A North Korean authorities-backed danger actor has been linked to attacks concentrating on governing administration and military staff, believe tanks, coverage makers, teachers, and researchers in South Korea and the U.S.
Google’s Danger Evaluation Team (TAG) is monitoring the cluster under the title ARCHIPELAGO, which it reported is a subset of another danger group tracked by Mandiant less than the title APT43.
The tech large said it began monitoring the group in 2012, incorporating it has “noticed the team target men and women with experience in North Korea plan issues these kinds of as sanctions, human rights, and non-proliferation issues.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The priorities of APT43, and by extension ARCHIPELAGO, are stated to align with North Korea’s Reconnaissance Standard Bureau (RGB), the most important foreign intelligence provider, suggesting overlaps with a team broadly recognised as Kimsuky.
Attack chains mounted by ARCHIPELAGO require the use of phishing e-mail made up of malicious backlinks that, when clicked by the recipients, redirect to phony login internet pages that are developed to harvest qualifications.
These messages purport to be from media shops and consider tanks and look for to entice targets underneath the pretext of requesting for interviews or extra information about North Korea.
“ARCHIPELAGO invests time and effort and hard work to create a rapport with targets, often corresponding with them by email above numerous times or months in advance of at last sending a malicious connection or file,” TAG reported.
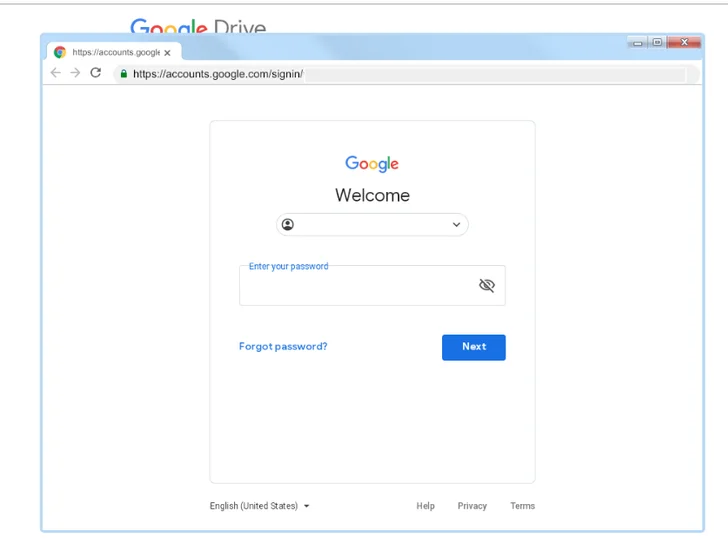
The menace actor is also recognised to utilize the browser-in-the-browser (BitB) approach to render rogue login internet pages within an real window to steal qualifications.
What is much more, the phishing messages have posed as Google account security alerts to activate the an infection, with the adversarial collective hosting malware payloads like BabyShark on Google Travel in the type of blank information or ISO optical disc photographs.
Upcoming WEBINARLearn to Protected the Identification Perimeter – Verified Procedures
Strengthen your small business security with our approaching specialist-led cybersecurity webinar: Explore Id Perimeter procedures!
Do not Miss out on Out – Help save Your Seat!
A further noteworthy method adopted by ARCHIPELAGO is the use of fraudulent Google Chrome extensions to harvest delicate information, as evidenced in prior strategies dubbed Stolen Pencil and SharpTongue.
The improvement arrives as AhnLab Security Unexpected emergency Reaction Heart (ASEC) detailed Kimsuky’s use of Alternate Knowledge Stream (Advertisements) and weaponized Microsoft Term documents to provide facts-stealer malware.
Found this posting interesting? Comply with us on Twitter and LinkedIn to read additional exceptional content material we submit.
Some elements of this posting are sourced from:
thehackernews.com


 Protect Your Company: Ransomware Prevention Made Easy
Protect Your Company: Ransomware Prevention Made Easy