Cybersecurity researchers have located a selection of GitHub repositories featuring cracked software that are made use of to deliver an information stealer known as RisePro.
The marketing campaign, codenamed gitgub, consists of 17 repositories associated with 11 diverse accounts, in accordance to G Info. The repositories in issue have given that been taken down by the Microsoft-owned subsidiary.
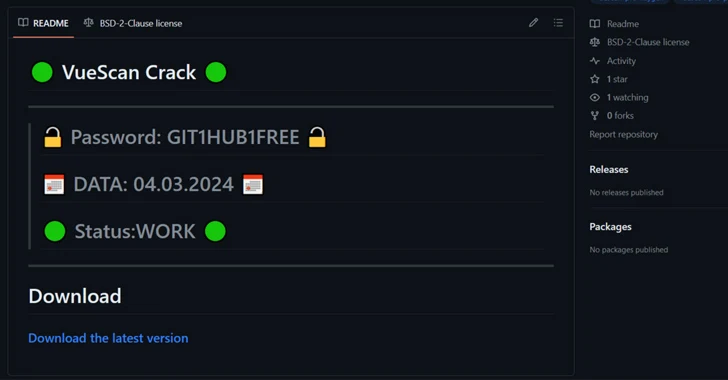
“The repositories look very similar, that includes a README.md file with the guarantee of totally free cracked program,” the German cybersecurity firm stated.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Environmentally friendly and crimson circles are normally used on Github to display the status of automated builds. Gitgub threat actors additional four eco-friendly Unicode circles to their README.md that faux to display a standing together with a recent date and deliver a perception of legitimacy and recency.”

The list of repositories is as follows, with just about every of them pointing to a download connection (“digitalxnetwork[.]com”) that contains a RAR archive file –
- andreastanaj/AVAST
- andreastanaj/Audio-Booster
- aymenkort1990/fabfilter
- BenWebsite/-IObit-Intelligent-Defrag-Crack
- Faharnaqvi/VueScan-Crack
- javisolis123/Voicemod
- lolusuary/AOMEI-Backupper
- lolusuary/Daemon-Tools
- lolusuary/EaseUS-Partition-Grasp
- lolusuary/SOOTHE-2
- mostofakamaljoy/ccleaner
- rik0v/ManyCam
- Roccinhu/Tenorshare-Reiboot
- Roccinhu/Tenorshare-iCareFone
- Accurate-Oblivion/AOMEI-Partition-Assistant
- vaibhavshiledar/droidkit
- vaibhavshiledar/TOON-Growth-HARMONY
The RAR archive, which calls for the victims to offer a password stated in the repository’s README.md file, incorporates an installer file, which unpacks the up coming-stage payload, an executable file that is inflated to 699 MB in an work to crash examination instruments like IDA Pro.
The real contents of the file – amounting to a mere 3.43 MB – act as a loader to inject RisePro (model 1.6) into both AppLaunch.exe or RegAsm.exe.
RisePro burst into the highlight in late 2022 when it was dispersed utilizing a spend-for every-put in (PPI) malware downloader service known as PrivateLoader.

Prepared in C++, it’s intended to collect delicate info from infected hosts and exfiltrate it to two Telegram channels, which are usually made use of by threat actors to extract victims’ details. Curiously, the latest exploration from Checkmarx showed that it truly is feasible to infiltrate and forward messages from an attacker’s bot to an additional Telegram account.
The development will come as Splunk specific the techniques and techniques adopted by Snake Keylogger, describing it as a stealer malware that “employs a multifaceted tactic to facts exfiltration.”
“The use of FTP facilitates the secure transfer of documents, when SMTP allows the sending of email messages containing sensitive data,” Splunk mentioned. “Furthermore, integration with Telegram presents a genuine-time interaction system, letting for quick transmission of stolen facts.”
Stealer malware have turn out to be more and more well known, usually turning into the principal vector for ransomware and other high affect knowledge breaches. According to a report from Specops printed this 7 days, RedLine, Vidar, and Raccoon have emerged as the most broadly-used stealers, with RedLine by itself accounting for the theft of a lot more than 170.3 million passwords in the last six months.
“The present rise of facts-stealing malware is a stark reminder of frequently evolving digital threats,” Flashpoint noted in January 2024. “Though the motivations behind its use is nearly always rooted in economical obtain, stealers are continuously adapting whilst currently being additional obtainable and less complicated to use.”
Observed this posting appealing? Adhere to us on Twitter and LinkedIn to browse a lot more unique content material we submit.
Some parts of this write-up are sourced from:
thehackernews.com

 GhostRace – New Data Leak Vulnerability Affects Modern CPUs
GhostRace – New Data Leak Vulnerability Affects Modern CPUs