Risk actors have started to use the Tox peer-to-peer instantaneous messaging company as a command-and-control technique, marking a change from its before role as a call strategy for ransomware negotiations.
The results from Uptycs, which analyzed an Executable and Linkable Format (ELF) artifact (“72consumer”) that functions as a bot and can run scripts on the compromised host applying the Tox protocol.
Tox is a serverless protocol for on the internet communications that presents end-to-stop encryption (E2EE) protections by producing use of the Networking and Cryptography library (NaCl, pronounced “salt”) for encryption and authentication.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“The binary observed in the wild is a stripped but dynamic executable, making decompilation a lot easier,” scientists Siddharth Sharma and Nischay Hedge mentioned. “The complete binary seems to be created in C, and has only statically joined the c-toxcore library.”
It truly is well worth noting that c-toxcore is a reference implementation of the Tox protocol.
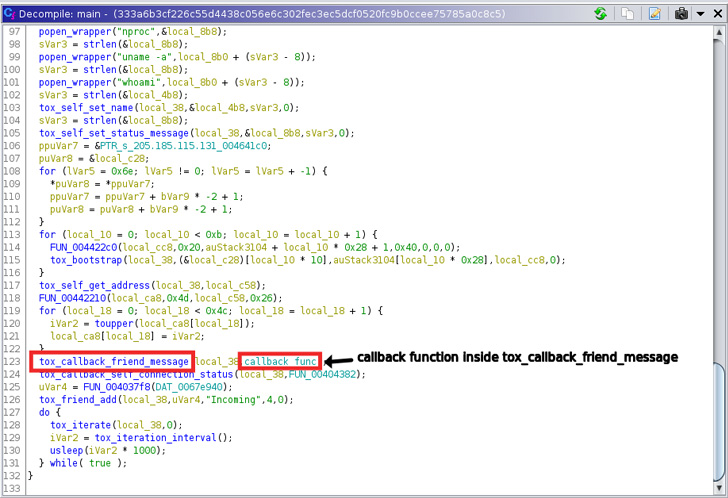
The reverse engineering carried out by Uptycs demonstrates that the ELF file is made to generate a shell script to the place “/var/tmp/” – a directory utilized for short term file generation in Linux – and start it, enabling it to run instructions to eliminate cryptominer relevant processes.
Also executed is a second plan that will allow it to operate a quantity of precise instructions (e.g., nproc, whoami, device-id, etcetera.) on the procedure, the benefits of which are subsequently sent about UDP to a Tox receiver.

In addition, the binary arrives with capabilities to receive different instructions by way of Tox, primarily based on which the shell script is updated or receives executed on an ad-hoc foundation. An “exit” command issued quits the Tox link.
Tox has been historically utilized by ransomware actors as a interaction system, but the most recent improvement marks the first time the protocol is currently being employed to run arbitrary scripts on an infected equipment.
“Even though the reviewed sample does not do anything explicitly destructive, we feel that it could be a component of a coinminer marketing campaign,” the researchers explained. “Therefore, it turns into vital to watch the network elements involved in the attack chains.”
The disclosure also comes amid experiences that the decentralized file program option acknowledged as IPFS is remaining ever more employed for hosting phishing web pages in an effort and hard work to make takedowns far more hard.
Discovered this post appealing? Follow THN on Facebook, Twitter and LinkedIn to go through much more exclusive information we publish.
Some parts of this report are sourced from:
thehackernews.com


 War in Ukraine Has Pushed Two-Thirds of Businesses to Change Cyber Strategy
War in Ukraine Has Pushed Two-Thirds of Businesses to Change Cyber Strategy