Phishing strategies delivering malware people these as DarkGate and PikaBot are adhering to the identical practices beforehand employed in attacks leveraging the now-defunct QakBot trojan.
“These consist of hijacked email threads as the original an infection, URLs with special designs that limit consumer accessibility, and an infection chain virtually similar to what we have viewed with QakBot delivery,” Cofense explained in a report shared with The Hacker Information.
“The malware families used also follow suit to what we would hope QakBot affiliates to use.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

QakBot, also referred to as QBot and Pinkslipbot, was shut down as portion of a coordinated legislation enforcement hard work codenamed Procedure Duck Hunt before this August.
The use of DarkGate and PikaBot in these campaigns is not astonishing as they can both of those act as conduits to deliver further payloads to compromised hosts, earning them the two an interesting alternative for cybercriminals.
PikaBot’s parallels to QakBot were being formerly highlighted by Zscaler in its analysis of the malware in May 2023, noting similarities in the “distribution strategies, campaigns, and malware behaviors.”
DarkGate, for its element, incorporates sophisticated tactics to evade detection by antivirus units, together with capabilities to log keystrokes, execute PowerShell, and put into action a reverse shell that will allow its operators to commandeer an contaminated host remotely.
“The link is bidirectional, indicating the attackers can send out commands and receive responses in real-time, enabling them to navigate the victim’s process, exfiltrate information, or perform other malicious actions,” Sekoia claimed in a new complex report of the malware.

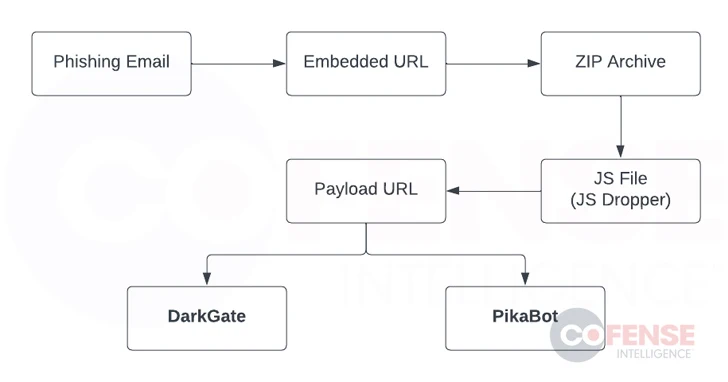
Cofense’s analysis of the higher-quantity phishing campaign shows that it targets a vast assortment of sectors, with the attack chains propagating a booby-trapped URL pointing to a ZIP archive in hijacked email threads.
The ZIP archive has a JavaScript dropper that, in flip, contacts a 2nd URL to obtain and operate either the DarkGate or PikaBot malware.
A noteworthy variant of the attacks has been noticed having benefit of Excel include-in (XLL) information in lieu of JavaScript droppers to produce the ultimate payloads.
“A effective DarkGate or PikaBot infection could direct to the delivery of innovative crypto mining software, reconnaissance tools, ransomware, or any other malicious file the risk actors would like to put in on a victim’s device,” Cofense said.
Observed this write-up appealing? Follow us on Twitter and LinkedIn to go through more distinctive information we article.
Some pieces of this post are sourced from:
thehackernews.com


 Why Defenders Should Embrace a Hacker Mindset
Why Defenders Should Embrace a Hacker Mindset