Microsoft on Wednesday disclosed that it identified a set of remarkably focused social engineering attacks mounted by a Russian country-point out threat actor making use of credential theft phishing lures sent as Microsoft Teams chats.
The tech large attributed the attacks to a group it tracks as Midnight Blizzard (previously Nobelium). It can be also named APT29, BlueBravo, Cozy Bear, Iron Hemlock, and The Dukes.
“In this hottest exercise, the danger actor takes advantage of previously compromised Microsoft 365 tenants owned by smaller enterprises to build new domains that show up as technical guidance entities,” the company claimed.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“Using these domains from compromised tenants, Midnight Blizzard leverages Teams messages to send lures that try to steal qualifications from a focused business by participating a person and eliciting approval of multi-factor authentication (MFA) prompts.”
Microsoft claimed the marketing campaign, noticed considering the fact that at the very least late May possibly 2023, affected considerably less than 40 companies globally spanning federal government, non-governing administration organizations (NGOs), IT solutions, technology, discrete producing, and media sectors.

The risk actor has been noticed to benefit from token theft methods for initial obtain into focused environments, together with other approaches these kinds of as authentication spear-phishing, password spray, and brute-drive attacks.
One more recognized hallmark is its exploitation of on-premises environments to laterally shift to the cloud as very well as the abuse of provider providers’ believe in chain to attain access to downstream customers, as observed in the SolarWinds hack of 2020.
In the new round of attacks linked to Midnight Blizzard, a new onmicrosoft.com subdomain is additional to a tenant earlier compromised in attacks, adopted by generating a new consumer with that subdomain to initiate a Teams chat ask for with possible targets by masquerading as a technical aid person or Microsoft’s Id Defense crew.
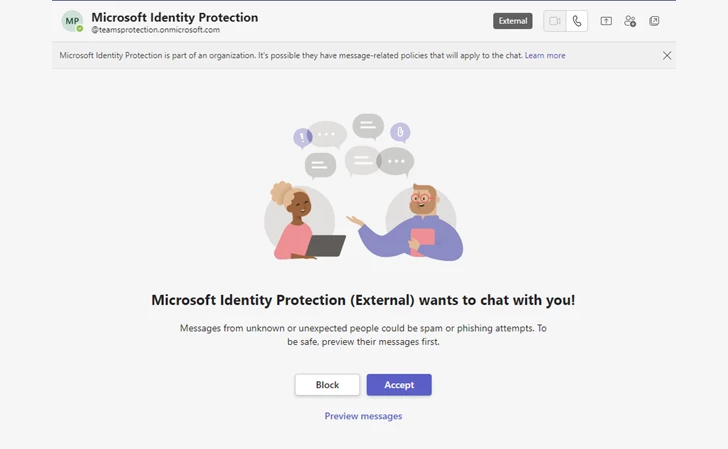
“If the target consumer accepts the message ask for, the user then receives a Microsoft Teams information from the attacker making an attempt to convince them to enter a code into the Microsoft Authenticator app on their cell machine,” Microsoft explained.
Ought to the sufferer stick to through with the guidelines, the risk actor is granted a token to authenticate as the targeted consumer, thereby allowing for account takeover and abide by-on put up-compromise action.
“In some cases, the actor tries to include a machine to the business as a managed gadget by using Microsoft Entra ID (previously Azure Lively Directory), very likely an endeavor to circumvent conditional entry guidelines configured to restrict accessibility to distinct sources to managed units only,” Microsoft cautioned.

The conclusions occur times following the risk actor was attributed to phishing attacks focusing on diplomatic entities throughout Jap Europe with the goal of providing a new backdoor referred to as GraphicalProton.
They also abide by the discovery of a number of new Azure Advertisement (AAD) Hook up attack vectors that could let malicious cyber actors to make an undetectable backdoor by stealing cryptographic hashes of passwords by injecting malicious code into a hash syncing approach and intercepting credentials by implies of an adversary-in-the-middle (AitM) attack.
“For example, attackers can leverage the extraction of NT hashes to guarantee they get every long term password improve in the domain,” Sygnia stated in a statement shared with The Hacker News.
“Menace actors can also use [Active Directory Certificate Services] to get hold of AAD Connector passwords, as perfectly as provide as a gentleman-in-the-middle and launch attacks towards SSL-encrypted channels in the network by exploiting misconfigurations in certification templates that have server authentication.”
Found this posting appealing? Observe us on Twitter and LinkedIn to go through extra distinctive articles we article.
Some parts of this report are sourced from:
thehackernews.com


 Researchers Discover Bypass for Recently Patched Critical Ivanti EPMM Vulnerability
Researchers Discover Bypass for Recently Patched Critical Ivanti EPMM Vulnerability