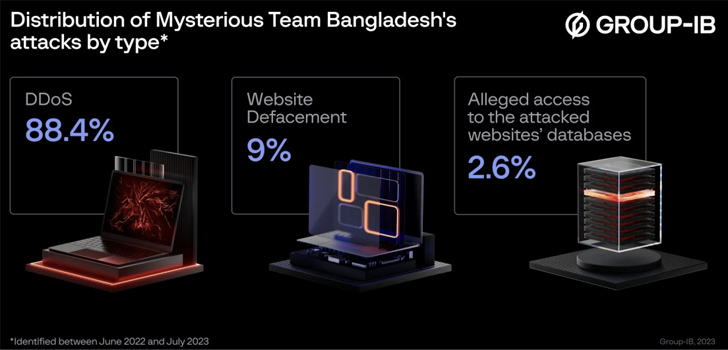
A hacktivist group identified as Mysterious Workforce Bangladesh has been linked to about 750 distributed denial-of-provider (DDoS) attacks and 78 internet site defacements since June 2022.
“The group most routinely attacks logistics, governing administration, and economical sector businesses in India and Israel,” Singapore-headquartered cybersecurity firm Team-IB said in a report shared with The Hacker News. “The group is generally pushed by spiritual and political motives.”
Some of the other focused nations around the world include Australia, Senegal, the Netherlands, Sweden, and Ethiopia.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
In addition, the menace actor is claimed to have obtained entry to web servers and administrative panels, probably by exploiting acknowledged security flaws or improperly-secured passwords.
Mysterious Crew Bangladesh, as the name implies, is suspected to be of Bangladeshi origin. “We are operating to defend Our Bangladesh Cyberspace,” the group’s Intro on Fb reads.
The group has an active social media presence throughout Telegram and Twitter. Its LinkedIn profile lists “Procedure Israel” as an ongoing job due to the fact June 2022, professing it supports Palestine, that the “Israeli Governing administration killing & torturing Palestine people’s,” and that “we will attacking their cyberspace right until they cease killing Palestine People’s.”

Particulars about the risk actor initially emerged in late 2022 when CloudSEK unveiled its plans to attack entities in India. A December 2022 attack on India’s Central Board of Better Training (CBHE) devices led to the publicity of individually identifiable info these types of as governing administration identification quantities. It has because been attributed to DDoS attacks on a number of UAE authorities websites.
The pretty very first attack marketing campaign against India took location on June 22, 2022, with the team showcasing an affinity for government means and the internet sites of financial institutions and monetary companies.
“The renaissance of hacktivism across the world may well have its roots in the ongoing geopolitical conflict, during which hacktivists have carried out several strategies,” the company said.
“As can be found, modern day hacktivist teams are fewer inspired by any ideology but attempt to acquire their have brand name and recognition in get to subsequently monetize their data means via the sale of marketing.”

The conclusions appear as a pro-Russian hacktivist collective dubbed NoName057(16) has been joined to a clean wave of disruptive DDoS attacks on Spanish and Italian websites in latest months.
“What is new about NoName057(16)’s DDoSia attacks is that the team admins execute reconnaissance prior to staging their attack vectors,” Radware stated in a Wednesday analysis. “They examine the target internet site and discover the most resource-intensive pieces of the web-site.
“Webpages with a search function or a type to fill in are regular candidates. NoName057(16) data all the variables used by GET and Publish requests for people web pages, which include any cookies and opportunity captcha keys, and then crafts particular web requests with placeholders for random details to be leveraged as attack vectors.”
Found this report appealing? Observe us on Twitter and LinkedIn to examine far more distinctive content material we article.
Some parts of this short article are sourced from:
thehackernews.com


 Microsoft Exposes Russian Hackers’ Sneaky Phishing Tactics via Microsoft Teams Chats
Microsoft Exposes Russian Hackers’ Sneaky Phishing Tactics via Microsoft Teams Chats