A new Google malvertising campaign is leveraging a cluster of domains mimicking a legit IP scanner computer software to produce a formerly unfamiliar backdoor dubbed MadMxShell.
“The risk actor registered numerous glimpse-alike domains using a typosquatting technique and leveraged Google Adverts to force these domains to the top of research motor results focusing on unique look for key terms, therefore luring victims to take a look at these internet sites,” Zscaler ThreatLabz researchers Roy Tay and Sudeep Singh stated.
As several as 45 domains are reported to have been registered amongst November 2023 and March 2024, with the web sites masquerading as port scanning and IT management software such as Innovative IP Scanner, Indignant IP Scanner, IP scanner PRTG, and ManageEngine.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
When this is not the initially time menace actors are banking on malvertising tactics to provide malware by using lookalike sites, the progress marks the initially time the delivery automobile is getting made use of to propagate a sophisticated Windows backdoor.

Hence, customers who finish up exploring for these applications are shown bogus web sites that include JavaScript code built to down load a destructive file (“Advanced-ip-scanner.zip”) upon clicking the obtain button.
Present within the ZIP archive is a DLL file (“IVIEWERS.dll”) and an executable (“Highly developed-ip-scanner.exe”), the latter of which takes advantage of DLL aspect-loading to load the DLL and activate the an infection sequence.
The DLL file is liable for injecting the shellcode into the “Highly developed-ip-scanner.exe” procedure through a approach named course of action hollowing, next which the injected EXE file unpacks two added documents – OneDrive.exe and Secur32.dll.
OneDrive.exe, a legit signed Microsoft binary, is then abused to sideload Secur32.dll, and in the long run execute the shellcode backdoor, but not prior to environment up persistence on the host by means of a scheduled job and disabling Microsoft Defender Antivirus.
The backdoor – so named for its use of DNS MX queries for command-and-management (C2) – is developed to obtain procedure data, run instructions via cmd.exe, and complete basic file manipulation operations such as looking at, crafting, and deleting data files.
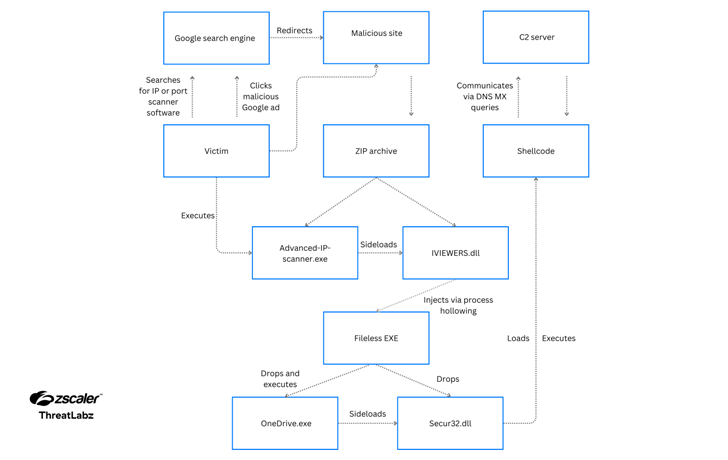
It sends requests to the C2 server (“litterbolo[.]com”) by encoding the knowledge in the subdomain(s) of the Fully Experienced Domain Name (FQDN) in a DNS mail exchange (MX) question packet and receives commands encoded inside the reaction packet.
“The backdoor employs strategies these types of as numerous stages of DLL facet-loading and DNS tunneling for command-and-manage (C2) communication as a indicates to evade endpoint and network security solutions, respectively,” Tay and Singh said.
“In addition, the backdoor takes advantage of evasive tactics like anti-dumping to protect against memory analysis and hinder forensics security alternatives.”

There is at this time no sign of where the malware operators originate from or what their intentions are, but Zscaler claimed it recognized two accounts created by them on prison underground forums like blackhatworld[.]com and social-eng[.]ru making use of the email address wh8842480@gmail[.]com, which was also utilized to register a domain spoofing State-of-the-art IP Scanner.
Particularly, the threat actor has been located partaking in posts supplying techniques to set up endless Google AdSense threshold accounts way back again in June 2023, indicating their curiosity in launching their individual extended-lasting malvertising campaign.
“Google Adverts threshold accounts and methods for abusing them are generally traded on BlackHat community forums,” the researchers explained. “Several moments they present a way for the threat actor to add as numerous credits as possible to run Google Advertisements campaigns.”
“This lets the danger actors to run campaigns without having essentially shelling out until finally the threshold limit. A reasonably significant threshold restrict allows the threat actor run the advert marketing campaign for a substantial amount of time.”
Uncovered this short article fascinating? Stick to us on Twitter and LinkedIn to browse extra exclusive articles we publish.
Some pieces of this write-up are sourced from:
thehackernews.com

 Russian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
Russian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks