Cybersecurity scientists have unmasked the id of a single of the persons who is thought to be connected with the e-crime actor recognized as XE Team.
According to Menlo Security, which pieced collectively the details from different online sources, “Nguyen Huu Tai, who also goes by the names Joe Nguyen and Thanh Nguyen, has the strongest likelihood of staying concerned with the XE Team.”
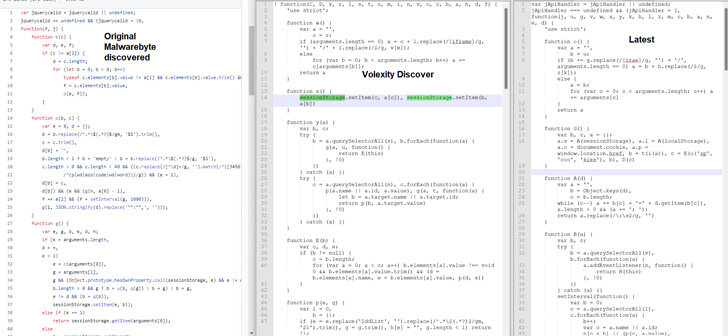
XE Group (aka XeThanh), formerly documented by Malwarebytes and Volexity, has a record of carrying out cyber criminal activities since at minimum 2013. It can be suspected to be a danger actor of Vietnamese origin.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Some of the entities qualified by the menace actor span federal government companies, design companies, and healthcare sectors.
It’s regarded to compromise internet-exposed servers with acknowledged exploits and monetize the intrusions by installing password theft or credit history card skimming code for on the net expert services.
“As considerably again as 2014, the threat actor was found producing AutoIT scripts that routinely created e-mail and a rudimentary credit history card validator for stolen credit cards,” the cybersecurity firm stated.
Before this March, U.S. cybersecurity and intelligence authorities disclosed XE Group’s tries to exploit a critical three-yr-outdated security flaw in Development Telerik equipment (CVE-2019-18935, CVSS rating: 9.8) to get hold of a foothold.
Upcoming WEBINAR 🔐 Mastering API Security: Knowing Your Real Attack Surface area
Learn the untapped vulnerabilities in your API ecosystem and choose proactive methods towards ironclad security. Be a part of our insightful webinar!
Be part of the Session.advertisement-button,.advertisement-label,.ad-label:immediately afterexhibit:inline-block.ad_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px stable #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-best-still left-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-ideal-radius:25px-moz-border-radius-bottomright:25px.advert-labelfont-dimensions:13pxmargin:20px 0font-bodyweight:600letter-spacing:.6pxcolor:#596cec.ad-label:soon afterwidth:50pxheight:6pxcontent:”border-prime:2px sound #d9deffmargin: 8px.ad-titlefont-dimension:21pxpadding:10px 0font-weight:900text-align:leftline-peak:33px.ad-descriptiontext-align:leftfont-dimensions:15.6pxline-peak:26pxmargin:5px !importantcolor:#4e6a8d.advert-buttonpadding:6px 12pxborder-radius:5pxbackground-shade:#4469f5font-size:15pxcolor:#fff!importantborder:0line-top:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-body weight:500letter-spacing:.2px
The adversary has also attempted to achieve obtain to company networks in the past by means of phishing e-mail despatched out utilizing fraudulent domains mimicking legit businesses this sort of as PayPal and eBay.
Other than camouflaging .EXE information as .PNG data files to keep away from detection, pick attacks have utilized a web shell dubbed ASPXSpy to acquire command of vulnerable units.
“XE Group continues to be a continued danger to many sectors, like government businesses, development organizations, and healthcare vendors,” the scientists stated.
Observed this post attention-grabbing? Adhere to us on Twitter and LinkedIn to read more special written content we publish.
Some components of this report are sourced from:
thehackernews.com


 Malicious PyPI Packages Using Compiled Python Code to Bypass Detection
Malicious PyPI Packages Using Compiled Python Code to Bypass Detection