A earlier undocumented menace actor dubbed SPIKEDWINE has been observed focusing on officials in European international locations with Indian diplomatic missions utilizing a new backdoor referred to as WINELOADER.
The adversary, in accordance to a report from Zscaler ThreatLabz, used a PDF file in emails that purported to occur from the Ambassador of India, inviting diplomatic team to a wine-tasting occasion on February 2, 2024.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The PDF doc was uploaded to VirusTotal from Latvia on January 30, 2024. That explained, there is evidence to counsel that this marketing campaign may have been energetic at least considering the fact that July 6, 2023, going by the discovery of a different equivalent PDF file uploaded from the very same region.
“The attack is characterised by its quite reduced volume and the superior methods, procedures, and procedures (TTPs) utilized in the malware and command-and-handle (C2) infrastructure,” security researchers Sudeep Singh and Roy Tay said.
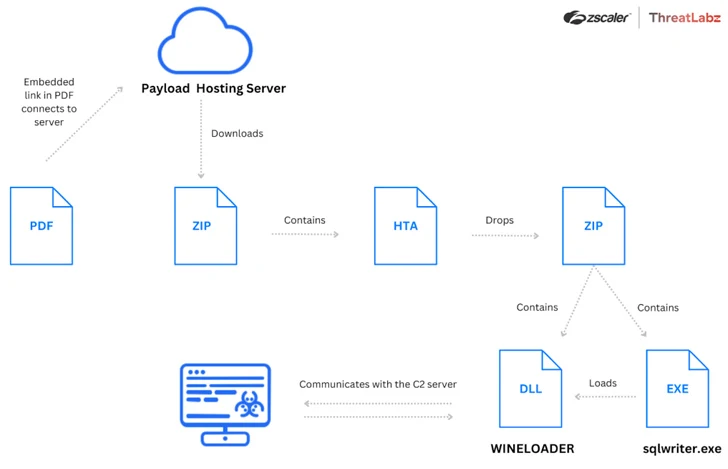
Central to the novel attack is the PDF file that will come embedded with a malicious connection that masquerades as a questionnaire, urging the recipients to fill it out in purchase to participate. Clicking on the backlink paves the way for an HTML application (“wine.hta”) that consists of obfuscated JavaScript code to retrieve an encoded ZIP archive bearing WINELOADER from the identical area.
The malware is packed with a main module that is built to Execute modules from the C2 server, inject by itself into an additional dynamic-link library (DLL), and update the slumber interval involving beacon requests.

A notable aspect of the cyber incursions is the use of compromised internet sites for C2 and hosting intermediate payloads. It is really suspected that the “C2 server only responds to precise types of requests at certain occasions,” thereby creating the attacks extra evasive.
“The danger actor place supplemental effort and hard work into remaining undetected by evading memory forensics and automatic URL scanning remedies,” the researchers claimed.
Discovered this post intriguing? Stick to us on Twitter and LinkedIn to read far more exclusive content we submit.
Some components of this post are sourced from:
thehackernews.com


 Lazarus Exploits Typos to Sneak PyPI Malware into Dev Systems
Lazarus Exploits Typos to Sneak PyPI Malware into Dev Systems