A pro-Hamas risk actor acknowledged as Gaza Cyber Gang is focusing on Palestinian entities working with an current version of a backdoor dubbed Pierogi.
The findings occur from SentinelOne, which has supplied the malware the name Pierogi++ owing to the reality that it is really implemented in the C++ programming language in contrast to its Delphi- and Pascal-primarily based predecessor.
“The latest Gaza Cybergang things to do show consistent concentrating on of Palestinian entities, with no observed significant improvements in dynamics due to the fact the begin of the Israel-Hamas war,” security researcher Aleksandar Milenkoski claimed in a report shared with The Hacker Information.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Gaza Cyber Gang, thought to be energetic because at minimum 2012, has a background of striking targets through the Center East, significantly Israel and Palestine, often leveraging spear-phishing as a strategy of first entry.
Impending WEBINAR Conquer AI-Driven Threats with Zero Believe in – Webinar for Security Gurus
Common security actions would not minimize it in modern earth. It is really time for Zero Have faith in Security. Protected your information like by no means right before.
Join Now
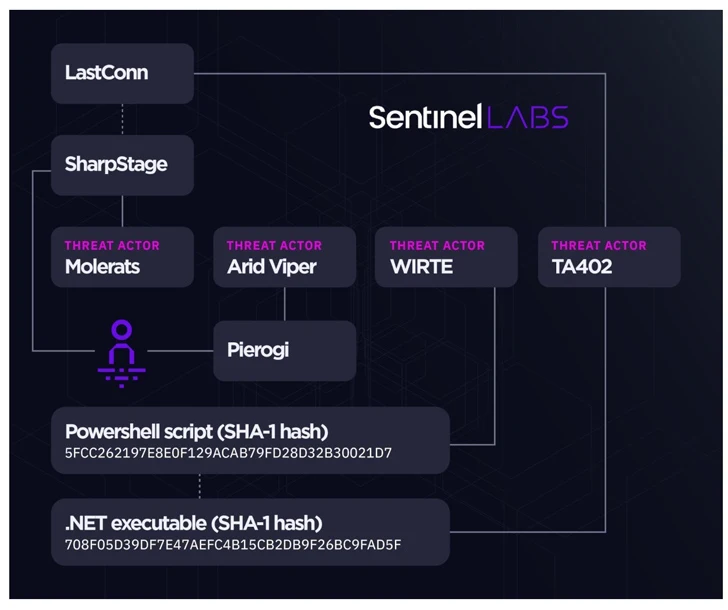
Some of the noteworthy malware family members in its arsenal contain BarbWire, DropBook, LastConn, Molerat Loader, Micropsia, NimbleMamba, SharpStage, Spark, Pierogi, PoisonIvy, and XtremeRAT between some others.
The menace actor is assessed to be a composite of many sub-teams that share overlapping victimology footprints and malware, these types of as Molerats, Arid Viper, and a cluster referred to as Procedure Parliament by Kaspersky.
In the latest months, the adversarial collective has been linked to a series of attacks that produce improvised variants of its Micropsia and Arid Gopher implants as effectively as a new initial obtain downloader dubbed IronWind.
The newest set of intrusions mounted by Gaza Cyber Gang has been located to leverage Pierogi++ and Micropsia. The initially recorded use of Pierogi++ goes back to late 2022.
Attack chains are characterised by the use of decoy files prepared in Arabic or English and pertaining to matters of curiosity to Palestinians to deliver the backdoors.
Cybereason, which get rid of light-weight on Pierogi in February 2020, described it as an implant that lets attackers to spy on specific victims and that the “commands applied to talk with the [command-and-control] servers and other strings in the binary are penned in Ukrainian.”

“The backdoor might have been acquired in underground communities rather than house-developed,” it assessed at the time.
Both Pierogi and Pierogi++ are equipped to choose screenshots, execute commands, and obtain attacker-offered documents. A different notable facet is that the up-to-date artifacts no extended feature any Ukrainian strings in the code.
SentinelOne’s investigation into Gaza Cyber Gang’s functions have also yielded tactical connections concerning two disparate campaigns referred to as Big Bang and Operation Bearded Barbie, in addition to reinforcing ties amongst the danger actor and WIRTE, as formerly disclosed by Kaspersky in November 2021.
The sustained focus on Palestine notwithstanding, the discovery of Pierogi++ underscores that the group proceeds to refine and retool its malware to make certain effective compromise of targets and to retain persistent access to their networks.
“The observed overlaps in concentrating on and malware similarities across the Gaza Cybergang sub-groups soon after 2018 suggests that the team has likely been undergoing a consolidation course of action,” Milenkoski claimed.
“This maybe incorporates the development of an internal malware improvement and upkeep hub and/or streamlining provide from exterior sellers.”
Identified this posting fascinating? Observe us on Twitter and LinkedIn to examine additional unique content material we post.
Some parts of this short article are sourced from:
thehackernews.com


 Iranian State-Sponsored OilRig Group Deploys 3 New Malware Downloaders
Iranian State-Sponsored OilRig Group Deploys 3 New Malware Downloaders