An OPSEC error by an Iranian threat actor has laid bare the internal workings of the hacking team by providing a scarce insight into the “at the rear of-the-scenes glance into their approaches.”
IBM’s X-Drive Incident Response Intelligence Companies (IRIS) bought hold of almost five several hours really worth of video recordings of the condition-sponsored group it calls ITG18 (also termed Charming Kitten, Phosphorous, or APT35) that it makes use of to coach its operators.
Some of the victims in the videos integrated particular accounts of U.S. and Greek Navy staff, in addition to unsuccessful phishing attempts directed against U.S. condition department officials and an unnamed Iranian-American philanthropist.
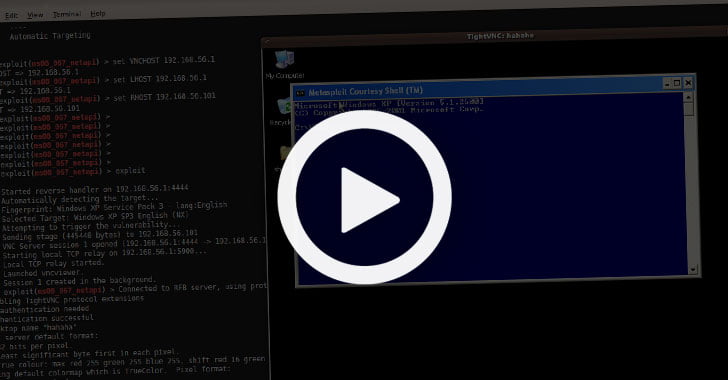
“Some of the videos confirmed the operator handling adversary-made accounts even though others confirmed the operator screening accessibility and exfiltrating info from earlier compromised accounts,” the scientists stated.
The IBM researchers stated they found the films on a digital non-public cloud server that was remaining uncovered due to a misconfiguration of security options. The server, which was also uncovered to host many ITG18 domains previously this calendar year, held far more than 40 gigabytes of knowledge.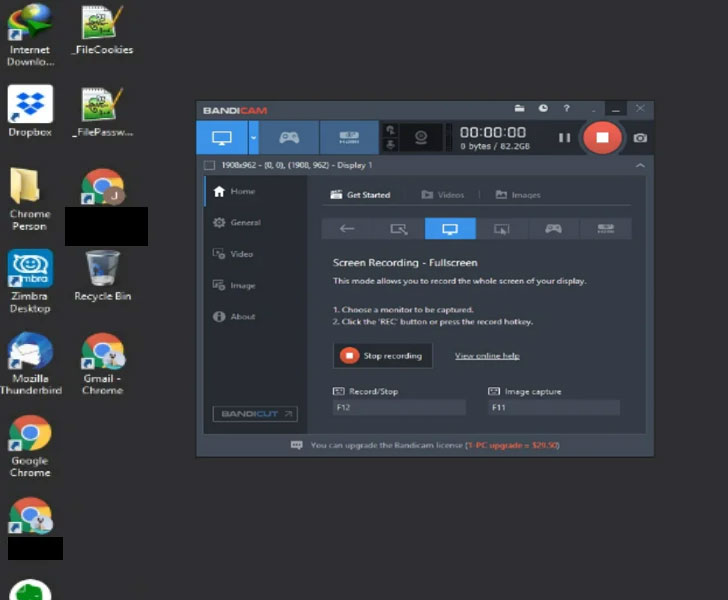
The learned online video files display that ITG18 experienced accessibility to the targets’ email and social media credentials attained by using spear-phishing, using the details to log in to the accounts, delete notifications of suspicious logins so as not to alert the victims, and exfiltrate contacts, images, and paperwork from Google Push.
“The operator was also ready to signal into victims’ Google Takeout (takeout.google.com), which lets a consumer to export articles from their Google Account, to involve locale background, info from Chrome, and associated Android gadgets,” the researchers mentioned.
In addition to this, the video clips — captured working with Bandicam’s display screen-recording tool — also clearly show that the actors driving the procedure plugged the victims’ qualifications to Zimbra’s email collaboration software package intending to keep an eye on and handle the compromised email accounts.
Exterior of email accounts, the scientists stated they observed the attackers employing a prolonged checklist of compromised usernames and passwords versus at minimum 75 distinct web sites ranging from banking companies to movie and songs streaming to one thing as trivial as pizza shipping and child goods.
Other clips showed the ITG18 team leveraging dummy Yahoo! accounts, which involve a phone variety with Iran’s region code (+98), employing them to send out the phishing e-mails, some of which bounced back again, suggesting the email messages did not reach the victim’s inbox.
“Throughout the video clips where by the operator was validating victim credentials, if the operator efficiently authenticated from a website that was set up with multi-variable authentication (MFA) they paused and moved on to an additional established of credentials with out attaining accessibility,” the scientists explained.
ITG18 has a very long record of focusing on the U.S. and the Middle Eastern army, diplomatic, and authorities personnel for intelligence gathering and espionage to provide Iran’s geopolitical pursuits.
If anything, the discovery emphasizes the have to have to secure your accounts by utilizing more robust passwords, turning on two-factor authentication, and reviewing and restricting access to third-get together applications.
“The compromise of private information of users of the Greek and U.S. Navy could be in assistance of espionage functions connected to various proceedings taking place in the Gulf of Oman and Arabian Gulf,” IBM X-Power scientists concluded. “The team has shown persistence in its operations and constant generation of new infrastructure in spite of many general public disclosures and wide reporting on its action.”
Uncovered this post interesting? Comply with THN on Fb, Twitter and LinkedIn to go through a lot more special material we post.
July 17, 2020

 The IT Pro Podcast: The secret life of hackers
The IT Pro Podcast: The secret life of hackers