Cloudflare on Thursday stated it mitigated hundreds of hyper-volumetric HTTP distributed denial-of-services (DDoS) attacks that exploited a a short while ago disclosed flaw referred to as HTTP/2 Swift Reset, 89 of which exceeded 100 million requests for every 2nd (RPS).
“The marketing campaign contributed to an overall improve of 65% in HTTP DDoS attack traffic in Q3 when compared to the earlier quarter,” the web infrastructure and security company stated in a report shared with The Hacker Information. “Likewise, L3/4 DDoS attacks also increased by 14%.”
The full variety of HTTP DDoS attack requests in the quarter surged to 8.9 trillion, up from 5.4 trillion in Q2 2023 and 4.7 trillion in Q1 2023. The amount of attack requests in Q4 2022 stood at 6.5 trillion.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

HTTP/2 Rapid Reset (CVE-2023-44487) arrived to mild before this thirty day period adhering to an field-vast coordinated disclosure that delved into DDoS attacks orchestrated by an mysterious actor by leveraging the flaw to focus on several providers these kinds of as Amazon Web Providers (AWS), Cloudflare, and Google Cloud.
Fastly, in a disclosure of its very own on Wednesday, claimed it countered a similar attack that peaked at a volume of about 250 million RPS and a duration of approximately a few minutes.
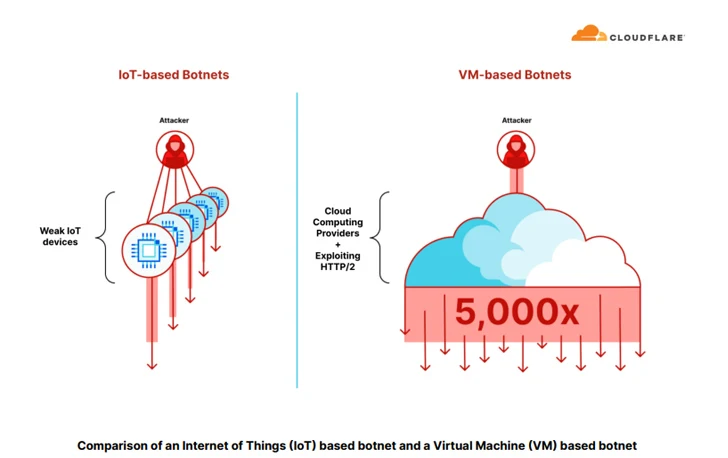
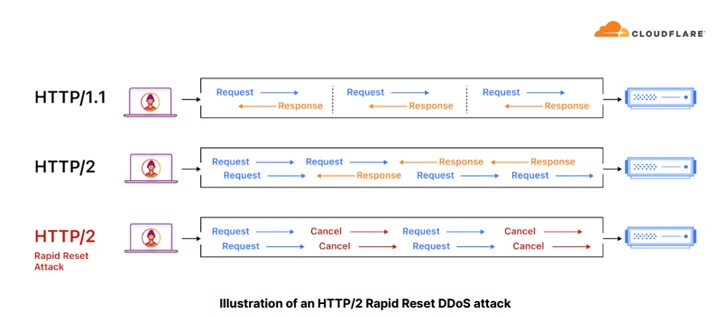
“Botnets that leverage cloud computing platforms and exploit HTTP/2 are equipped to generate up to x5,000 far more force for every botnet node,” Cloudflare mentioned. “This authorized them to start hyper-volumetric DDoS attacks with a modest botnet ranging 5-20 thousand nodes by yourself.”
Some of the major industries targeted by HTTP DDoS attacks incorporate gaming, IT, cryptocurrency, laptop computer software, and telecom, with the U.S., China, Brazil, Germany, and Indonesia accounting for the biggest sources of application layer (L7) DDoS attacks.
On the other hand, the U.S., Singapore, China, Vietnam, and Canada emerged as the main targets of HTTP DDoS attacks.

“For the second consecutive quarter, DNS-based mostly DDoS attacks were the most common,” the firm claimed. “Practically 47% of all attacks were being DNS-centered. This signifies a 44% maximize as opposed to the former quarter. SYN floods keep on being in next location, followed by RST floods, UDP floods, and Mirai attacks.”
Yet another notable adjust is the lower in ransom DDoS attacks, which Cloudflare claimed “is for the reason that danger actors have realized that businesses will not pay them.”
The disclosure will come amid internet traffic fluctuations and a spike in DDoS attacks in the aftermath of the Israel-Hamas war, with Cloudflare repelling quite a few attack makes an attempt aimed at Israeli and Palestinian internet websites.
Found this write-up intriguing? Abide by us on Twitter and LinkedIn to study additional exclusive articles we publish.
Some pieces of this write-up are sourced from:
thehackernews.com


