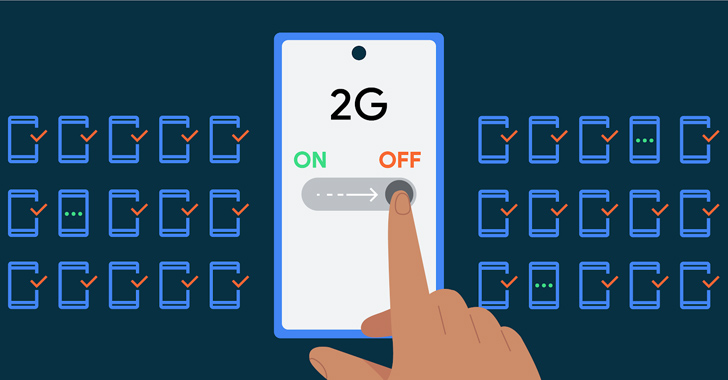
Google has launched a new security attribute in Android 14 that will allow IT administrators to disable aid for 2G cellular networks in their managed machine fleet.
The lookup huge stated it’s introducing a 2nd consumer environment to transform off assist, at the design amount, for null-ciphered cellular connections.
“The Android Security Design assumes that all networks are hostile to preserve consumers harmless from network packet injection, tampering, or eavesdropping on user traffic,” Roger Piqueras Jover, Yomna Nasser, and Sudhi Herle explained.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“Android does not depend on link-layer encryption to tackle this danger product. Rather, Android establishes that all network targeted traffic need to be close-to-conclude encrypted (E2EE).”
2G networks, in specific, utilize weak encryption and lack mutual authentication, rendering them inclined to around-the-air interception and targeted traffic decryption attacks by impersonating a serious 2G tower.

The menace posed by rogue mobile base stations signifies that it could be weaponized by destructive actors to intercept interaction website traffic, distribute malware, as effectively as launch denial-of-service (DoS) and adversary-in-the-center (AitM) attacks, posing surveillance concerns.
In June 2020, Amnesty Worldwide disclosed how a Moroccan journalist was qualified with network injection attacks, probable utilizing a bogus cell tower to supply the Pegasus spyware.
To make issues worse, an adversary could start a stealthy downgrade attack using superior cell-web page simulators (aka Stingrays) that power the handsets to connect to a 2G network by taking gain of the point that all current cellular units however function assist for 2G bands.
Google, in an endeavor to deal with some of these issues, included an alternative to disable 2G at the modem amount with Android 12 in early 2022. As a future rational action, the company is now placing in place a new restriction that prevents a device’s potential to downgrade to 2G connectivity.

Also tackled in the upcoming launch of the cell functioning system is the risk of null ciphers (non-encrypted method or GEA0) in business networks, which exposes user voice and SMS targeted visitors, such as a person-time passwords (OTPs) to trivial on-the-fly interception attacks.
The disclosure will come as Google mentioned that it is really enabling E2EE for RCS discussions in its Messages application for Android by default for new and current end users, although the enterprise notes that some people may perhaps be questioned to agree to Conditions of Assistance provided by their carrier network.
It also follows its plans to insert assistance for Message Layer Security (MLS) to the Messages app for interoperability throughout other messaging expert services.
Although Google has attempted to publicly pressurize Apple into adopting RCS, the iPhone maker seems to be information with iMessage for encrypted messaging. Nor has it expressed any interest in releasing a edition of iMessage for Android, forcing consumers texting amongst the two working devices to swap to a third-party messaging choice.
Identified this report attention-grabbing? Abide by us on Twitter and LinkedIn to browse far more distinctive material we write-up.
Some areas of this article are sourced from:
thehackernews.com

 Microsoft Releases Patches for 74 New Vulnerabilities in August Update
Microsoft Releases Patches for 74 New Vulnerabilities in August Update