The North Korea-joined country-state actor identified as Kimsuky is suspected of making use of a formerly undocumented Golang-dependent info stealer known as Troll Stealer.
The malware steals “SSH, FileZilla, C push information/directories, browsers, procedure facts, [and] display captures” from contaminated systems, South Korean cybersecurity business S2W said in a new technological report.
Troll Stealer’s links to Kimsuky stem from its similarities to acknowledged malware people, such as AppleSeed and AlphaSeed malware that have been attributed to the team.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Kimsuky, also tracked beneath the names APT43, ARCHIPELAGO, Black Banshee, Emerald Sleet (earlier Thallium), Nickel Kimball, and Velvet Chollima, is well identified for its propensity to steal delicate, private details in offensive cyber operations.
In late November 2023, the threat actors had been sanctioned by the U.S. Treasury Department’s Place of work of Overseas Property Command (OFAC) for gathering intelligence to additional North Korea’s strategic objectives.
The adversarial collective, in latest months, has been attributed to spear-phishing attacks focusing on South Korean entities to deliver a selection of backdoors, like AppleSeed and AlphaSeed.
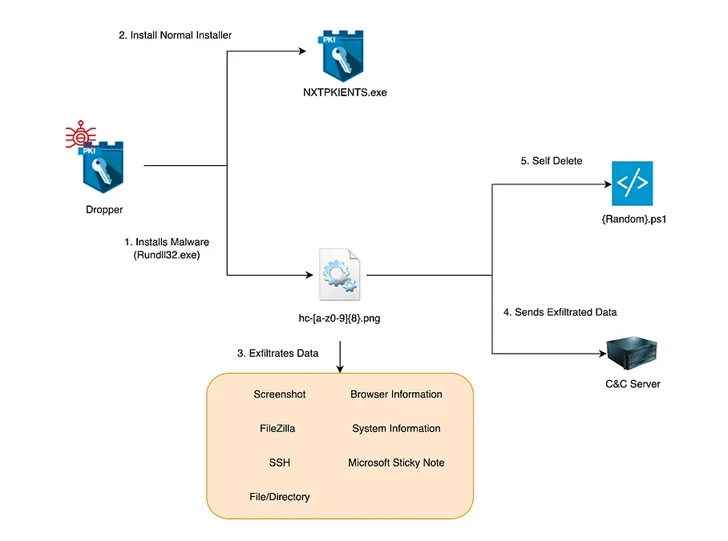
S2W’s hottest examination reveals the use of a dropper that masquerades as a security plan installation file from a South Korean business named SGA Solutions to launch the stealer, which will get its name from the route “D:/~/repo/golang/src/root.go/s/troll/agent” which is embedded in it.
“The dropper runs as a legit installer alongside the malware, and the two the dropper and malware are signed with a legitimate, authentic D2Innovation Co.,LTD’ certification, suggesting that the company’s certification was actually stolen,” the company reported.
A stand-out aspect of Troll Stealer is its means to pilfer the GPKI folder on contaminated techniques, elevating the probability that the malware has been put to use in attacks focusing on administrative and public companies in the nation.

Provided the absence of Kimsuky campaigns documenting the theft of GPKI folders, it has elevated the chance that the new actions is possibly a shift in methods or the perform of an additional risk actor intently associated with the group that also has obtain to the source code of AppleSeed and AlphaSeed.
There are also symptoms that the threat actor may well be associated with a Go-based mostly backdoor codenamed GoBear which is also signed with a authentic certificate associated with D2Innovation Co., LTD and executes guidance acquired from a command-and-manage (C2) server.
“The strings contained in the names of the functions it calls have been discovered to overlap with the instructions used by BetaSeed, a C++-centered backdoor malware applied by the Kimsuky team,” S2W reported. “It is noteworthy that GoBear provides SOCKS5 proxy functionality, which was not previously supported by the Kimsuky group’s backdoor malware.”
Found this report fascinating? Comply with us on Twitter and LinkedIn to study extra exclusive written content we publish.
Some elements of this report are sourced from:
thehackernews.com

 Critical Patches Released for New Flaws in Cisco, Fortinet, VMware Products
Critical Patches Released for New Flaws in Cisco, Fortinet, VMware Products