The danger team tracked as REF2924 has been noticed deploying formerly unseen malware in its attacks aimed at entities in South and Southeast Asia.
The malware, dubbed NAPLISTENER by Elastic Security Labs, is an HTTP listener programmed in C# and is made to evade “network-based mostly forms of detection.”
REF2924 is the moniker assigned to an activity cluster joined to attacks against an entity in Afghanistan as nicely as the Foreign Affairs Workplace of an ASEAN member in 2022.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The risk actor’s modus operandi indicates overlaps with another hacking team dubbed ChamelGang, which was documented by Russian cybersecurity firm Favourable Systems in October 2021.
Attacks orchestrated by the group are said to have exploited internet-uncovered Microsoft Trade servers to deploy backdoors these as DOORME, SIESTAGRAPH, and ShadowPad.
DOORME, an Internet Facts Products and services (IIS) backdoor module, supplies remote obtain to a contested network and executes additional malware and tools.
SIESTAGRAPH employs Microsoft’s Graph API for command-and-handle through Outlook and OneDrive, and comes with abilities to run arbitrary commands as a result of Command Prompt, upload and obtain files to and from OneDrive, and consider screenshots.
ShadowPad is a privately marketed modular backdoor and a successor of PlugX, enabling menace actors to preserve persistent obtain to compromised pcs and operate shell instructions and abide by-on payloads.
The use of ShadowPad is noteworthy as it implies a opportunity backlink to China-centered hacking groups, which are acknowledged to utilize the malware in many strategies more than the several years.
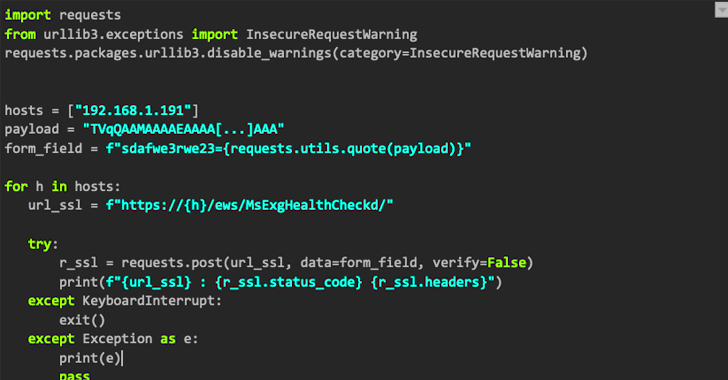
To this list of expanding malware arsenal made use of by REF2924 joins NAPLISTENER (“wmdtc.exe”), which masquerades as a respectable company Microsoft Dispersed Transaction Coordinator (“msdtc.exe”) in an attempt to fly under the radar and establish persistent entry.
WEBINARDiscover the Hidden Potential risks of Third-Party SaaS Apps
Are you conscious of the risks linked with 3rd-party application accessibility to your company’s SaaS applications? Sign up for our webinar to understand about the varieties of permissions getting granted and how to limit risk.
RESERVE YOUR SEAT
“NAPLISTENER generates an HTTP ask for listener that can method incoming requests from the internet, reads any information that was submitted, decodes it from Foundation64 structure, and executes it in memory,” security researcher Remco Sprooten stated.
Code assessment indicates the risk actor borrows or repurposes code from open resource tasks hosted on GitHub to produce its possess equipment, a indication that REF2924 may well be actively honing a raft of cyber weapons.
The findings also occur as a Vietnamese group was focused in late December 2022 by a formerly mysterious Windows backdoor codenamed PIPEDANCE to aid write-up-compromise and lateral motion pursuits, like Cobalt Strike.
Identified this report exciting? Abide by us on Twitter and LinkedIn to read through much more exceptional articles we submit.
Some sections of this post are sourced from:
thehackernews.com

 BreachForums Administrator Baphomet Shuts Down Infamous Hacking Forum
BreachForums Administrator Baphomet Shuts Down Infamous Hacking Forum