The Iranian danger actor regarded as Domestic Kitten has been attributed to a new cellular marketing campaign that masquerades as a translation app to distribute an updated variant of an Android malware acknowledged as FurBall.
“Since June 2021, it has been dispersed as a translation app by way of a copycat of an Iranian internet site that offers translated article content, journals, and guides,” ESET researcher Lukas Stefanko claimed in a report shared with The Hacker News.
The updates, whilst retaining the exact same surveillance features as previously versions, are intended to evade detection by security alternatives, the Slovak cybersecurity agency additional.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Domestic Kitten, also called APT-C-50, is an Iranian threat activity cluster that has been earlier discovered as concentrating on men and women of interest with the intention of harvesting delicate details from compromised mobile units. It’s been acknowledged to be active given that at least 2016.

A tactical evaluation carried out by Development Micro in 2019 reveals Domestic Kitten’s prospective connections to a different team termed Bouncing Golf, a cyber espionage campaign focusing on Middle Jap international locations.
APT-C-50 has largely singled out “Iranian citizens that could pose a menace to the steadiness of the Iranian regime, which includes inside dissidents, opposition forces, ISIS advocates, the Kurdish minority in Iran, and much more,” in accordance to Verify Level.
Strategies carried out by the team have customarily relied on luring opportunity victims into installing a rogue application through different attack vectors, including Iranian weblog internet sites, Telegram channels, and SMS messages.
Irrespective of the approach used, the applications act as a conduit to supply a piece of malware codenamed by the Israeli cybersecurity business named Furball, a customized version of KidLogger which will come with abilities to assemble and exfiltrate personal information from the gadgets.
The latest iteration of the campaign uncovered by ESET requires the app functioning underneath the guise of a translation provider. Former handles employed to conceal destructive behavior span unique classes this kind of as security, news, online games, and wallpaper applications.
The application (“sarayemaghale.apk”) is delivered by using a phony web site mimicking downloadmaghaleh[.]com, a genuine internet site that offers content articles and publications translated from English to Persian.

What is actually notable about the most up-to-date variation is that although the main spyware features are retained, the artifact requests only one particular authorization to entry contacts, restricting it from accessing SMS messages, device site, contact logs, and clipboard knowledge.
“The explanation could be its aim to stay underneath the radar on the other hand, we also assume it could signal it is just the preceding period of a spear-phishing attack performed by means of text messages,” Stefanko pointed out.
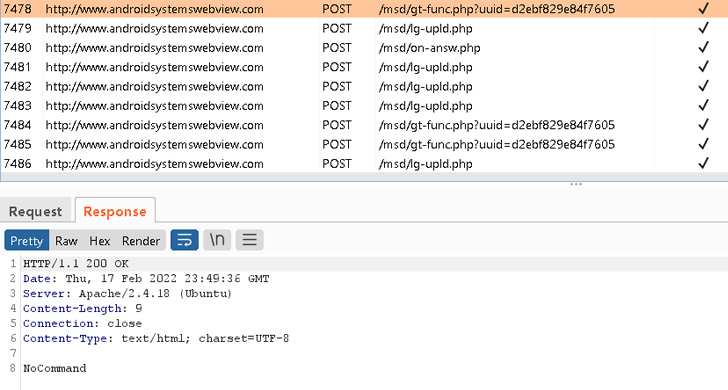
Inspite of this handicap, the Furball malware, in its current form, can retrieve commands from a remote server that will allow it to get contacts, documents from exterior storage, a listing of mounted apps, basic procedure metadata, and synced user accounts.
The reduction in active application operation notwithstanding, the sample further more stands out for applying an elementary code obfuscation scheme which is noticed as an try to get previous security limitations.
“The Domestic Kitten marketing campaign is however lively, making use of copycat internet websites to focus on Iranian citizens,” Stefanko mentioned. “The operator’s goal has improved a little from distributing whole-featured Android spy ware to a lighter variant.”
Uncovered this article intriguing? Adhere to THN on Fb, Twitter and LinkedIn to read through additional exceptional content we submit.
Some components of this report are sourced from:
thehackernews.com


 Ransomware activity down 11% worldwide in Q3, but rise expected
Ransomware activity down 11% worldwide in Q3, but rise expected