Cybersecurity scientists have in-depth a “extreme design flaw” in Google Workspace’s domain-extensive delegation (DWD) attribute that could be exploited by risk actors to facilitate privilege escalation and acquire unauthorized accessibility to Workspace APIs without the need of tremendous admin privileges.
“Such exploitation could end result in theft of emails from Gmail, information exfiltration from Google Push, or other unauthorized actions within just Google Workspace APIs on all of the identities in the concentrate on domain,” cybersecurity agency Hunters mentioned in a technological report shared with The Hacker Information.
The style weak point – which continues to be lively to this day – has been codenamed DeleFriend for its ability to manipulate present delegations in the Google Cloud Platform (GCP) and Google Workspace without having possessing super admin privileges.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Domain-wide delegation, per Google, is a “powerful characteristic” that makes it possible for third-party and internal apps to access users’ data throughout an organization’s Google Workspace environment.

The vulnerability is rooted in the point that a domain delegation configuration is identified by the service account resource identifier (OAuth ID), and not the particular non-public keys linked with the services account id object.
As a end result, probable threat actors with significantly less privileged accessibility to a focus on GCP venture could “create various JSON web tokens (JWTs) composed of distinct OAuth scopes, aiming to pinpoint thriving mixtures of private crucial pairs and approved OAuth scopes which indicate that the assistance account has area-huge delegation enabled.”
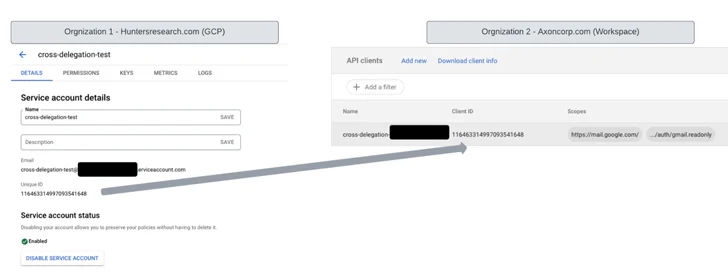
To put it in different ways, an IAM identity that has entry to generate new private keys to a related GCP assistance account source that has existing domain-broad delegation authorization can be leveraged to create a fresh new private essential, which can be used to carry out API calls to Google Workspace on behalf of other identities in the area.
Profitable exploitation of the flaw could enable exfiltration of delicate info from Google companies like Gmail, Travel, Calendar, and others. Hunters has also created accessible a evidence-of-strategy (PoC) that can be utilized to detect DWD misconfigurations.
“The likely penalties of destructive actors misusing domain-broad delegation are extreme,” Hunters security researcher Yonatan Khanashvili claimed. “As a substitute of influencing just a single id, as with individual OAuth consent, exploiting DWD with present delegation can impact each individual identification inside the Workspace area.
Located this article appealing? Abide by us on Twitter and LinkedIn to read a lot more distinctive information we put up.
Some pieces of this post are sourced from:
thehackernews.com


 How Hackers Phish for Your Users’ Credentials and Sell Them
How Hackers Phish for Your Users’ Credentials and Sell Them