Authorities entities in the Center East are the concentrate on of new phishing campaigns that are designed to deliver a new initial obtain downloader dubbed IronWind.
The exercise, detected involving July and Oct 2023, has been attributed by Proofpoint to a threat actor it tracks below the name TA402, which is also recognized as Molerats, Gaza Cyber Gang, and shares tactical overlaps with a pro-Hamas hacking crew identified as APT-C-23 (aka Arid Viper).
“When it will come to point out-aligned threat actors, North Korea, Russia, China, and Iran commonly reap the lion’s share of consideration,” Joshua Miller, senior menace researcher at Proofpoint, reported in a statement shared with The Hacker Information.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“But TA402, a Center Eastern innovative persistent danger (APT) team that traditionally has operated in the interests of the Palestinian Territories, has continuously proven to be an intriguing danger actor able of extremely sophisticated cyber espionage with a concentrate on intelligence collection.”

Coinciding with the use of IronWind are constant updates to its malware shipping and delivery mechanisms, utilizing Dropbox links, XLL file attachments, and RAR archives to distribute IronWind.
The use of IronWind is a shift from prior attack chains, which were being linked to the propagation of a backdoor codenamed NimbleMamba in intrusions targeting Middle Jap governments and overseas policy imagine tanks.
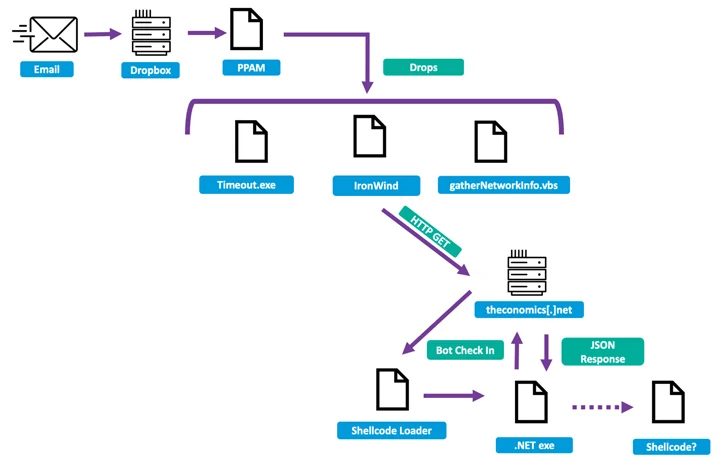
TA402’s most recent campaigns are characterized by the use of a compromised email account belonging to the Ministry of Overseas Affairs to ship phishing lures pointing to Dropbox links that facilitate the deployment of IronWind.
The downloader is engineered to contact an attacker-controlled server to fetch further payloads, like a put up-exploitation toolkit referred to as SharpSploit, pursuing a multi-phase sequence.
Subsequent social engineering campaigns in August and Oct 2023 have been discovered to leverage XLL file and RAR archive attachments embedded in email messages to trigger the deployment of IronWind. Yet another notable tactic utilized by the group is the reliance on geofencing methods to complicate detection endeavours.

“The ongoing conflict in the Center East does not seem to have hindered their ongoing operations, as they go on to iterate and use new and clever shipping solutions to bypass detection efforts,” Miller claimed.
“Employing complicated an infection chains and drumming up new malware to attack their targets, TA402 proceeds to interact in exceptionally targeted action with a robust focus on government entities centered in the Middle East and North Africa.”
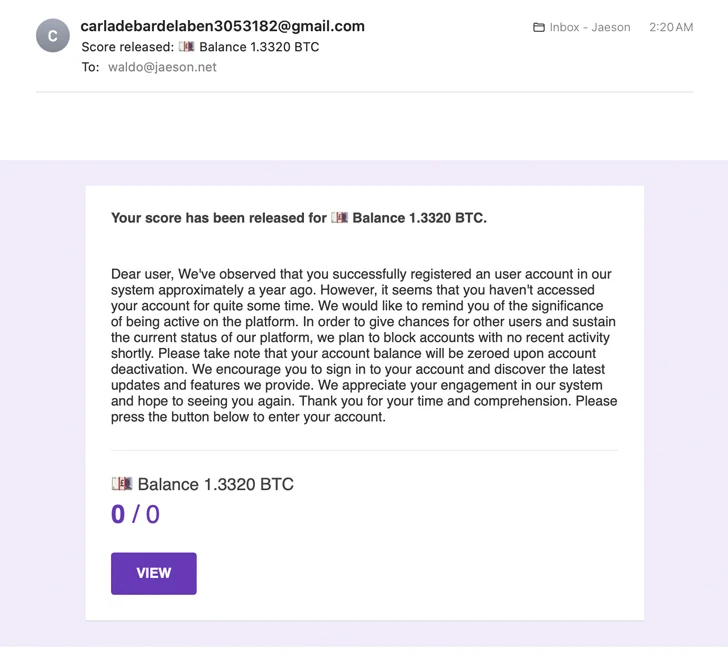
The improvement arrives as Cisco Talos unveiled that cybercriminals have been noticed exploiting the “Launch scores” characteristic of Google Types quizzes to produce email and orchestrate elaborate cryptocurrency ripoffs, highlighting the artistic methods threat actors vacation resort to in purchase to satisfy their aims.
“The e-mail originate from Google’s personal servers and therefore might have an less complicated time bypassing anti-spam protections and obtaining the victim’s inbox,” security researcher Jaeson Schultz said previous 7 days.
Found this report attention-grabbing? Comply with us on Twitter and LinkedIn to study a lot more special articles we put up.
Some areas of this short article are sourced from:
thehackernews.com


 Vietnamese Hackers Using New Delphi-Powered Malware to Target Indian Marketers
Vietnamese Hackers Using New Delphi-Powered Malware to Target Indian Marketers