Researchers have discovered a novel attack on the Python Package deal Index (PyPI) repository that employs compiled Python code to sidestep detection by software security instruments.
“It may possibly be the initially provide chain attack to get advantage of the actuality that Python bytecode (PYC) documents can be straight executed,” ReversingLabs analyst Karlo Zanki reported in a report shared with The Hacker Information.
The package deal in query is fshec2, which was taken out from the deal registry on April 17, 2023, following dependable disclosure on the very same working day.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
PYC data files are compiled bytecode documents that are created by the Python interpreter when a Python application is executed.
“When a module is imported for the initially time (or when the source file has changed because the present compiled file was designed) a .pyc file that contains the compiled code must be designed in a __pycache__ subdirectory of the directory made up of the .py file,” describes the Python documentation.
The deal, for every the software supply chain security firm, contains 3 files – _init_.py, principal.py, and comprehensive.pyc – the past of which harbors destructive features.
“The entry stage of the offer was located in the __init__.py file, which imports a perform from the other plaintext file, most important.py, which consists of Python resource code liable for loading of the Python compiled module situated in one particular of the other documents, complete.pyc,” Zanki pointed out.
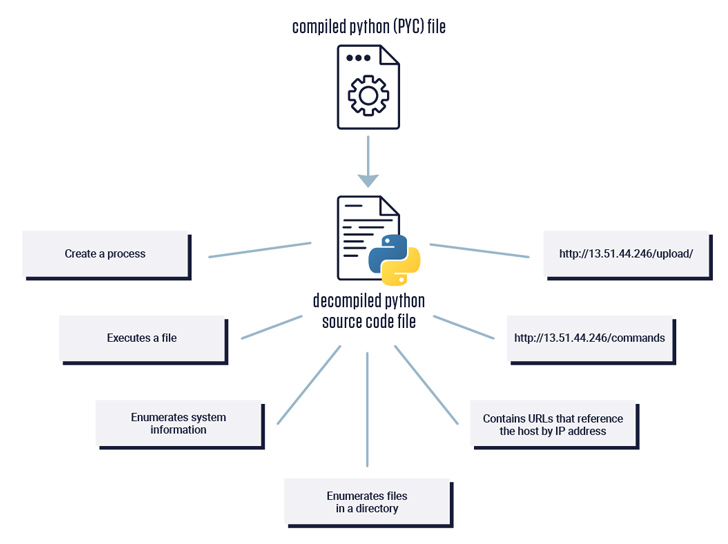
This, in switch, is obtained by creating use of the importlib bundle (as opposed to a frequent import) to load and execute the code existing in the .pyc file.
An assessment of the reverse-engineered edition of the PYC file reveals that it is really configured to collect usernames, hostnames, and directory listings, as perfectly as fetch commands to be executed on the host from a hard-coded server (13.51.44[.]246).
Approaching WEBINAR 🔐 Mastering API Security: Understanding Your True Attack Area
Find the untapped vulnerabilities in your API ecosystem and consider proactive steps to ironclad security. Sign up for our insightful webinar!
Join the Session.advertisement-button,.ad-label,.advert-label:soon afterdisplay screen:inline-block.ad_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px reliable #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-leading-still left-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-suitable-radius:25px-moz-border-radius-bottomright:25px.advert-labelfont-dimensions:13pxmargin:20px 0font-pounds:600letter-spacing:.6pxcolor:#596cec.ad-label:just afterwidth:50pxheight:6pxcontent:”border-top rated:2px good #d9deffmargin: 8px.ad-titlefont-size:21pxpadding:10px 0font-weight:900textual content-align:leftline-peak:33px.advertisement-descriptiontext-align:leftfont-measurement:15.6pxline-height:26pxmargin:5px !importantcolor:#4e6a8d.advert-buttonpadding:6px 12pxborder-radius:5pxbackground-coloration:#4469f5font-dimension:15pxcolor:#fff!importantborder:0line-peak:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-weight:500letter-spacing:.2px
ReversingLabs mentioned it also noticed the module download and operate one more Python script which is accountable for fetching new commands put inside of a file that can be tweaked at will by the danger actor to issue various recommendations.
Further more evaluation of the command-and-control server unearthed a misconfiguration that manufactured it doable to download data files by their ID, which are numbered in sequential buy (starting from 1), sans any authorization. This suggests that the attack was most very likely not orchestrated by a sophisticated actor.
The development is a continuation of attempts on the portion of danger actors to undertake unique obfuscation techniques in buy to evade detection from security answers.
“Loader scripts these as these learned in the fshec2 offer have a minimal amount of money of Python code and conduct a basic motion: loading of a compiled Python module,” Zanki reported. “It just comes about to be a malicious module.”
Identified this posting exciting? Adhere to us on Twitter and LinkedIn to examine additional exceptional content material we put up.
Some pieces of this report are sourced from:
thehackernews.com


 How Wazuh Improves IT Hygiene for Cyber Security Resilience
How Wazuh Improves IT Hygiene for Cyber Security Resilience