A previously unidentified hacker outfit known as GambleForce has been attributed to a collection of SQL injection attacks towards corporations principally in the Asia-Pacific (APAC) area due to the fact at least September 2023.
“GambleForce takes advantage of a established of basic nevertheless extremely helpful tactics, together with SQL injections and the exploitation of susceptible site content material management techniques (CMS) to steal sensitive data, such as consumer qualifications,” Singapore-headquartered Group-IB explained in a report shared with The Hacker Information.
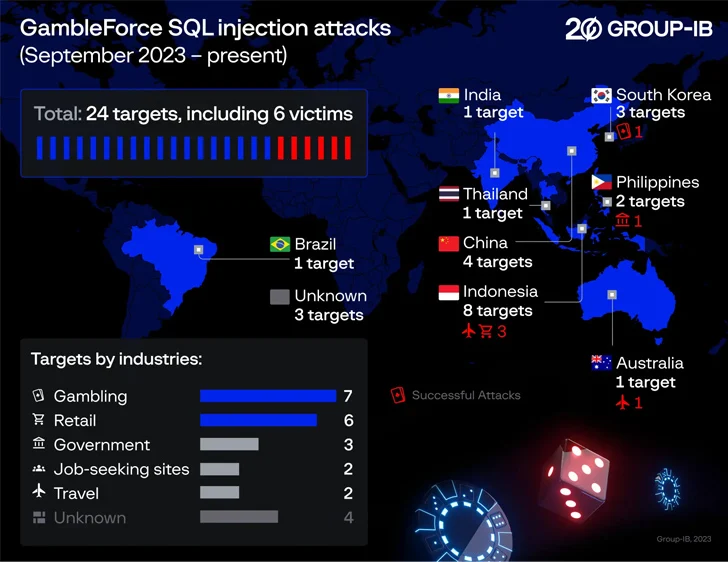
The group is estimated to have qualified 24 companies in the gambling, authorities, retail, and journey sectors throughout Australia, Brazil, China, India, Indonesia, the Philippines, South Korea, and Thailand. 6 of these attacks had been prosperous.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Future WEBINAR Beat AI-Powered Threats with Zero Believe in – Webinar for Security Experts
Regular security measures won’t minimize it in present-day planet. It’s time for Zero Belief Security. Secure your knowledge like hardly ever right before.
Join Now
The modus operandi of GambleForce is its exceptional reliance on open up-resource equipment like dirsearch, sqlmap, tinyproxy, and redis-rogue-getshell at different levels of the attacks with the final purpose of exfiltrating delicate facts from compromised networks.
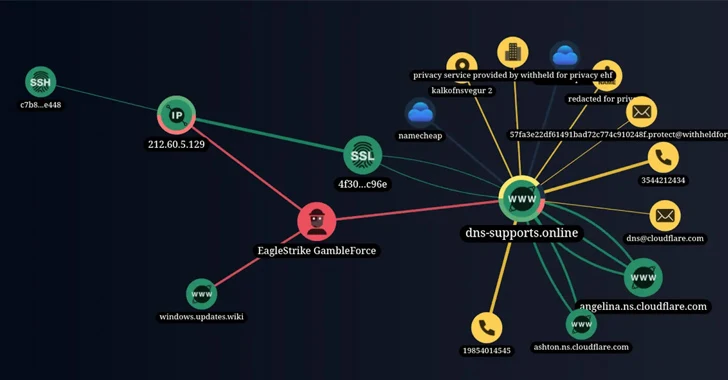
Also made use of by the risk actor is the reputable article-exploitation framework identified as Cobalt Strike. Apparently, the edition of the device uncovered on its attack infrastructure utilized commands in Chinese, though the group’s origins are considerably from distinct.
The attack chains entail the abuse of victims’ public-experiencing apps of victims by exploiting SQL injections as effectively as the exploitation of CVE-2023-23752, a medium-severity flaw in Joomla CMS, to achieve unauthorized obtain to a Brazilian enterprise.
It truly is at the moment not identified how GambleForce leverages the stolen information and facts. The cybersecurity business reported it also took down the adversary’s command-and-command (C2) server and notified the discovered victims.

“Web injections are among the the oldest and most popular attack vectors,” Nikita Rostovcev, senior menace analyst at Team-IB, said.
“And the motive getting is that often developers overlook the value of input security and details validation. Insecure coding methods, incorrect database configurations, and outdated computer software generate a fertile natural environment for SQL injection attacks on web apps.”
Uncovered this post exciting? Adhere to us on Twitter and LinkedIn to read through much more unique content we article.
Some components of this report are sourced from:
thehackernews.com

 Microsoft Takes Legal Action to Crack Down on Storm-1152’s Cybercrime Network
Microsoft Takes Legal Action to Crack Down on Storm-1152’s Cybercrime Network