The prolific risk actor recognised as Scattered Spider has been noticed impersonating freshly hired workforce in qualified corporations as a ploy to blend into usual on-retain the services of processes and takeover accounts and breach organizations across the planet.
Microsoft, which disclosed the pursuits of the economically enthusiastic hacking crew, explained the adversary as “a single of the most risky financial prison groups,” contacting out its operational fluidity and its means to incorporate SMS phishing, SIM swapping, and help desk fraud into its attack model.
“Octo Tempest is a fiscally motivated collective of native English-speaking threat actors identified for launching extensive-ranging strategies that prominently element adversary-in-the-middle (AiTM) approaches, social engineering, and SIM swapping capabilities,” the enterprise explained.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
It is truly worth noting that the activity represented by Octo Tempest is tracked by other cybersecurity corporations below various monikers, like 0ktapus, Scatter Swine, and UNC3944, which has frequently singled out Okta to get elevated permissions and infiltrate specific networks.

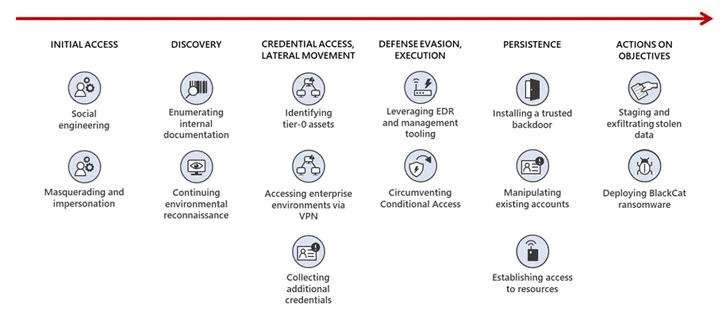
One of the important hallmarks is the concentrating on of guidance and help desk personnel by using social engineering attacks to gain first obtain to privileged accounts, tricking them into accomplishing a reset of the victim’s password and multi-factor authentication (MFA) methods.
Other methods entail purchasing an employee’s qualifications and/or session token(s) on a criminal underground marketplace, or calling the person specifically and socially engineering the user to both install a Distant Monitoring and Administration (RMM) utility, take a look at a bogus login portal using an AiTM phishing toolkit, or clear away their FIDO2 token.
Preliminary attacks mounted by the group qualified cell telecommunication vendors and enterprise process outsourcing (BPO) corporations to initiate SIM swaps, ahead of graduating to monetizing the obtain for selling SIM swaps to other criminals and accomplishing account takeovers of high-net-well worth persons for cryptocurrency theft.
Octo Tempest has given that diversified its targeting to incorporate email and tech provider vendors, gaming, hospitality, retail, managed support companies (MSPs), production, technology, and fiscal sectors, when simultaneously emerging as an affiliate for the BlackCat ransomware gang in mid-2023 to extort victims.
Put in a different way, the end purpose of the attacks differ between cryptocurrency theft and knowledge exfiltration for extortion and ransomware deployment.
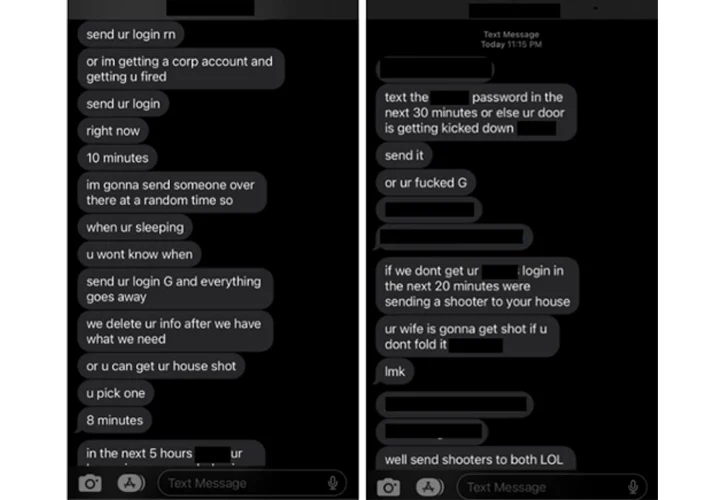
“In late 2022 to early 2023, […] Octo Tempest begun monetizing intrusions by extorting victim organizations for facts stolen through their intrusion operations and in some cases even resorting to bodily threats,” Microsoft said.
“In uncommon circumstances, Octo Tempest resorts to fear-mongering tactics, focusing on certain persons by means of phone phone calls and texts. These actors use personalized facts, such as household addresses and loved ones names, along with bodily threats to coerce victims into sharing qualifications for company accessibility.”

A successful foothold is followed by the attackers carrying out reconnaissance of the natural environment and privilege escalation, the latter of which is attained by means of stolen password coverage techniques, bulk downloads of consumer, group, and part exports.
An additional noteworthy tradecraft is use of compromised security staff accounts inside of target businesses to impair the operating security merchandise in an try to fly beneath the radar, in addition to tampering with the security personnel mailbox principles to automatically delete emails from sellers.
The wide arsenal of resources and methods used by Octo Tempest, such as enrolling actor-controlled gadgets into gadget management computer software to bypass controls and replaying harvested tokens with pleased MFA statements to bypass MFA, is indicative of its in depth complex experience and its capability to navigate elaborate hybrid environments, Redmond explained.
“A one of a kind procedure Octo Tempest employs is compromising VMware ESXi infrastructure, putting in the open up-source Linux backdoor Bedevil, and then launching VMware Python scripts to operate arbitrary commands towards housed digital devices,” the organization further spelled out.
Discovered this report fascinating? Abide by us on Twitter and LinkedIn to read through a lot more special information we put up.
Some pieces of this post are sourced from:
thehackernews.com


 Record-Breaking 100 Million RPS DDoS Attack Exploits HTTP/2 Rapid Reset Flaw
Record-Breaking 100 Million RPS DDoS Attack Exploits HTTP/2 Rapid Reset Flaw