Google has unveiled a new pilot software in Singapore that aims to reduce users from sideloading specified applications that abuse Android application permissions to browse one-time passwords and collect sensitive data.
“This increased fraud security will evaluate and automatically block the set up of applications that may use sensitive runtime permissions usually abused for financial fraud when the user attempts to put in the app from an Internet-sideloading source (web browsers, messaging applications or file administrators),” the enterprise reported.
The feature is intended to study the permissions declared by a 3rd-party application in actual-time and search for people that seek to acquire access to sensitive permissions connected with looking at SMS messages, deciphering or dismissing notifications from legit applications, and accessibility services that have been routinely abused by Android-centered malware for extracting useful data.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

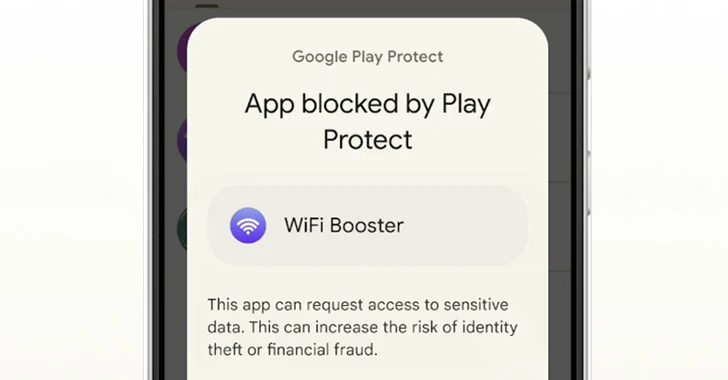
As part of the test, people in Singapore who endeavor to sideload these types of applications (or APK information) will be blocked from accomplishing so by way of Google Enjoy Safeguard and exhibited a pop-up information that reads: “This application can request entry to sensitive info. This can increase the risk of identification theft or monetary fraud.”
“These permissions are routinely abused by fraudsters to intercept 1-time passwords via SMS or notifications, as properly as spy on-monitor content,” Eugene Liderman, director of the cell security approach at Google, reported.
The adjust is portion of a collaborative work to overcome cell fraud, the tech big said, urging app developers to follow greatest tactics and evaluate their apps’ device permissions to ensure it does not violate the Cellular Unwanted Program concepts.
Google, which released Google Engage in Safeguard genuine-time scanning at the code level to detect novel Android malware in pick markets like India, Thailand, Singapore, and Brazil, explained the energy allowed it to detect 515,000 new destructive applications and that it issued no significantly less than 3.1 million warnings or blocks of people applications.
The improvement also arrives as Apple introduced sweeping adjustments to the App Retailer in the European Union to comply with the Electronic Markets Act (DMA) in advance of the March 6, 2024, deadline. The changes, together with Notarization for iOS apps, are expected to go are living with iOS 17.4.

The iPhone maker, however, repeatedly emphasised that distributing iOS apps from choice app marketplaces exposes E.U. customers to “amplified privacy and security threats,” and that it does not intend to provide them to other locations.
“This contains new avenues for malware, fraud and scams, illicit and unsafe material, and other privacy and security threats,” Apple mentioned. “These adjustments also compromise Apple’s capability to detect, avoid, and consider action in opposition to malicious applications on iOS and to aid people impacted by issues with applications downloaded outside of the App Retail store.”
Located this report attention-grabbing? Comply with us on Twitter and LinkedIn to study additional distinctive content we article.
Some components of this short article are sourced from:
thehackernews.com

 Kimsuky’s New Golang Stealer ‘Troll’ and ‘GoBear’ Backdoor Target South Korea
Kimsuky’s New Golang Stealer ‘Troll’ and ‘GoBear’ Backdoor Target South Korea