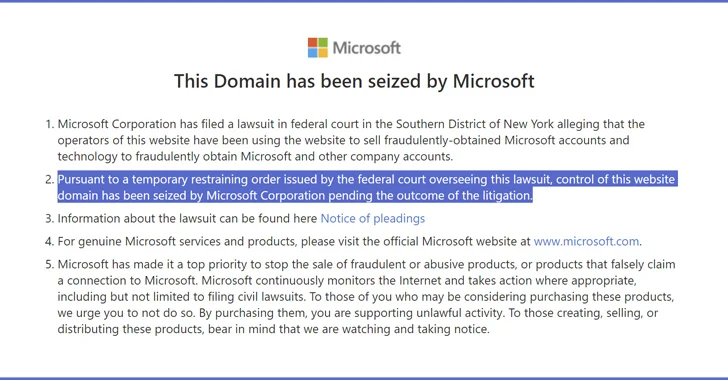
Microsoft on Wednesday claimed it received a courtroom purchase to seize infrastructure established up by a group referred to as Storm-1152 that peddled roughly 750 million fraudulent Microsoft accounts and tools by a network of bogus internet sites and social media internet pages to other prison actors, netting them hundreds of thousands of dollars in illicit income.
“Fraudulent on line accounts act as the gateway to a host of cybercrime, which includes mass phishing, id theft and fraud, and dispersed denial-of-support (DDoS) attacks,” Amy Hogan-Burney, the company’s associate common counsel for cybersecurity coverage and safety, stated.
These cybercrime-as-a-company (CaaS) choices, for each Redmond, are designed to get all-around identification verification application across different technology platforms and assist lessen the initiatives necessary to perform destructive activities online, such as phishing, spamming, ransomware, and fraud, effectively decreasing the barriers to entry for attackers.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Future WEBINAR Defeat AI-Driven Threats with Zero Have confidence in – Webinar for Security Industry experts
Common security actions will not minimize it in present day globe. It’s time for Zero Have faith in Security. Protected your facts like never ahead of.
Be part of Now
Several threat actors, counting Octo Tempest (aka Scattered Spider), are said to have made use of Storm-1152’s accounts to pull off ransomware, facts theft, and extortion techniques. Two other financially motivated danger actors that have ordered fraudulent accounts from Storm-1152 to scale their personal attacks are Storm-0252 and Storm-0455.

The team, lively since at the very least 2021, has been attributed to the next internet websites and web pages –
- Hotmailbox.me for marketing fraudulent Microsoft Outlook accounts
- 1stCAPTCHA, AnyCAPTCHA, and NoneCAPTCHA for selling device understanding-dependent CAPTCHA solving services to bypass id verification
- Social media internet pages for advertising and marketing the services
Microsoft, which collaborated with Arkose Labs on the initiative, said it was ready to establish 3 people today primarily based in Vietnam who have been instrumental in producing and preserving the infrastructure: Duong Dinh Tu, Linh Van Nguyễn (also regarded as Nguyễn Van Linh), and Tai Van Nguyen.

“These men and women operated and wrote the code for the illicit web-sites, revealed detailed stage-by-move guidelines on how to use their products through online video tutorials and delivered chat expert services to guide all those utilizing their fraudulent companies,” Hogan-Burney pointed out.
“Not only did the enterprise sell its technology like any other sort of program company – with pricing structures primarily based upon a customer’s needs – but it also would carry out bogus account registration attacks, promote all those bogus accounts to other cybercriminals, and then hard cash out with crypto forex,” Kevin Gosschalk and Patrice Boffa mentioned.
Identified this posting attention-grabbing? Comply with us on Twitter and LinkedIn to go through far more distinctive material we submit.
Some components of this post are sourced from:
thehackernews.com

 BazaCall Phishing Scammers Now Leveraging Google Forms for Deception
BazaCall Phishing Scammers Now Leveraging Google Forms for Deception