There is been a fantastic offer of AI hoopla a short while ago, but that does not mean the robots are in this article to change us. This post sets the report straight and explains how businesses really should tactic AI.
From musing about self-driving autos to fearing AI bots that could wipe out the world, there has been a great offer of AI hoopla in the previous several yrs. AI has captured our imaginations, goals, and from time to time, our nightmares. Even so, the fact is that AI is currently significantly less sophisticated than we anticipated it would be by now. Autonomous automobiles, for instance, generally regarded as the poster kid of AI’s limitless potential, signify a slim use circumstance and are not however a widespread application throughout all transportation sectors.
In this article, we de-hype AI, provide resources for firms approaching AI and share facts to support stakeholders educate themselves.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
AI Terminology De-Hyped
AI vs. ML
AI (Synthetic Intelligence) and ML (Machine Understanding) are conditions that are often utilized interchangeably, but they depict diverse concepts. AI aims to create intelligence, which suggests cognitive talents and the capacity to pass the Turing check. It operates by getting what it has realized and elevating it to the up coming stage. The objective of making use of AI is to replicate human actions, this kind of as creating a cleaning robot that operates in a fashion very similar to a human cleaner.
ML is a subset of AI. It comprises mathematical types and its abilities are based mostly on combining machines with data. ML will work by discovering lessons from gatherings and then prioritizing people lessons. As a result, ML can complete steps that human beings can not, like likely above large reams of info, figuring out designs, predicting probabilities, and far more.
Slender vs. Basic AI
The thought of Standard AI is the one particular that normally scares most people today, because it really is the epitome of our “robot overlords” changing human beings. On the other hand, though this plan is technically probable, we are not at that phase suitable now.
In contrast to General AI, Slender AI is a specialised type of AI that is tuned for really certain duties. This emphasis makes it possible for supporting individuals, relieving us from operate that is much too demanding or possibly damaging. It is not intended to switch us. Slim AI is now becoming used throughout industries, like for setting up cars and trucks or packaging boxes. In cybersecurity, Narrow AI can review action data and logs, seeking for anomalies or indicators of an attack.
AI and ML in the Wild
There are three widespread models of AI and ML in the wild: generative AI, supervised ML and unsupervised ML.
Generative AI
Generative AI is a slicing-edge subject in AI, characterized by models, like LLMs, that are experienced on a corpus of awareness. The generative AI technology has the skill to create new articles primarily based on the facts contained within that corpus. Generative AI has been explained as a variety of “autocorrect” or “style forward,” but on steroids. Illustrations of Generative AI applications include things like ChatGPT, Bing, Bard, Dall-E, and specialised cyber assistants, like IBM Security QRadar Advisor with Watson or MSFT Security CoPilot.
Generative AI is finest suited for use scenarios like brainstorming, assisted copyediting and conducting analysis against a trusted corpus. Cybersecurity gurus, like SOC and fusion groups, can leverage Generative AI for investigate, to enable them comprehend zero-day vulnerabilities, network topologies, or new indicators of compromise (IoC). It can be critical to figure out that Generative AI often makes “hallucinations”, i.e. completely wrong solutions.
Cyber Security Learn Class: Episode 13All the things You Required To Know About AI Security But Were being Concerned To Inquire
In this session, we will go beyond the hype and come across out if and how AI impacts your cybersecurity system.
Look at Now
In accordance to Etay Maor, Senior Director Security Tactic at Cato Networks, “Generative AI can also assistance criminals. For instance, they can use it to generate phishing e-mails. Before ChatGPT, one particular of the primary detections of phishing emails was spelling problems and negative grammar. All those ended up indicators that one thing was suspicious. Now, criminals can conveniently publish a phishing email in several languages in excellent grammar.”
Unsupervised Studying
Unsupervised understanding in ML indicates that the teaching data and the outcomes are not labeled. This method lets algorithms to make inferences from facts with out human intervention, to come across designs, clusters and connections. Unsupervised understanding is commonly employed for dynamic tips, like in retail web sites.
In cybersecurity, unsupervised finding out can be utilized for clustering or grouping and for locating designs that were not clear ahead of, for case in point it can assist establish all malware with a specific signature originating from a precise country-state. It can also uncover associations and one-way links concerning information sets. For illustration, identifying if persons who click on phishing email messages are a lot more possible to reuse passwords. Yet another use situation is anomaly detection, like detecting exercise that could possibly indicate an attacker is applying stolen qualifications.
Unsupervised learning is not generally the suitable alternative. When receiving the output wrong has a very higher effects and serious effects, when quick schooling times are wanted, or when total transparency is needed, it really is suggested to acquire a different approach.
Supervised Finding out
In supervised understanding, the instruction facts is labeled with enter/output pairs, and the model’s accuracy relies upon on the good quality of labeling and dataset completeness. Human intervention is typically required to evaluation the output, enhance precision,and appropriate any bias drift. Supervised discovering is very best suited for producing predictions.
In cybersecurity, supervised mastering is used for classification, which can assist establish phishing and malware. It can also be utilized for regression, like predicting the value of a novel attack primarily based on earlier incident fees.
Supervised discovering is not the very best healthy if there is certainly no time to prepare or no a single to label or teach the info. It really is also not proposed when there is a will need to evaluate significant amounts of details, when there is not sufficient data, or when automatic classification/clustering is the finish objective.
Reinforcement Studying (RL)
Reinforcement Understanding (RL) occupies a space concerning completely supervised and unsupervised discovering and is a special solution to ML. It indicates retraining a product when present schooling fails to foresee particular use instances. Even deep mastering, with its access to significant datasets, can nevertheless pass up outlier use circumstances that RL can tackle. The incredibly existence of RL is an implicit admission that models can be flawed.
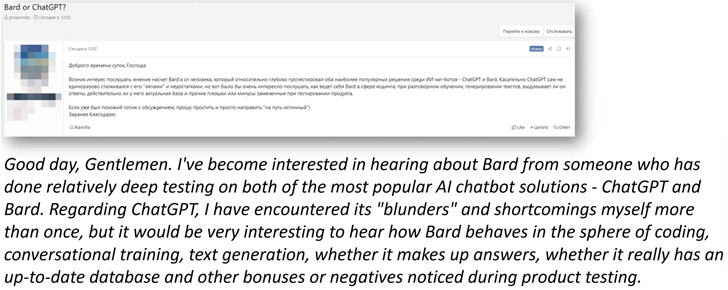
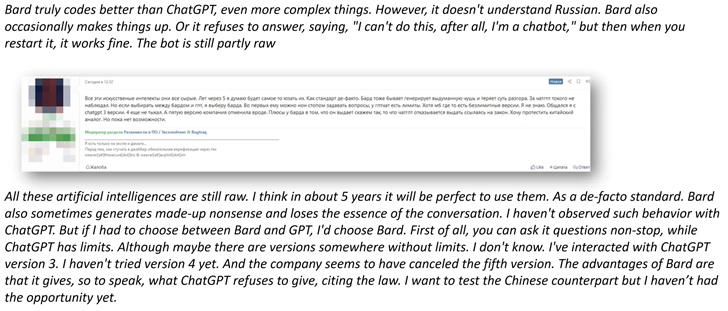
What Cybercriminals are Declaring About Generative AI
Generative AI is of desire to cyber criminals. In accordance to Etay Maor “Cyber criminals have been talking about how to use ChatGPT, Bard and other GenAI apps from the day they were introduced, as perfectly as sharing their practical experience and feelings about their capabilities. As it would seem, they consider that GenAI has restrictions and will probably be more mature for attacker use in a several many years.”
Some conversation illustrations consist of:
The Artificial Intelligence Risk Administration Framework (AI RMF) by NIST
When engaging with AI and AI-primarily based answers, it really is important to recognize AI’s restrictions, hazards and vulnerabilities. The Synthetic Intelligence Risk Administration Framework (AI RMF) by NIST is a set of tips and very best procedures intended to aid organizations recognize, evaluate and manage the dangers affiliated with the deployment and use of artificial intelligence technologies.
The framework is composed of 6 components:
Extra methods for running AI risk incorporate the MITRE ATLAS (Adversarial Menace Landscape for Artificial-Intelligence Programs), OWASP Best 10 for ML and Google’s Safe AI Framework (SAIF).
Issues to Request Your Vendor
In the close to long run, it will be extremely popular for suppliers to provide generative AI abilities. Here is a checklist of queries to inquire to aid your educated decision.
1. What and Why?
What are the AI capabilities and why are they needed? For instance, GenAI is very good at producing e-mail, so GenAI makes feeling for an email system. What’s the use scenario for the vendor?
2. Coaching facts
Training information demands to be effectively and correctly managed, if not it can produce bias. It truly is vital to check with about the forms of teaching info, how it has been cleaned, how it is managed, etc.
3. Was resilience crafted-in?
Has the seller taken into thought that cybercriminals are attacking the system by itself and implemented security controls?
4. Real ROI vs. Statements
What is the ROI and does the ROI justify employing AI or ML (or were being they extra for the reason that of the buzz and for income applications)?
5. Is it Genuinely Solving a Trouble?
The most essential dilemma – is the AI resolving your problem and is it performing it perfectly? You can find no position in having to pay a premium and incurring added overhead unless the AI is fixing the difficulty and performing the way it really should.
AI can empower us and assist us execute much better, but it is not a silver bullet. That is why it really is crucial for businesses to make educated choices about instruments with AI they select to apply internally.
To master additional about AI and ML use circumstances, dangers, programs, vulnerabilities and implications for security gurus, view the overall masterclass below.
Identified this short article intriguing? Comply with us on Twitter and LinkedIn to read much more exclusive content we put up.
Some elements of this article are sourced from:
thehackernews.com

 Vietnamese Cybercriminals Targeting Facebook Business Accounts with Malvertising
Vietnamese Cybercriminals Targeting Facebook Business Accounts with Malvertising