Cryptocurrency people are being targeted with a new clipper malware strain dubbed Laplas by suggests of a different malware recognised as SmokeLoader.
SmokeLoader, which is delivered by usually means of weaponized paperwork despatched by spear-phishing e-mails, additional functions as a conduit for other commodity trojans like SystemBC and Raccoon Stealer 2., according to an analysis from Cyble.
Observed in the wild considering that circa 2013, SmokeLoader capabilities as a generic loader capable of distributing additional payloads on to compromised systems, these as info-stealing malware and other implants. In July 2022, it was identified to deploy a backdoor termed Amadey.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
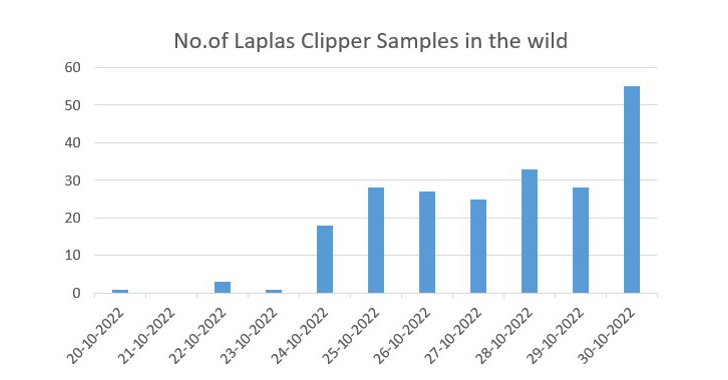
Cyble claimed it found more than 180 samples of the Laplas due to the fact Oct 24, 2022, suggesting a large deployment.
Clippers, also known as ClipBankers, tumble below a group of malware that Microsoft calls cryware, which are developed to steal crypto by preserving shut tabs on a victim’s clipboard exercise and swapping the first wallet deal with, if present, with an attacker-controlled tackle.
The target of clipper malware like Laplas is to hijack a digital currency transaction supposed for a respectable recipient to that owned by the risk actor.
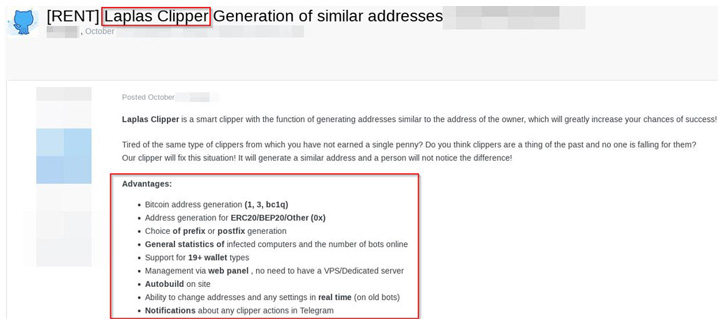
“Laplas is new clipper malware that generates a wallet deal with similar to the victim’s wallet address,” the scientists pointed out. “The sufferer will not notice the variance in the tackle, which appreciably boosts the probabilities of productive clipper activity.”

The newest clipper malware offers guidance for a wide range of wallets like Bitcoin, Ethereum, Bitcoin Income, Litecoin, Dogecoin, Monero, Ripple, Zcash, Dash, Ronin, TRON, Cardano, Cosmos, Tezos, Qtum, and Steam Trade URL. It’s priced from $59 a month to $549 a calendar year.
It also comes with its very own web panel that enables its purchasers to get details about the selection of contaminated desktops and the lively wallet addresses operated by the adversary, in addition to enabling for incorporating new wallet addresses.
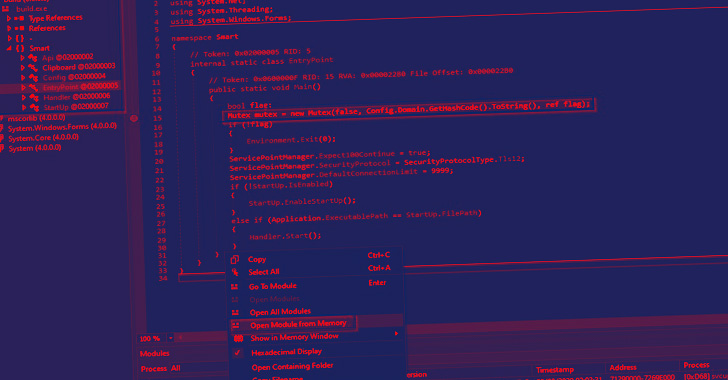
“SmokeLoader is a effectively-recognised, extremely configurable, successful malware that TAs [threat actors] are actively renovating,” the researchers concluded.
“It is a modular malware, indicating it can get new execution directions from [command-and-control] servers and down load supplemental malware for expanded features. In this case, the TAs use three various malware people for monetary achieve and other destructive uses.”
Observed this write-up attention-grabbing? Follow THN on Facebook, Twitter and LinkedIn to study more distinctive written content we article.
Some components of this posting are sourced from:
thehackernews.com

 U.S. Seizes Over 50K Bitcoin Worth $3.3 Billion Linked to Silk Road Dark Web
U.S. Seizes Over 50K Bitcoin Worth $3.3 Billion Linked to Silk Road Dark Web