Although cyberattacks on web-sites get much consideration, there are generally unaddressed risks that can lead to companies struggling with lawsuits and privacy violations even in the absence of hacking incidents. A new scenario analyze highlights 1 of these extra frequent circumstances.
Download the total circumstance review listed here.
It is really a state of affairs that could have influenced any style of enterprise, from healthcare to finance, e-commerce to insurance policy, or any other sector. Not too long ago, Reflectiz, an sophisticated site security remedy provider, introduced a situation analyze concentrating on a forgotten and misconfigured pixel that experienced been associated with a foremost global healthcare company. This overlooked piece of code surreptitiously gathered personal knowledge with no person consent, most likely exposing the organization to substantial fines and problems to its track record.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Nowadays, it has turn out to be widespread apply for companies to embed these pixels into their sites. For instance, the TikTok Pixel is a normal case in point, added to sites to monitor site functions for TikTok. However, when a pixel like this deviates from its meant function and starts to run in an unauthorized manner, it can guide to sizeable issues. In this context, “rogue” indicates the unauthorized selection and sharing of person info, which may perhaps outcome in a breach of numerous information safety restrictions.
The Overlooked Pixel
The circumstance analyze delves into a significant incident involving a healthcare website and an exterior advertising and marketing service supplier. Four a long time in the past, through a marketing marketing campaign, the marketing company incorporated monitoring pixels into the web-site. Sadly, the pixel was forgotten and remained on the site just after the marketing campaign concluded. Above time, as the website underwent variations and expansions, this overlooked pixel ongoing to obtain sensitive client health and fitness details (PHI) devoid of detection. Reflectiz, a proactive internet site security resolution provider, played a pivotal position in determining and mitigating this knowledge leakage.
Configuration Drift in Complex Web Environments
Elaborate web environments normally endure from human mistakes and errors, frequently attributed to variables these as perform overload and worry. This scenario leaves a considerable opening for potential security and privacy issues, with configuration drift being just one of the most frequent issues.
Configuration drift refers to a circumstance in which the configurations of IT programs, program, or infrastructure factors veer absent from their intended or preferred point out around time. This can take place due to numerous variables, including guide adjustments, software updates, or unintended alterations. Configuration drift can introduce inconsistencies, vulnerabilities, and functionality issues within a process, creating it a challenge to maintain procedure trustworthiness, security, and compliance with founded benchmarks. Businesses frequently depend on configuration management and checking instruments to detect and rectify any deviations from the wished-for configuration.
Critical Compliance Issues
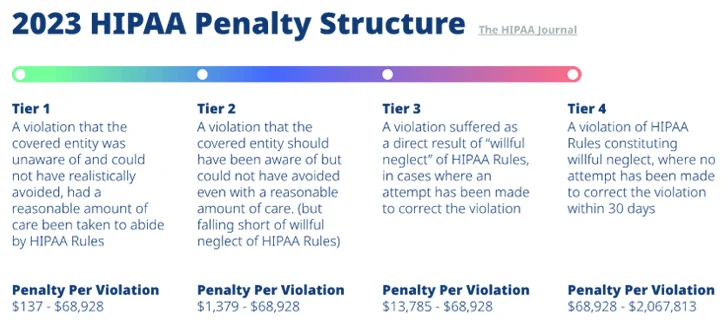
In this situation review, Reflectiz explores the sizeable compliance issues that organizations might encounter when working with rogue pixels in their web environments. This portion will emphasize the subsequent issues:
The Alternative
Reflectiz’s innovative web-site security solution performed a critical part in identifying and disabling the overlooked rogue pixel, giving a useful lesson in the relevance of constant vigilance.
With Reflectiz, you can:
- Repeatedly monitor all delicate web web pages to detect suspicious action of any web ingredient.
- Discover and block third-party web components that keep track of your users’ action without having their consent.
- Detect which third-events receive users’ geo-locale, digital camera, and microphone permissions with out consent.
- Map all web elements that have access to delicate info.
- Validate that all your existing web security tools are performing as intended.
For in-depth investigation and extra specifics, obtain the full case review listed here.
Observed this write-up exciting? Follow us on Twitter and LinkedIn to go through much more unique written content we write-up.
Some parts of this post are sourced from:
thehackernews.com


 Iranian Group Tortoiseshell Launches New Wave of IMAPLoader Malware Attacks
Iranian Group Tortoiseshell Launches New Wave of IMAPLoader Malware Attacks