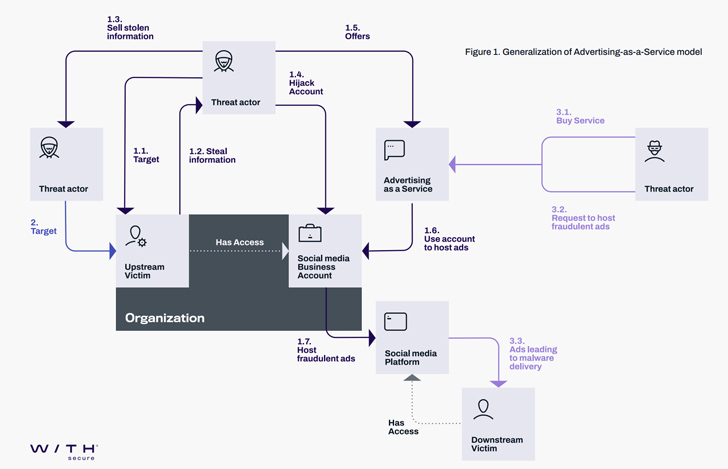
Destructive actors affiliated with the Vietnamese cybercrime ecosystem are leveraging marketing-as-a-vector on social media platforms these types of as Meta-owned Facebook to distribute malware.
“Menace actors have extensive employed fraudulent adverts as a vector to goal victims with frauds, malvertising, and a lot more,” WithSecure researcher Mohammad Kazem Hassan Nejad claimed. “And with companies now leveraging the reach of social media for marketing, attackers have a new, highly-beneficial type of attack to add to their arsenal – hijacking organization accounts.”
Cyber attacks focusing on Meta Organization and Fb accounts have attained attractiveness around the previous year, courtesy of exercise clusters these as Ducktail and NodeStealer that are recognised to raid companies and people today working on Fb.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Between the strategies employed by cybercriminals to obtain unauthorized entry to consumer accounts, social engineering performs a major part.
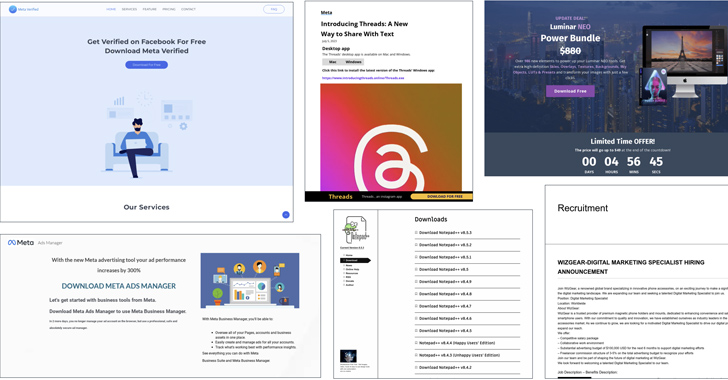
Victims are approached by means of several platforms ranging from Facebook and LinkedIn to WhatsApp and freelance occupation portals like Upwork. An additional known distribution system is the use of search motor poisoning to increase bogus software program this kind of as CapCut, Notepad++, OpenAI ChatGPT, Google Bard, and Meta Threads.
An component which is typical to these groups is the abuse of URL shortener products and services, Telegram for command-and-management (C2), and legit cloud companies like Trello, Discord, Dropbox, iCloud, OneDrive, and Mediafire to host the destructive payloads.

The actors driving Ducktail, for occasion, leverage lures associated to model and advertising tasks to infiltrate folks and companies that work on Meta’s Organization platform, with new attack waves employing task and recruitment-associated themes to activate the infection.
In these attacks, possible targets are directed to bogus postings on Upwork and Freelancer by way of Facebook ads or LinkedIn InMail, which, in flip, incorporate a connection to a booby-trapped position description file hosted on a single of the aforementioned cloud storage providers, eventually leading to the deployment of the Ducktail stealer malware.
“Ducktail malware steals saved session cookies from browsers, with code specifically customized to choose over Fb business accounts,” Zscaler ThreatLabz scientists Sudeep Singh and Naveen Selvan noted in a parallel evaluation, stating the accounts offer for anyplace involving $15 to $340.
“The ‘products’ of the operation (i.e. hacked social media accounts) feed an underground financial system of stolen social media accounts, where a lot of vendors offer accounts priced according to their perceived usefulness for malicious exercise.”
Decide on infection sequences observed concerning February and March 2023 have included the use of shortcut and PowerShell files to down load and launch the final malware, illustrating the attackers’ ongoing evolution of their techniques.
The experimentation also extends to the stealer, which has been current to harvest a user’s personal info from X (previously Twitter), TikTok Business enterprise, and Google Ads, as nicely as leverage the stolen Fb session cookies to produce fraudulent adverts in an automated fashion and acquire elevated privileges to execute other steps.
A principal technique applied to takeover a victim’s compromised account is by incorporating their have email deal with to that account, subsequently modifying the password and email address of the victim’s Fb account to lock them out of the support.
“One more new element noticed in Ducktail samples since (at least) July 2023 is utilizing RestartManager (RM) to eliminate procedures that lock browser databases,” WithSecure reported. “This ability is typically uncovered in ransomware as data files that are in-use by processes or solutions simply cannot be encrypted.”
What is actually more, the closing payload is obscured utilizing a loader to decrypt and execute it dynamically at runtime in what is actually seen as an endeavor to incorporate procedures aimed at increasing evaluation complexity and detection evasion.
Some of the other solutions adopted by the threat actor to hinder examination encompass the use of uniquely generated assembly names and the reliance on SmartAssembly, bloating, and compression to obfuscate the malware.
Zscaler reported it spotted cases where by the team initiated get in touch with by using compromised LinkedIn accounts that belonged to users performing in the electronic advertising and marketing house, some of whom had extra than 500 connections and 1,000 followers.
Approaching WEBINARDetect, Respond, Safeguard: ITDR and SSPM for Full SaaS Security
Learn how Identification Threat Detection & Response (ITDR) identifies and mitigates threats with the aid of SSPM. Understand how to secure your company SaaS programs and safeguard your information, even soon after a breach.
Supercharge Your Abilities
“The large amount of money of connections/followers assisted lend authenticity to the compromised accounts and facilitated the social engineering process for menace actors,” the scientists mentioned.
This also highlights the worm-like propagation of Ducktail wherein LinkedIn credentials and cookies stolen from a consumer who fell victim to the malware attack is utilized to login to their accounts and contact other targets and broaden their achieve.
Ducktail is explained to be one particular of the a lot of Vietnamese threat actors who are leveraging shared tooling and strategies to pull off these types of fraudulent techniques. This also includes a Ducktail copycat dubbed Duckport, which has been active considering the fact that late March 2023 and performs information thieving together with Meta Company account hijacking.
It is really worthy of pointing out that the marketing campaign that Zscaler is monitoring as Ducktail is in point Duckport, which, in accordance to WithSecure, is a individual menace owing to the variations in the Telegram channels utilised for C2, the source code implementation, and the reality that the two the strains have hardly ever been dispersed collectively.
“Though Ducktail has dabbled with the usage of faux branded web-sites as element of their social engineering efforts, it has been a frequent technique for Duckport,” WithSecure stated.
“Rather of offering immediate obtain one-way links to file hosting providers these as Dropbox (which may increase suspicion), Duckport sends victims links to branded web pages that are relevant to the brand name/company they’re impersonating, which then redirects them to download the destructive archive from file hosting services (these types of as Dropbox).”
Duckport, while primarily based on Ducktail, also comes with novel options that expand on the information and facts thieving and account hijacking capabilities, and also choose screenshots or abuse on the internet note-taking companies as element of its C2 chain, effectively replacing Telegram as a channel to pass instructions to the victim’s machine.
“The Vietnamese-centric component of these threats and large degree of overlaps in phrases of capabilities, infrastructure, and victimology indicates lively performing interactions amongst various threat actors, shared tooling and TTPs across these danger teams, or a fractured and services-oriented Vietnamese cybercriminal ecosystem (akin to ransomware-as-a-support model) centered about social media platforms these as Fb.”
Observed this article intriguing? Stick to us on Twitter and LinkedIn to read through extra exclusive content material we put up.
Some pieces of this article are sourced from:
thehackernews.com

 Beware of MalDoc in PDF: A New Polyglot Attack Allowing Attackers to Evade Antivirus
Beware of MalDoc in PDF: A New Polyglot Attack Allowing Attackers to Evade Antivirus