Chromium-based web browsers are the target of a new malware known as Rilide that masquerades by itself as a seemingly authentic extension to harvest sensitive knowledge and siphon cryptocurrency.
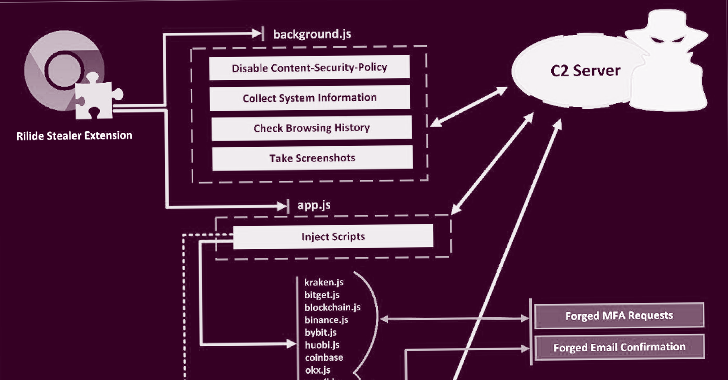
“Rilide malware is disguised as a authentic Google Travel extension and enables risk actors to have out a broad spectrum of malicious pursuits, which includes monitoring
searching heritage, getting screenshots, and injecting destructive scripts to withdraw funds from different cryptocurrency exchanges,” Trustwave SpiderLabs Exploration explained in a report shared with The Hacker News.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
What is more, the stealer malware can display solid dialogs to deceive end users into moving into a two-factor authentication code to withdraw electronic property.
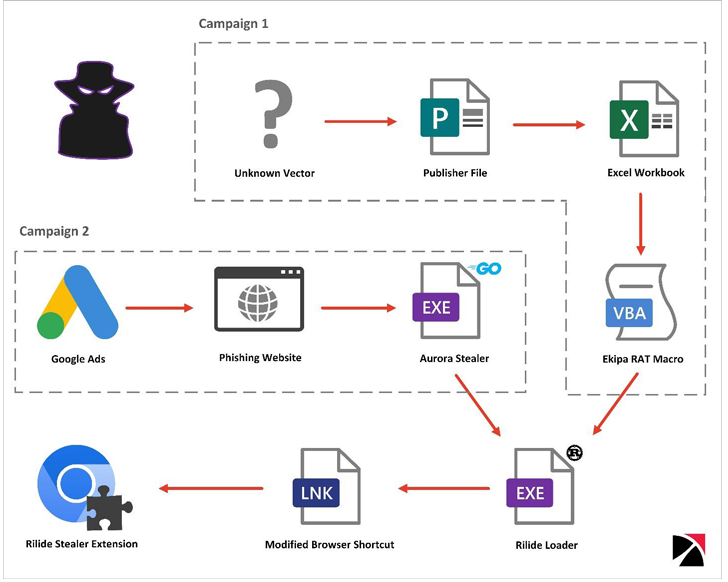
Trustwave stated it recognized two unique strategies involving Ekipa RAT and Aurora Stealer that led to the installation of the malicious browser extension.
Though Ekipa RAT is distributed by way of booby-trapped Microsoft Publisher documents, rogue Google Advertisements act as the supply vector for Aurora Stealer – a system that is grow to be ever more typical in the latest months.
Both equally the attack chains facilitate the execution of a Rust-centered loader that, in transform, modifies the browser’s LNK shortcut file and will make use of the “–load-extension” command line switch to launch the add-on.
The specific origins of Rilide is unknown, but Trustwave reported it was ready to come across an underground forum put up produced in March 2022 by a menace actor advertising the sale of a botnet with very similar functionalities.
A part of the malware’s source code has considering that identified its way to the discussion boards subsequent what appears to be an unresolved payment dispute.
THN WEBINARBecome an Incident Response Pro!
Unlock the secrets to bulletproof incident reaction – Learn the 6-Phase system with Asaf Perlman, Cynet’s IR Leader!
Never Overlook Out – Conserve Your Seat!
1 noteworthy aspect executed in the leaked resource code is the means to swap cryptocurrency wallet addresses in the clipboard with an actor-controlled deal with really hard-coded in the sample.
Moreover, a command-and-handle (C2) tackle specified in the Rilide code has designed it probable to determine numerous GitHub repositories belonging to a person named gulantin that comprise loaders for the extension.
“The Rilide stealer is a key instance of the increasing sophistication of destructive browser extensions and the risks they pose,” Trustwave concluded.
“Though the upcoming enforcement of manifest v3 may perhaps make it far more demanding for threat actors to run, it is not likely to fix the issue fully as most of the functionalities leveraged by Rilide will nonetheless be readily available.”
Located this report exciting? Adhere to us on Twitter and LinkedIn to browse far more exclusive content material we article.
Some elements of this short article are sourced from:
thehackernews.com

 TikTok Fined £12.7m For Violating UK Data Privacy Laws
TikTok Fined £12.7m For Violating UK Data Privacy Laws