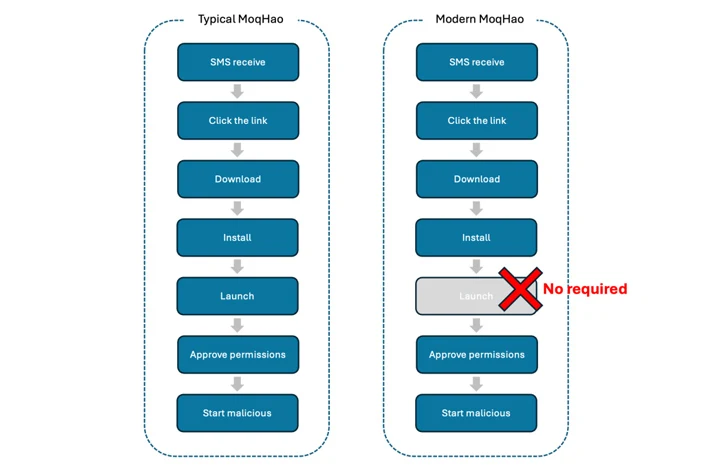
Threat hunters have discovered a new variant of Android malware referred to as MoqHao that instantly executes on infected devices without the need of requiring any user interaction.
“Typical MoqHao demands buyers to put in and start the application to get their wanted goal, but this new variant calls for no execution,” McAfee Labs stated in a report published this 7 days. “While the app is installed, their destructive action commences quickly.”
The campaign’s targets include things like Android end users situated in France, Germany, India, Japan, and South Korea.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
MoqHao, also termed Wroba and XLoader (not to be perplexed with the Windows and macOS malware of the similar title), is an Android-centered cellular threat that is related with a Chinese economically enthusiastic cluster dubbed Roaming Mantis (aka Shaoye).

Standard attack chains commence with bundle shipping-themed SMS messages bearing fraudulent back links that, when clicked from Android units, direct to the deployment of the malware but redirect victims to credential harvesting internet pages impersonating Apple’s iCloud login website page when frequented from an iPhone.
In July 2022, Sekoia specific a marketing campaign that compromised at least 70,000 Android equipment in France. As of early final year, updated variations of MoqHao have been located to infiltrate Wi-Fi routers and undertake Domain Identify Technique (DNS) hijacking, revealing the adversary’s motivation to innovating its arsenal.
The most up-to-date iteration of MoqHao continues to be distributed by means of smishing strategies, but what has transformed is that the malicious payload is operate immediately on set up and prompts the sufferer to grant it dangerous permissions with out launching the application, a conduct formerly noticed with bogus applications made up of the HiddenAds malware.
What is also obtained a facelift is that the backlinks shared in the SMS messages them selves are concealed making use of URL shorteners to increase the likelihood of the attack’s success. The content material for these messages is extracted from the bio (or description) subject from fraudulent Pinterest profiles established up for this reason.
MoqHao is outfitted with numerous options that enable it to stealthily harvest sensitive data like device metadata, contacts, SMS messages, and shots, contact specific numbers with silent method, and help/disable Wi-Fi, among the many others.
McAfee stated it has documented the findings to Google, which is stated to be “already operating on the implementation of mitigations to prevent this kind of auto-execution in a long run Android model.”
The enhancement arrives as Chinese cybersecurity agency QiAnXin exposed that a beforehand mysterious cybercrime syndicate named Bigpanzi has been linked to the compromise of Android-dependent sensible TVs and set-leading boxes (STBs) in buy to corral them into a botnet for conducting dispersed denial-of-assistance (DDoS) attacks.

The operation, energetic given that at the very least 2015, is estimated to handle a botnet comprising 170,000 day-to-day lively bots, most of which are located in Brazil. Having said that, 1.3 million distinctive Brazilian IP addresses have been affiliated with Bigpanzi due to the fact August 2023.
The infections are designed probable by tricking people into setting up booby-trapped applications for streaming pirated videos and Tv set displays by way of sketchy internet sites. The campaign was 1st disclosed by Russian antivirus seller Doctor Web in September 2023.
“The moment set up, these gadgets remodel into operational nodes in their illicit streaming media system, catering to expert services like targeted traffic proxying, DDoS attacks, OTT content material provision, and pirate site visitors,” QiAnXin scientists explained.
“The potential for Bigpanzi-managed TVs and STBs to broadcast violent, terroristic, or pornographic written content, or to hire progressively convincing AI-generated movies for political propaganda, poses a sizeable menace to social get and security.”
Found this short article attention-grabbing? Adhere to us on Twitter and LinkedIn to read through more unique written content we write-up.
Some parts of this write-up are sourced from:
thehackernews.com


 Hands-on Review: Myrror Security Code-Aware and Attack-Aware SCA
Hands-on Review: Myrror Security Code-Aware and Attack-Aware SCA