A new security flaw has been disclosed in the libcue library impacting GNOME Linux units that could be exploited to realize remote code execution (RCE) on influenced hosts.
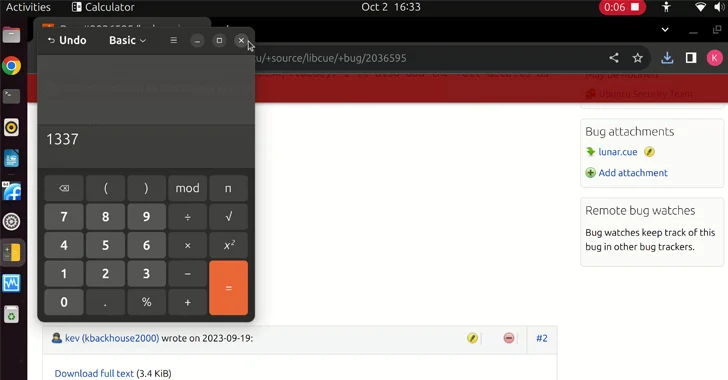
Tracked as CVE-2023-43641 (CVSS rating: 8.8), the issue is explained as a situation of memory corruption in libcue, a library designed for parsing cue sheet documents. It impacts variations 2.2.1 and prior.
libcue is included into Tracker Miners, a search engine device that is included by default in GNOME and indexes documents in the technique for uncomplicated obtain.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The challenge is rooted in an out-of-bounds array accessibility in the keep track of_set_index functionality that will allow for acquiring code execution on the machine simply by tricking a sufferer into clicking a destructive website link and downloading a .cue file.
“A person of the GNOME desktop surroundings can be exploited by downloading a cue sheet from a destructive webpage,” according to a description of the vulnerability in the Nationwide Vulnerability Database (NVD).
“Because the file is saved to ‘~/Downloads,’ it is then routinely scanned by tracker-miners. And simply because it has a .cue filename extension, tracker-miners use libcue to parse the file. The file exploits the vulnerability in libcue to obtain code execution.”
Extra technical information about the vulnerability has been withheld to give people more than enough time to put in the hottest updates.
“From time to time a vulnerability in a seemingly innocuous library can have a massive affect,” GitHub security researcher Kevin Backhouse, who discovered the bug, mentioned. “Owing to the way that it really is utilized by tracker-miners, this vulnerability in libcue grew to become a one particular-click on RCE.”

The disclosure comes two weeks right after GitHub unveiled comprehensive details about CVE-2023-3420, a higher-severity sort confusion vulnerability in the Google Chrome V8 JavaScript motor that allows distant code execution (RCE) in the renderer sandbox of Chrome by browsing a malicious website.
“Vulnerabilities like this are often the beginning level for a ‘one-click’ exploit, which compromise the victim’s system when they pay a visit to a malicious website,” security researcher Gentleman Yue Mo explained. “A renderer RCE in Chrome makes it possible for an attacker to compromise and execute arbitrary code in the Chrome renderer method.”
Identified this short article fascinating? Observe us on Twitter and LinkedIn to go through more unique content material we put up.
Some pieces of this write-up are sourced from:
thehackernews.com

 Citrix Devices Under Attack: NetScaler Flaw Exploited to Capture User Credentials
Citrix Devices Under Attack: NetScaler Flaw Exploited to Capture User Credentials