The Midnight Blizzard and Cloudflare-Atlassian cybersecurity incidents raised alarms about the vulnerabilities inherent in important SaaS platforms. These incidents illustrate the stakes included in SaaS breaches — safeguarding the integrity of SaaS apps and their delicate data is critical but is not simple. Frequent threat vectors this sort of as subtle spear-phishing, misconfigurations and vulnerabilities in third-party app integrations reveal the intricate security troubles struggling with IT units.
In the circumstance of Midnight Blizzard, password spraying towards a examination atmosphere was the first attack vector. For Cloudflare-Atlassian, menace actors initiated the attack via compromised OAuth tokens from a prior breach at Okta, a SaaS identification security service provider.
What Precisely Took place?

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Microsoft Midnight Blizzard Breach
Microsoft was focused by the Russian “Midnight Blizzard” hackers (also acknowledged as Nobelium, APT29, or Cozy Bear) who are joined to the SVR, the Kremlin’s overseas intelligence provider unit.
In the Microsoft breach, the risk actors:
 Recreation of illustration by Amitai Cohen
Recreation of illustration by Amitai Cohen
Cloudflare-Atlassian Breach
On Thanksgiving Day, November 23, 2023, Cloudflare’s Atlassian programs ended up also compromised by a country-point out attack.
SaaS Security GuideCan Your Security Workforce Observe 3rd Party Apps? 60% of Teams Are unable to
Believe your SaaS security is top rated-notch? Appomni surveyed more than 600 worldwide security practitioners, and 79% of professionals felt the same – yet they faced cybersecurity incidents! Dive into the insights of the AppOmni 2023 Report.
Find out How You Can
Risk Actors Progressively Focus on SaaS
These breaches are element of a broader pattern of nation-point out actors focusing on SaaS service companies, like but not confined to espionage and intelligence collecting. Midnight Blizzard beforehand engaged in important cyber operations, including the 2021 SolarWinds attack.
These incidents underscore the worth of continual monitoring of your SaaS environments and the ongoing risk posed by sophisticated cyber adversaries concentrating on critical infrastructure and operational tech stack. They also spotlight substantial vulnerabilities related to SaaS identification administration and the requirement for stringent 3rd-party application risk administration techniques.
Attackers use popular ways, techniques and methods (TTPs) to breach SaaS vendors through the adhering to destroy chain:
Breaking the SaaS Get rid of Chain
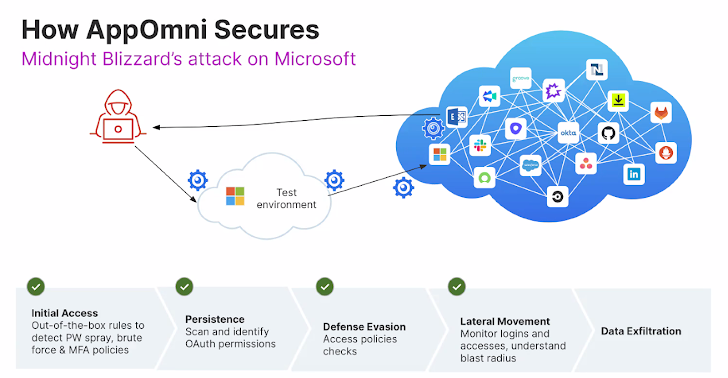
1 helpful way to split the destroy chain early is with ongoing monitoring, granular plan enforcement, and proactive lifecycle management above your SaaS environments. A SaaS Security Posture Management (SSPM) platform like AppOmni can support with detecting and alerting on:
- First Accessibility: Out-of-the-box rules to detect credential compromise, including password spraying, brute pressure attacks, and unenforced MFA policies
- Persistence: Scan and establish OAuth permissions and detect OAuth hijacking
- Protection Evasion: Entry plan checks, detect if a new identification supplier (IdP) is designed, detect authorization improvements.
- Lateral Motion: Watch logins and privileged accessibility, detect poisonous combos, and understand the blast radius of a probably compromised account
Notice: This expertly contributed post is written by Beverly Nevalga, AppOmni.
Observed this post fascinating? This article is a contributed piece from 1 of our valued companions. Adhere to us on Twitter and LinkedIn to go through far more special content we put up.
Some areas of this article are sourced from:
thehackernews.com

 Ivanti Vulnerability Exploited to Install ‘DSLog’ Backdoor on 670+ IT Infrastructures
Ivanti Vulnerability Exploited to Install ‘DSLog’ Backdoor on 670+ IT Infrastructures