Danger actors are leveraging a just lately disclosed security flaw impacting Ivanti Connect Secure, Plan Safe, and ZTA gateways to deploy a backdoor codenamed DSLog on susceptible devices.
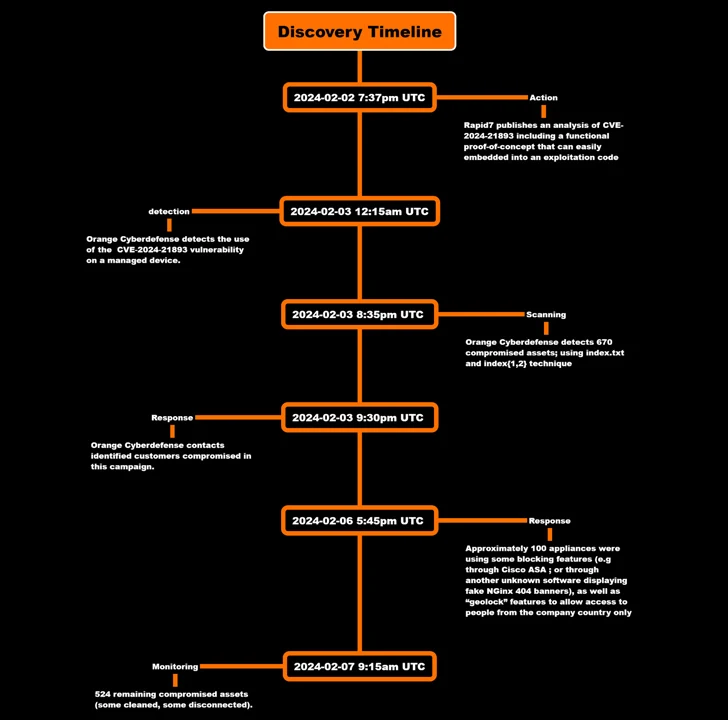
That’s according to findings from Orange Cyberdefense, which mentioned it noticed the exploitation of CVE-2024-21893 inside several hours of the public launch of the evidence-the-thought (PoC) code.
CVE-2024-21893, which was disclosed by Ivanti late last month alongside CVE-2024-21888, refers to a server-facet request forgery (SSRF) vulnerability in the SAML module that, if productively exploited, could permit entry to usually limited resources sans any authentication.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The Utah-dependent enterprise has given that acknowledged that the flaw has confined specific attacks, even though the exact scale of the compromises is unclear.

Then, final week, the Shadowserver Basis unveiled a surge in exploitation attempts targeting the vulnerability originating from over 170 unique IP addresses, shortly following equally Speedy7 and AssetNote shared added complex specifics.
Orange Cyberdefense’s hottest evaluation reveals that compromises have been detected as early as February 3, with the attack targeting an unnamed customer to inject a backdoor that grants persistent remote access.
“The backdoor is inserted into an current Perl file named ‘DSLog.pm,'” the firm explained, highlighting an ongoing pattern in which existing legit parts – in this situation, a logging module – are modified to insert the malicious code.
DSLog, the implant, will come fitted with its personal tips to hamper examination and detection, including embedding a exceptional hash per appliance, therefore making it difficult to use the hash to make contact with the identical backdoor on another gadget.
The exact hash worth is provided by the attackers to the User-Agent header field in an HTTP request to the appliance to make it possible for the malware to extract the command to be executed from a query parameter referred to as “cdi.” The decoded instruction is then operate as the root person.
“The web shell does not return standing/code when hoping to call it,” Orange Cyberdefense reported. “There is no known way to detect it immediately.”

It even further observed evidence of threat actors erasing “.access” logs on “various” appliances in a bid to deal with up the forensic path and fly beneath the radar.
But by checking the artifacts that were being created when triggering the SSRF vulnerability, the company said it was equipped to detect 670 compromised assets all through an preliminary scan on February 3, a variety that has dropped to 524 as of February 7.
In light-weight of the ongoing exploitation of Ivanti products, it can be extremely encouraged that “all shoppers factory reset their equipment ahead of implementing the patch to reduce the danger actor from gaining update persistence in your natural environment.”
Found this post interesting? Stick to us on Twitter and LinkedIn to browse far more exceptional articles we submit.
Some areas of this article are sourced from:
thehackernews.com


 Alert: CISA Warns of Active ‘Roundcube’ Email Attacks – Patch Now
Alert: CISA Warns of Active ‘Roundcube’ Email Attacks – Patch Now