A quantity of state-again danger actors from Russia and China have been noticed exploiting a the latest security flaw in the WinRAR archiver tool for Windows as element of their operations.
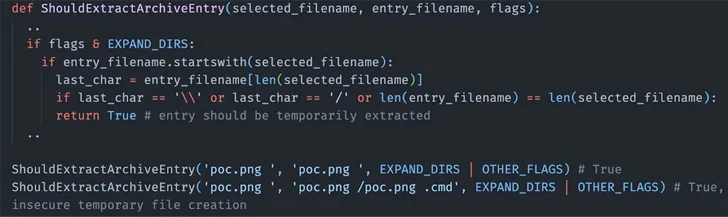
The vulnerability in question is CVE-2023-38831 (CVSS score: 7.8), which makes it possible for attackers to execute arbitrary code when a person makes an attempt to check out a benign file in just a ZIP archive. The shortcoming has been actively exploited due to the fact at least April 2023.
Google Threat Evaluation Team (TAG), which detected the pursuits in the latest weeks, attributed them to a few unique clusters it tracks beneath the geological monikers FROZENBARENTS (aka Sandworm), FROZENLAKE (aka APT28), and ISLANDDREAMS (aka APT40).

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The phishing attack joined to Sandworm impersonated a Ukrainian drone warfare coaching college in early September and dispersed a destructive ZIP file exploiting CVE-2023-38831 to deliver Rhadamanthys, a commodity stealer malware which is made available for sale for $250 for a every month membership.
APT28, also affiliated with the Key Directorate of the Common Personnel of the Armed Forces of the Russian Federation (GRU) as it is really the situation with Sandworm, is stated to have introduced an email marketing campaign focusing on federal government businesses in Ukraine.
In these attacks, buyers from Ukraine were being prompted to down load a file made up of a CVE-2023-38831 exploit – a decoy doc that masqueraded as an function invitation from Razumkov Centre, a community plan consider tank in the region.
The end result is the execution of a PowerShell script named IRONJAW that steals browser login knowledge and local state directories and exports the info to an actor-managed infrastructure on webhook[.]web page.
The third threat actor to exploit the WinRAR bug is APT40, which unleashed a phishing campaign focusing on Papua New Guinea in which the email messages bundled a Dropbox website link to a ZIP archive that contains the CVE-2023-38831 exploit.
The infection sequence in the end paved the way for the deployment of a dropper named ISLANDSTAGER that is accountable for loading BOXRAT, a .NET backdoor that takes advantage of the Dropbox API for command-and-command
The disclosure builds on current conclusions from Cluster25, which in-depth attacks undertaken by the APT28 hacking crew exploiting the WinRAR flaw to conduct credential harvesting operations.

Some of the other condition-sponsored adversaries that have joined the fray are Konni (which shares overlaps with a North Korean cluster tracked as Kimsuky) and Dark Pink (aka Saaiwc Group), in accordance to findings from the Knownsec 404 staff and NSFOCUS.
“The common exploitation of the WinRAR bug highlights that exploits for known vulnerabilities can be extremely helpful, even with a patch becoming accessible,” TAG researcher
Kate Morgan said. “Even the most complex attackers will only do what is essential to complete their ambitions.”
Uncovered this article fascinating? Stick to us on Twitter and LinkedIn to read additional unique content material we article.
Some areas of this report are sourced from:
thehackernews.com


 Lazarus Group Targeting Defense Experts with Fake Interviews via Trojanized VNC Apps
Lazarus Group Targeting Defense Experts with Fake Interviews via Trojanized VNC Apps