Microsoft on Thursday disclosed details of a new vulnerability that could make it possible for an attacker to bypass security limits in macOS and consider complete command of the machine to complete arbitrary operations on the gadget without the need of having flagged by common security answers.
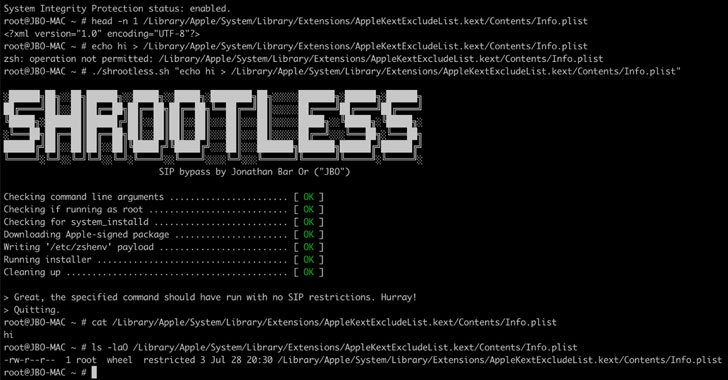
Dubbed “Shrootless” and tracked as CVE-2021-30892, the “vulnerability lies in how Apple-signed offers with post-set up scripts are put in,” Microsoft 365 Defender Research Team’s Jonathan Bar Or mentioned in a specialized compose-up. “A malicious actor could develop a specially crafted file that would hijack the installation approach.”


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Technique Integrity Protection (SIP) aka “rootless” is a security element launched in OS X El Capitan that’s intended to protect the macOS working program by restricting a root consumer from executing unauthorized code or carrying out functions that may possibly compromise technique integrity.
Specially, SIP enables modification of protected elements of the procedure — such as /Procedure, /usr, /bin, /sbin, and /var — only by processes that are signed by Apple or those people that have unique entitlements to write to program data files, like Apple application updates and Apple installers, while also mechanically authorizing apps that are downloaded from the Mac Application Store.
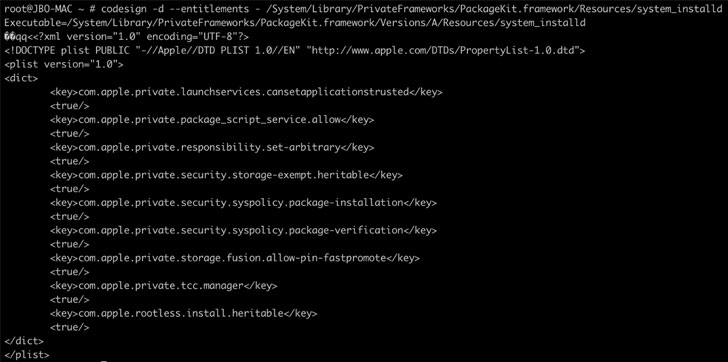
Microsoft’s investigation into the security technology seemed at macOS processes entitled to bypass SIP protections, foremost to the discovery of a software package set up daemon known as “method_installd” that allows any of its boy or girl procedures to absolutely circumvent SIP filesystem restrictions.
As a result when an Apple-signed offer is being put in, it invokes the process_installd daemon, and any write-up-put in scripts contained in the deal is executed by invoking a default shell, which is Z shell (zsh) on macOS.
“Apparently, when zsh starts, it appears to be for the file /and so on/zshenv, and — if identified — runs instructions from that file routinely, even in non-interactive method,” Bar Or claimed. “Consequently, for attackers to accomplish arbitrary operations on the device, a completely dependable route they could consider would be to create a destructive /etcetera/zshenv file and then wait around for system_installd to invoke zsh.”
Effective exploitation of CVE-2021-30892 could enable a malicious software to modify protected components of the file program, such as the ability to install malicious kernel drivers (aka rootkits), overwrite method data files, or set up persistent, undetectable malware. Apple claimed it remediated the trouble with supplemental limits as aspect of security updates pushed on October 26, 2021.
“Security technology like SIP in macOS products serves equally as the device’s developed-in baseline protection and the previous line of defense in opposition to malware and other cybersecurity threats,” Bar Or stated. “However, destructive actors continue on to discover ground breaking ways of breaching these obstacles for these quite very same good reasons.”
Discovered this posting intriguing? Adhere to THN on Fb, Twitter and LinkedIn to browse more distinctive material we post.
Some elements of this post are sourced from:
thehackernews.com

 Winter is Coming for CentOS 8
Winter is Coming for CentOS 8