Cybersecurity researchers have unearthed a new piece of evasive malware dubbed Beep that’s designed to fly beneath the radar and fall further payloads on to a compromised host.
“It appeared as if the authors of this malware were striving to carry out as a lot of anti-debugging and anti-VM (anti-sandbox) techniques as they could uncover,” Minerva Labs researcher Natalie Zargarov stated.
“A single this kind of method involved delaying execution by the use of the Beep API functionality, as a result the malware’s identify.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
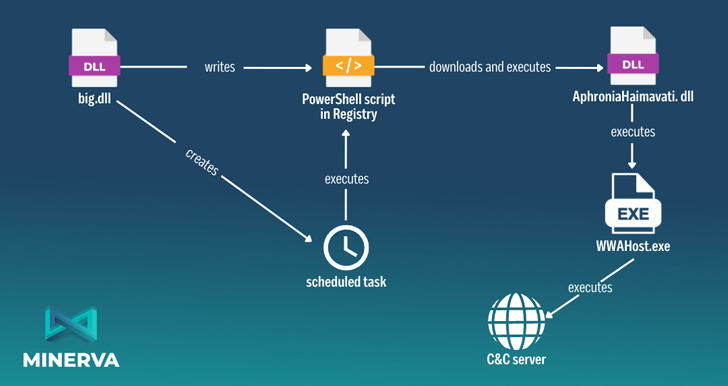
Beep comprises a few elements, the to start with of which is a dropper which is dependable for generating a new Windows Registry key and executing a Base64-encoded PowerShell script saved in it.
The PowerShell script, for its portion, reaches out to a distant server to retrieve an injector, which, following confirming it can be not currently being debugged or released in a virtual equipment, extracts and launches the payload via a technique identified as system hollowing.
The payload is an information and facts stealer which is outfitted to acquire and exfiltrate process facts and enumerate functioning procedures. Other guidance the malware is able of accepting from a command-and-command (C2) server consist of the skill to execute DLL and EXE information.
A variety of other attributes are still to be executed, suggesting that Beep is nonetheless in its early phases of enhancement.
What sets the rising malware aside is its significant concentrate on stealth, adopting a sheer quantity of detection evasion solutions in an attempt to resist investigation, stay away from sandboxes, and delay execution.
“Once this malware productively penetrates a technique, it can effortlessly download and spread a wide assortment of supplemental destructive resources, such as ransomware, building it incredibly hazardous,” Zargarov observed.
The conclusions appear as antivirus vendor Avast disclosed specifics of yet another dropper strain codenamed NeedleDropper that has been employed to distribute distinctive malware family members considering the fact that October 2022.
Shipped by using spam email attachments, Discord, or OneDrive URLs, the malware is suspected to be supplied as a service for other legal actors wanting to distribute their have payloads.
“The malware tries to conceal alone by dropping lots of unused, invalid data files and stores essential details involving a number of MB of unimportant data, and also makes use of reputable apps to accomplish its execution,” the organization explained.
Located this article intriguing? Abide by us on Twitter and LinkedIn to read far more distinctive content material we submit.
Some elements of this short article are sourced from:
thehackernews.com


 Cyber security certification vs degree: Which is best for your career?
Cyber security certification vs degree: Which is best for your career?