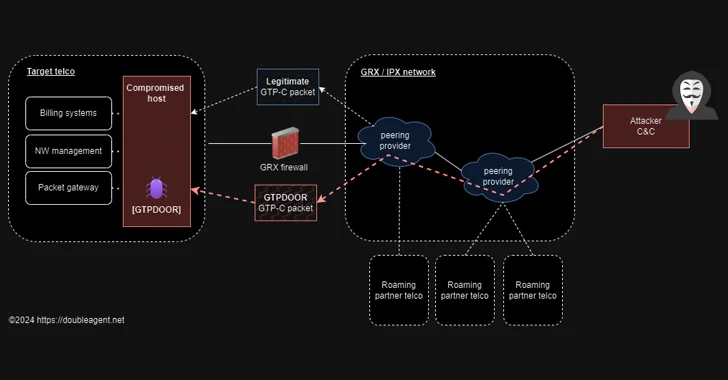
Menace hunters have found a new Linux malware termed GTPDOOR which is made to be deployed in telecom networks that are adjacent to GPRS roaming exchanges (GRX)
The malware is novel in the reality that it leverages the GPRS Tunnelling Protocol (GTP) for command-and-manage (C2) communications.
GPRS roaming enables subscribers to accessibility their GPRS services even though they are past the attain of their dwelling cell network. This is facilitated by signifies of a GRX that transports the roaming website traffic making use of GTP amongst the visited and the house General public Land Mobile Network (PLMN).

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Security researcher haxrob, who found out two GTPDOOR artifacts uploaded to VirusTotal from China and Italy, said the backdoor is likely joined to a acknowledged threat actor tracked as LightBasin (aka UNC1945), which was formerly disclosed by CrowdStrike in Oct 2021 in connection with a series of attacks concentrating on the telecom sector to steal subscriber data and connect with metadata.

“When run, the first factor GTPDOOR does is course of action-title stomps itself – shifting its approach title to ‘[syslog]’ – disguised as syslog invoked from the kernel,” the researcher explained. “It suppresses child alerts and then opens a uncooked socket [that] will allow the implant to receive UDP messages that hit the network interfaces.”
Set differently, GTPDOOR allows a risk actor that presently has recognized persistence on the roaming exchange network to get in touch with a compromised host by sending GTP-C Echo Ask for messages with a destructive payload.
This magic GTP-C Echo Request concept functions as a conduit to transmit a command to be executed on the infected device and return the results again to the remote host.

GTPDOOR “Can be covertly probed from an external network to elicit a reaction by sending a TCP packet to any port variety,” the researcher observed. “If the implant is active a crafted vacant TCP packet is returned alongside with details if the destination port was open up/responding on the host.”
“This implant seems like it is designed to sit on compromised hosts that directly contact the GRX network – these are the devices that communicate to other telecommunication operator networks through the GRX.”
Located this report appealing? Abide by us on Twitter and LinkedIn to examine a lot more special articles we submit.
Some components of this write-up are sourced from:
thehackernews.com

 Lazarus Hackers Exploited Windows Kernel Flaw as Zero-Day in Recent Attacks
Lazarus Hackers Exploited Windows Kernel Flaw as Zero-Day in Recent Attacks