Microsoft has patched a misconfiguration issue impacting the Azure Lively Directory (AAD) identity and accessibility management company that uncovered many “significant-influence” apps to unauthorized access.
“Just one of these applications is a content administration procedure (CMS) that powers Bing.com and authorized us to not only modify lookup final results, but also start high-effect XSS attacks on Bing consumers,” cloud security organization Wiz claimed in a report. “People attacks could compromise users’ personalized data, such as Outlook emails and SharePoint paperwork.”
The issues ended up claimed to Microsoft in January and February 2022, subsequent which the tech giant applied fixes and awarded Wiz a $40,000 bug bounty. Redmond reported it observed no proof that the misconfigurations ended up exploited in the wild.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The crux of the vulnerability stems from what is termed “Shared Obligation confusion,” whereby an Azure app can be improperly configured to permit consumers from any Microsoft tenant, leading to a potential scenario of unintended access.
Apparently, a variety of Microsoft’s individual inner apps have been uncovered to show this habits, therefore allowing exterior get-togethers to acquire read through and publish to the afflicted applications.
This contains the Bing Trivia app, which the cybersecurity business exploited to alter research final results in Bing and even manipulate articles on the homepage as component of an attack chain dubbed BingBang.

To make issues even worse, the exploit could be weaponized to result in a cross-web page scripting (XSS) attack on Bing.com and extract a victim’s Outlook emails, calendars, Groups messages, SharePoint paperwork, and OneDrive documents.
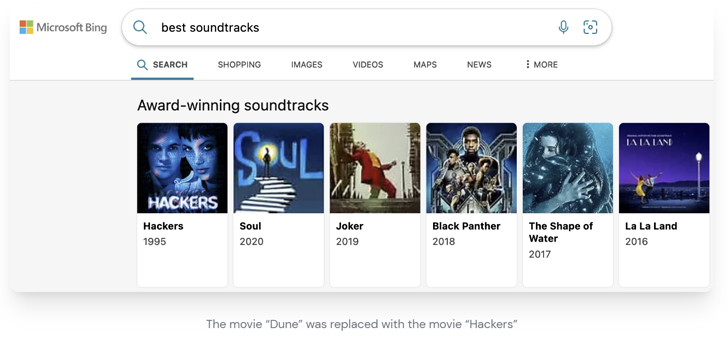
“A malicious actor with the exact same accessibility could’ve hijacked the most preferred lookup effects with the exact payload and leak sensitive data from thousands and thousands of users,” Wiz researcher Hillai Ben-Sasson observed.
Other apps that had been found inclined to the misconfiguration issue include things like Mag News, Central Notification Service (CNS), Speak to Middle, PoliCheck, Ability Automate Weblog, and COSMOS.
THN WEBINARBecome an Incident Reaction Pro!
Unlock the secrets to bulletproof incident reaction – Grasp the 6-Section process with Asaf Perlman, Cynet’s IR Chief!
Do not Pass up Out – Save Your Seat!
The enhancement comes as company penetration tests business NetSPI uncovered aspects of a cross-tenant vulnerability in Energy System connectors that could be abused to get access to sensitive details.
Pursuing accountable disclosure in September 2022, the deserialization vulnerability was fixed by Microsoft in December 2022.
The investigate also follows the launch of patches to remediate Super FabriXss (CVE-2023-23383, CVSS rating: 8.2), a mirrored XSS vulnerability in Azure Support Fabric Explorer (SFX) that could lead to unauthenticated remote code execution.
Identified this short article intriguing? Abide by us on Twitter and LinkedIn to read a lot more exceptional content we publish.
Some elements of this short article are sourced from:
thehackernews.com

 Cacti, Realtek, and IBM Aspera Faspex Vulnerabilities Under Active Exploitation
Cacti, Realtek, and IBM Aspera Faspex Vulnerabilities Under Active Exploitation