A earlier unfamiliar advanced persistent risk (APT) is targeting iOS devices as section of a advanced and long-running cellular campaign dubbed Operation Triangulation that commenced in 2019.
“The targets are contaminated employing zero-simply click exploits by means of the iMessage system, and the malware operates with root privileges, attaining entire manage more than the product and user facts,” Kaspersky stated.
The Russian cybersecurity organization reported it learned traces of compromise after creating offline backups of the targeted devices.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The attack chain commences with the iOS machine receiving a information via iMessage that consists of an attachment bearing the exploit.
The exploit is reported to be zero-click, this means the receipt of the message triggers the vulnerability with no requiring any user conversation in order to realize code execution.
Impending WEBINAR 🔐 Mastering API Security: Comprehending Your Genuine Attack Floor
Explore the untapped vulnerabilities in your API ecosystem and take proactive techniques to ironclad security. Sign up for our insightful webinar!
Be part of the Session.ad-button,.advertisement-label,.advertisement-label:right afterdisplay screen:inline-block.ad_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px strong #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-prime-still left-radius:25px-moz-border-radius-topleft:25px-webkit-border-base-right-radius:25px-moz-border-radius-bottomright:25px.ad-labelfont-size:13pxmargin:20px 0font-body weight:600letter-spacing:.6pxcolor:#596cec.advert-label:right afterwidth:50pxheight:6pxcontent:”border-top:2px good #d9deffmargin: 8px.advertisement-titlefont-sizing:21pxpadding:10px 0font-pounds:900text-align:leftline-peak:33px.ad-descriptiontextual content-align:leftfont-dimension:15.6pxline-peak:26pxmargin:5px !importantcolor:#4e6a8d.advertisement-buttonpadding:6px 12pxborder-radius:5pxbackground-coloration:#4469f5font-dimension:15pxcolor:#fff!importantborder:0line-height:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-body weight:500letter-spacing:.2px
It can be also configured to retrieve further payloads for privilege escalation and fall a ultimate stage malware from a remote server that Kaspersky explained as a “entirely-highlighted APT platform.”
The implant, which runs with root privileges, is capable of harvesting sensitive information and outfitted to operate code downloaded as plugin modules from the server.
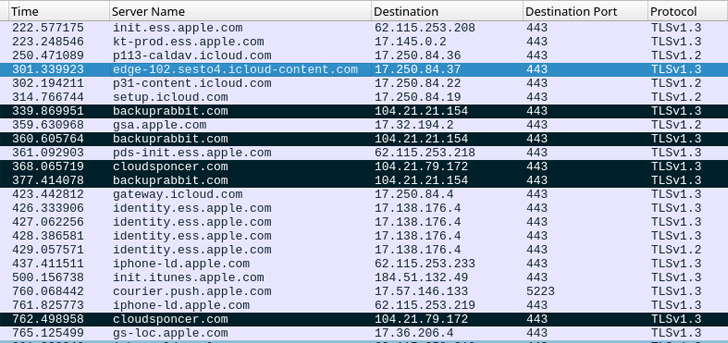
In the ultimate section, equally the preliminary information and the exploit in the attachment are deleted to erase any traces of the infection.
“The destructive toolset does not guidance persistence, most likely thanks to the restrictions of the [operating system],” Kaspersky stated. “The timelines of numerous devices reveal that they may well be reinfected after rebooting.”
The exact scale and scope of the marketing campaign continue to be unclear, but the business explained the attacks are ongoing, with productive bacterial infections penetrating equipment managing iOS 15.7, which was launched on September 12, 2022.
Uncovered this report attention-grabbing? Observe us on Twitter and LinkedIn to read extra exclusive articles we post.
Some components of this post are sourced from:
thehackernews.com


 Unmasking XE Group: Experts Reveal Identity of Suspected Cybercrime Kingpin
Unmasking XE Group: Experts Reveal Identity of Suspected Cybercrime Kingpin