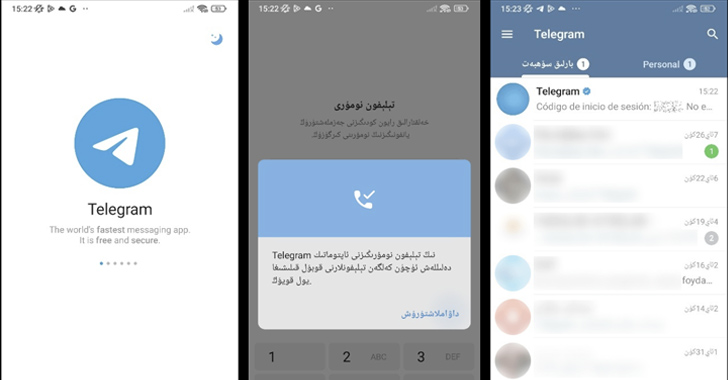
Spyware masquerading as modified variations of Telegram have been noticed in the Google Participate in Shop that’s intended to harvest delicate info from compromised Android units.
In accordance to Kaspersky security researcher Igor Golovin, the apps occur with nefarious characteristics to seize and exfiltrate names, person IDs, contacts, phone numbers, and chat messages to an actor-managed server.
The exercise has been codenamed Evil Telegram by the Russian cybersecurity organization.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The apps have been collectively downloaded tens of millions of occasions prior to they have been taken down by Google. Their details are as follows –
- 電報,紙飛機-TG繁體中文版 or 電報,小飛機-TG繁體中文版 (org.telegram.messenger.wab) – 10 million+ downloads
- TG繁體中文版-電報,紙飛機 (org.telegram.messenger.wab) – 50,000+ downloads
- 电报,纸飞机-TG简体中文版 (org.telegram.messenger.wob) – 50,000+ downloads
- 电报,纸飞机-TG简体中文版 (org.tgcn.messenger.wob) – 10,000+ downloads
- ئۇيغۇر تىلى TG – تېلېگرامما (org.telegram.messenger.wcb) – 100+ downloads
The past app on the checklist interprets to “Telegram – TG Uyghur,” indicating a obvious endeavor to target the Uyghur community.


It can be truly worth noting that the package deal title involved with the Play Keep model of Telegram is “org.telegram.messenger,” whilst the package name for the APK file immediately downloaded from Telegram’s web-site is “org.telegram.messenger.web.”
The use of “wab,” “wcb,” and “wob” for the destructive package names, for that reason, highlights the threat actor’s reliance on typosquatting procedures in purchase to move off as the genuine Telegram application and slip underneath the radar.
Approaching WEBINARWay Also Susceptible: Uncovering the State of the Identity Attack Surface
Obtained MFA? PAM? Service account protection? Locate out how well-geared up your organization certainly is versus identity threats
Supercharge Your Competencies
“At first look, these apps surface to be total-fledged Telegram clones with a localized interface,” the corporation stated. “All the things appears to be like and is effective nearly the identical as the genuine factor. [But] there is a small distinction that escaped the interest of the Google Engage in moderators: the infected variations house an extra module:”
The disclosure comes days right after ESET unveiled a BadBazaar malware campaign concentrating on the formal application market that leveraged a rogue variation of Telegram to amass chat backups.
Comparable copycat Telegram and WhatsApp applications were being uncovered by the Slovak cybersecurity enterprise earlier in March 2023 that arrived fitted with clipper functionality to intercept and modify wallet addresses in chat messages and redirect cryptocurrency transfers to attacker-owned wallets.
Identified this write-up attention-grabbing? Abide by us on Twitter and LinkedIn to browse far more exclusive material we submit.
Some components of this posting are sourced from:
thehackernews.com

 Cybercriminals Weaponizing Legitimate Advanced Installer Tool in Crypto-Mining Attacks
Cybercriminals Weaponizing Legitimate Advanced Installer Tool in Crypto-Mining Attacks