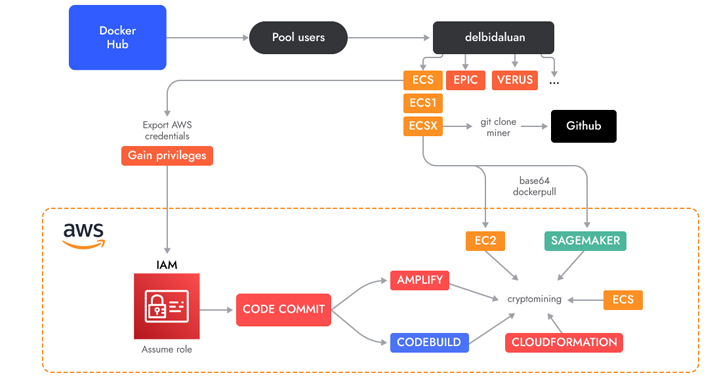
A novel cloud-native cryptojacking operation has established its eyes on uncommon Amazon Web Providers (AWS) choices such as AWS Amplify, AWS Fargate, and Amazon SageMaker to illicitly mine cryptocurrency.
The destructive cyber exercise has been codenamed AMBERSQUID by cloud and container security firm Sysdig.
“The AMBERSQUID operation was able to exploit cloud companies with out triggering the AWS need for approval of much more means, as would be the scenario if they only spammed EC2 occasions,” Sysdig security researcher Alessandro Brucato mentioned in a report shared with The Hacker Information.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“Concentrating on multiple providers also poses additional challenges, like incident reaction, because it needs acquiring and killing all miners in every single exploited assistance.”

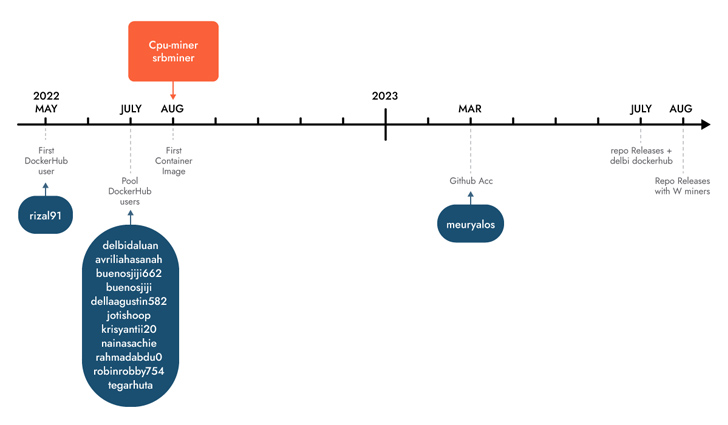
Sysdig stated it discovered the campaign adhering to an evaluation of 1.7 million images on Docker Hub, attributing it with average self-assurance to Indonesian attackers primarily based on the use of Indonesian language in scripts and usernames.
Some of these photographs are engineered to execute cryptocurrency miners downloaded from actor-controlled GitHub repositories, when others operate shell scripts focusing on AWS.
A key attribute is the abuse of AWS CodeCommit, which is applied to host personal Git repositories, to “produce a non-public repository which they then utilised in distinctive services as a source.”
The repository contains the supply code of an AWS Amplify app that, in change, is leveraged by a shell script to make a Amplify web app and in the long run launch the cryptocurrency miner.
The threat actors have also been noticed using shell scripts to carry out cryptojacking in AWS Fargate and SageMaker instances, incurring considerable compute costs for the victims.
Sysdig believed that AMBERSQUID could consequence in losses of far more than $10,000 for every day if it can be scaled to goal all AWS locations. A further more assessment of the wallet addresses employed reveals that the attackers have gained extra than $18,300 in revenues to day.
Future WEBINARIdentity is the New Endpoint: Mastering SaaS Security in the Contemporary Age
Dive deep into the foreseeable future of SaaS security with Maor Bin, CEO of Adaptive Protect. Discover why id is the new endpoint. Secure your spot now.
Supercharge Your Skills
This is not the 1st time Indonesian menace actors have been linked to cryptojacking strategies. In Could 2023, Permiso P0 Labs comprehensive an actor named GUI-vil which was spotted leveraging Amazon Web Services (AWS) Elastic Compute Cloud (EC2) occasions to carry out crypto mining operations.
“When most fiscally determined attackers goal compute services, these as EC2, it is essential to remember that lots of other companies also present access to compute resources (albeit it a lot more indirectly),” Brucato explained.
“It is quick for these companies to be ignored from a security point of view given that there is a lot less visibility compared to that readily available by way of runtime threat detection.”
Identified this report intriguing? Observe us on Twitter and LinkedIn to study additional exceptional content we write-up.
Some pieces of this article are sourced from:
thehackernews.com

 Think Your MFA and PAM Solutions Protect You? Think Again
Think Your MFA and PAM Solutions Protect You? Think Again