The North Korea-linked Lazarus Group has been connected to a cyber espionage attack concentrating on an unnamed aerospace organization in Spain in which workers of the firm have been approached by the risk actor posing as a recruiter for Meta.
“Staff of the focused business ended up contacted by a fake recruiter through LinkedIn and tricked into opening a malicious executable file presenting itself as a coding problem or quiz,” ESET security researcher Peter Kálnai stated in a complex report shared with The Hacker Information.
The attack is aspect of a prolonged-standing spear-phishing marketing campaign known as Procedure Aspiration Position that is orchestrated by the hacking crew in an try to entice workers working at potential targets that are of strategic desire are enticed with lucrative task chances to activate the an infection chain.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Previously this March, the Slovak cybersecurity organization specific an attack wave aimed at Linux buyers that concerned the use of bogus HSBC occupation provides to launch a backdoor named SimplexTea.
The best goal of the latest intrusion, which is intended for Windows methods, is the deployment of an implant codenamed LightlessCan.
“The most worrying part of the attack is the new type of payload, LightlessCan, a advanced and potentially evolving resource that reveals a significant stage of sophistication in its design and style and operation, and signifies a significant development in malicious capabilities in contrast to its predecessor, BLINDINGCAN,” Kálnai said.
BLINDINGCAN, also recognised by the name AIRDRY or ZetaNile, is a element-wealthy malware able of harvesting sensitive data from infiltrated hosts.
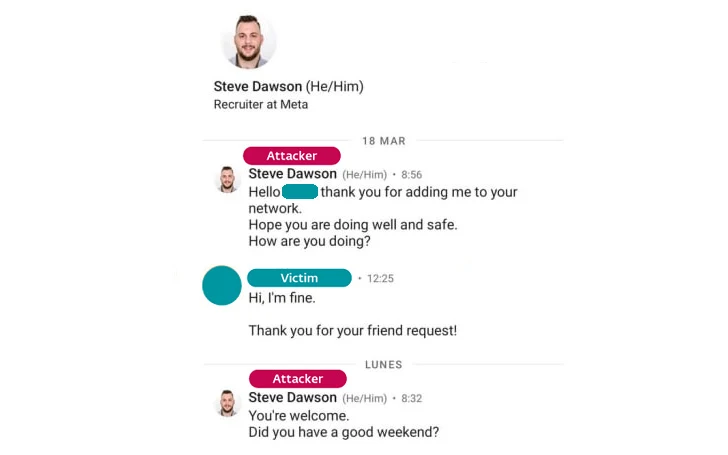
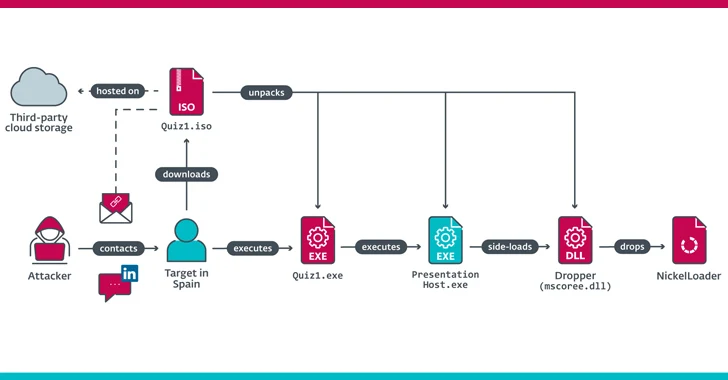
It all commenced with the concentrate on acquiring a concept on LinkedIn from a faux recruiter operating for Meta Platforms, who then despatched two coding challenges as aspect of the intended hiring process and certain the victim to execute the take a look at documents (named Quiz1.iso and Quiz2.iso) hosted on a third-party cloud storage platform.
ESET stated the ISO documents, which contained malicious binaries Quiz1.exe and Quiz2.exe, were being downloaded and executed on a corporation-presented system, properly ensuing in the self-compromise of the procedure.
Future WEBINARFight AI with AI — Battling Cyber Threats with Up coming-Gen AI Applications
Ready to deal with new AI-driven cybersecurity worries? Join our insightful webinar with Zscaler to handle the escalating risk of generative AI in cybersecurity.
Supercharge Your Skills
The attack paves the way for an HTTP(S) downloader referred to as NickelLoader, which allows the attackers to deploy any preferred method into the memory of the victim’s laptop or computer, which includes the LightlessCan remote entry trojan and a variant of BLINDINGCAN referred to as miniBlindingCan (aka AIRDRY.V2).
LightlessCan arrives equipped with aid for as a lot of as 68 unique instructions, whilst in its latest model, only 43 of individuals instructions are applied with some functionality. On tminiBlindingCan’s major accountability is to transmit process info and obtain information retrieved from a distant server, amongst others.
A noteworthy trait of the marketing campaign is the use of execution guardrails to reduce the payloads from becoming decrypted and run on any other machine other than that of the supposed victim’s.
“LightlessCan mimics the functionalities of a large array of native Windows instructions, enabling discreet execution in the RAT alone in its place of noisy console executions,” Kálnai said. “This strategic shift enhances stealthiness, earning detecting and examining the attacker’s things to do extra tough.”
Observed this short article appealing? Stick to us on Twitter and LinkedIn to browse additional exclusive articles we article.
Some components of this article are sourced from:
thehackernews.com

 Post-Quantum Cryptography: Finally Real in Consumer Apps?
Post-Quantum Cryptography: Finally Real in Consumer Apps?