A Linux variation of a multi-system backdoor called DinodasRAT has been detected in the wild targeting China, Taiwan, Turkey, and Uzbekistan, new results from Kaspersky reveal.
DinodasRAT, also regarded as XDealer, is a C++-based mostly malware that gives the skill to harvest a vast selection of delicate details from compromised hosts.
In Oct 2023, Slovak cybersecurity company ESET revealed that a governmental entity in Guyana has been targeted as portion of a cyber espionage campaign dubbed Operation Jacana to deploy the Windows edition of the implant.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Then previous 7 days, Trend Micro specific a danger action cluster it tracks as Earth Krahang and which has shifted to employing DinodasRAT considering that 2023 in its attacks aimed at quite a few authorities entities around the globe.
The use of DinodasRAT has been attributed to various China-nexus danger actors, like LuoYu, after once again reflecting the software sharing commonplace among hacking crews determined as acting on behalf of the region.
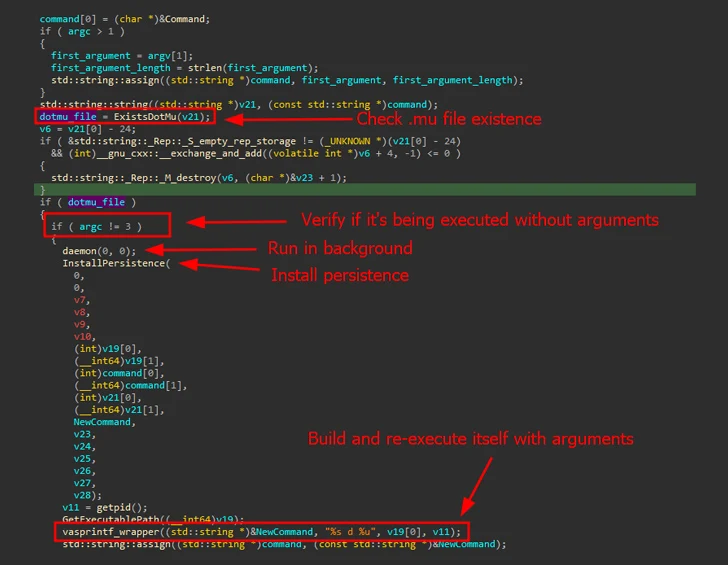
Kaspersky said it discovered a Linux model of the malware (V10) in early Oct 2023. Evidence gathered so much displays that the initial known variant (V7) dates again to 2021.
It can be predominantly created to focus on Purple Hat-dependent distributions and Ubuntu Linux. Upon execution, it establishes persistence on the host by utilizing SystemV or SystemD startup scripts and periodically contacts a distant server around TCP or UDP to fetch the instructions to be operate.

DinodasRAT is outfitted to carry out file operations, adjust command-and-management (C2) addresses, enumerate and terminate running procedures, execute shell instructions, down load a new variation of the backdoor, and even uninstall itself.
It also takes methods to evade detection by debugging and monitoring resources, and like its Windows counterpart, makes use of the Small Encryption Algorithm (TEA) to encrypt C2 communications.
“DinodasRAT’s most important use situation is to gain and keep obtain by using Linux servers rather than reconnaissance,” Kaspersky mentioned. “The backdoor is entirely useful, granting the operator entire management about the contaminated equipment, enabling facts exfiltration and espionage.”
Identified this write-up interesting? Abide by us on Twitter and LinkedIn to read a lot more special content material we submit.
Some components of this article are sourced from:
thehackernews.com

 Finland Blames Chinese Hacking Group APT31 for Parliament Cyber Attack
Finland Blames Chinese Hacking Group APT31 for Parliament Cyber Attack