The North Korean menace actor acknowledged as Kimsuky has been observed concentrating on investigate institutes in South Korea as portion of a spear-phishing campaign with the ultimate target of distributing backdoors on compromised techniques.
“The threat actor ultimately employs a backdoor to steal details and execute commands,” the AhnLab Security Emergency Reaction Heart (ASEC) reported in an examination posted final week.
The attack chains begin with an import declaration lure that’s actually a destructive JSE file that contains an obfuscated PowerShell script, a Base64-encoded payload, and a decoy PDF doc.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The up coming phase entails opening the PDF file as a diversionary tactic, whilst the PowerShell script is executed in the track record to start the backdoor.
The malware, for its component, is configured to collect network information and other pertinent data (i.e., host title, consumer name, and functioning program model) and transmit the encoded details to a distant server.
It really is also able of jogging commands, executing extra payloads, and terminating by itself, turning it into a backdoor for distant entry to the contaminated host.
Approaching WEBINAR Cracking the Code: Find out How Cyber Attackers Exploit Human Psychology
Ever questioned why social engineering is so successful? Dive deep into the psychology of cyber attackers in our impending webinar.
Be part of Now
Kimsuky, energetic considering the fact that at least 2012, started off off focusing on South Korean government entities, believe tanks, and folks discovered as authorities in various fields, just before expanding its victimology footprint to encompass Europe, Russia, and the U.S.
Before this month, the U.S. Treasury Section sanctioned Kimsuky for gathering intelligence to support North Korea’s strategic objectives, including geopolitical situations, overseas policy, and diplomatic endeavours.
“Kimsuky has concentrated its intelligence collection functions on overseas plan and national security issues similar to the Korean peninsula, nuclear policy, and sanctions,” cybersecurity agency ThreatMon pointed out in a current report.
The condition-sponsored team has also been observed leveraging booby-trapped URLs that, when clicked, down load a bogus ZIP archive masquerading as an update for the Chrome browser to deploy a malicious VBScript from Google Push that employs the cloud storage as a conduit for details exfiltration and command-and-control (C2).
Lazarus Group Goes Phishing on Telegram
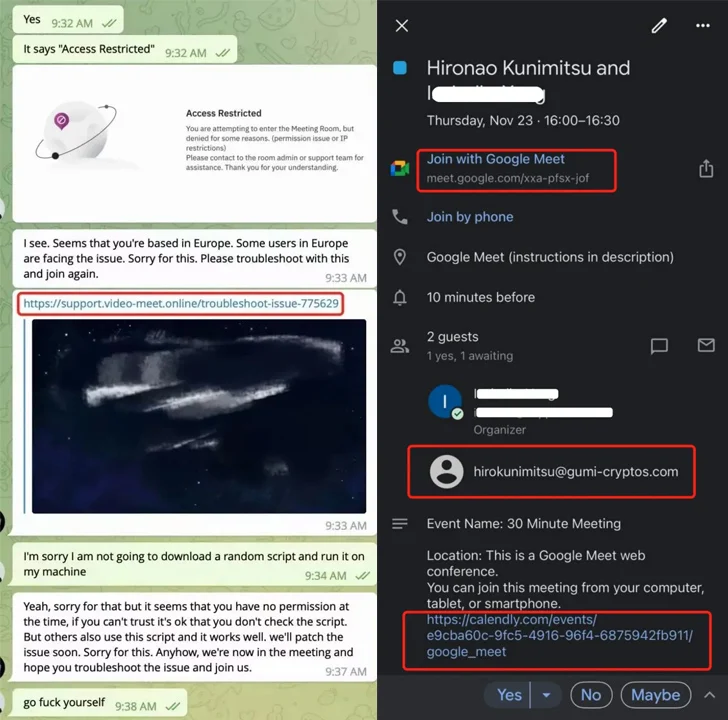
The growth comes as blockchain security company SlowMist implicated the notorious North Korea-backed outfit identified as the Lazarus Team in a prevalent phishing marketing campaign on Telegram targeting the cryptocurrency sector.
“More not long ago, these hackers have escalated their techniques by posing as respected financial commitment establishments to execute phishing scams in opposition to various cryptocurrency challenge teams,” the Singapore-based agency explained.

Right after creating rapport, the targets are deceived into downloading a destructive script under the guise of sharing an on line meeting hyperlink that facilitates crypto theft.
It also follows a report from the Seoul Metropolitan Police Company (SMPA) that accused the Lazarus sub-cluster codenamed Andariel of thieving technological information and facts about anti-plane weapon devices from domestic protection businesses and laundering ransomware proceeds back to North Korea.
It is estimated that additional than 250 documents amounting to 1.2 terabytes have been stolen in the attacks. To address up the tracks, the adversary is explained to have utilized servers from a local firm that “rents servers to subscribers with unclear identities” as an entry issue.
In addition, the group extorted 470 million received ($356,000) value of bitcoin from 3 South Korean corporations in ransomware attacks and laundered them by way of digital asset exchanges this sort of as Bithumb and Binance. It can be truly worth noting that Andariel has been joined to the deployment of Maui ransomware in the past.
Uncovered this posting attention-grabbing? Observe us on Twitter and LinkedIn to read through more unique content we write-up.
Some parts of this post are sourced from:
thehackernews.com


 Ransomware-as-a-Service: The Growing Threat You Can’t Ignore
Ransomware-as-a-Service: The Growing Threat You Can’t Ignore