IT hygiene is a security greatest follow that guarantees that electronic property in an organization’s natural environment are secure and working effectively. Excellent IT cleanliness features vulnerability administration, security configuration assessments, protecting asset and procedure inventories, and comprehensive visibility into the routines happening in an surroundings.
As technology advances and the tools employed by cybercriminals and cybersecurity pros evolve, the approaches utilized to carry out cyber attacks differ centered on their complexity and uniqueness. Danger actors consistently concentrate on organizations working towards very poor IT cleanliness to exploit recognised security weaknesses and human error. Security directors can defend against cyberattacks by employing very good IT hygiene procedures like whitelisting plans, keeping systems up to date, and extra.
Getting full visibility into the IT belongings is elementary to producing an effective security tactic. The emergence of shadow IT, like rogue belongings, software program, or consumer accounts, can build a blind location that risk actors can use as an attack vector. IT hygiene methods handle the issue of visibility, making certain IT property are sufficiently shielded consequently reducing the attack area.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Frequent problems faced by businesses practising very poor IT hygiene
The following are some of the issues companies confront as a result of poor IT cleanliness:
Why is IT cleanliness significant?
IT hygiene is critical for protecting the security and resilience of an organization’s IT infrastructure. By adhering to excellent IT cleanliness procedures, organizations can make sure the security, performance, and trustworthiness of their IT infrastructure when also complying with regulatory demands and minimizing fees. IT hygiene is critical as follows.
First of all, corporations can appreciably improve their security posture by practising excellent IT cleanliness as a result of comprehensive vulnerability and patch management. This follow assures the safety of endpoints and applications from malicious attacks.
Additionally, by retaining very good IT hygiene, businesses can effectively lessen their attack surface area as they have higher visibility of all their IT property.
At last, adhering to IT superior cleanliness practices aids in meeting regulatory necessities and business benchmarks and conserving costs. Proactive monitoring and response can support corporations in keeping away from legal sanctions and financial and reputational destruction ensuing from information breaches and cyberattacks.
How Wazuh allows improve IT hygiene
Wazuh is a cost-free, open up supply security system that delivers unified XDR and SIEM abilities. It allows give security throughout workloads on cloud and on-premises environments. It provides a centralized look at for checking, detecting, and alerting security events on monitored endpoints and cloud workloads.
This portion highlights several Wazuh abilities crucial to maintaining your network clean and secure.
1 —System stock: IT cleanliness commences with real-time visibility of electronic belongings in an setting and the functions happening in them. Real-time visibility contains an up-to-date stock of property and method. It involves instantly determining risks, vulnerabilities, and misconfigurations throughout those people property. The Wazuh program stock functionality collects appropriate info like components, running techniques, ports, packages, Windows updates, and network interfaces on monitored endpoints. This facts is critical to acquiring an successful IT hygiene practice that increases the general security posture of an corporation. For example, the program stock knowledge consists of a list of open up ports on endpoints which can support security directors in determining and closing unwanted ports, thereby cutting down the attack surface area.
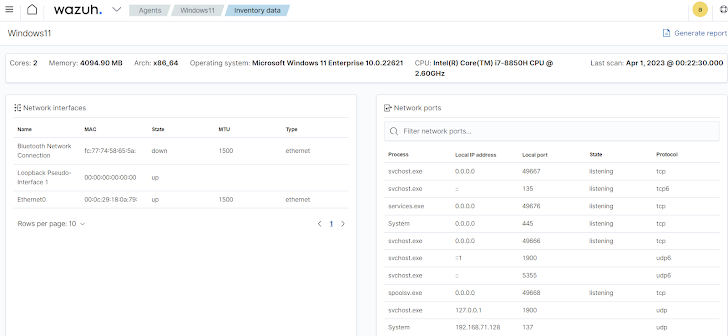 Determine 1: Wazuh dashboard showing inventory facts of a monitored endpoint.
Determine 1: Wazuh dashboard showing inventory facts of a monitored endpoint.
2 — Security Configuration Evaluation (SCA): This involves conducting an substantial analysis of security issues on monitored endpoints. It really is centered on compliance expectations to increase security posture. Most effective IT hygiene tactics involve security directors to conduct configuration assessments frequently to recognize and remediate vulnerabilities and misconfigurations on endpoints. Security configuration assessments and endpoint hardening properly lessen an organization’s attack area.
The Wazuh SCA functionality assesses program configurations and triggers alerts when these configurations do not meet secure technique policies. Relying on the marketplace, IT hygiene guarantees that endpoints comply with HIPAA, PCI DSS, NIST 800-53 compliance specifications, and CIS benchmarks.
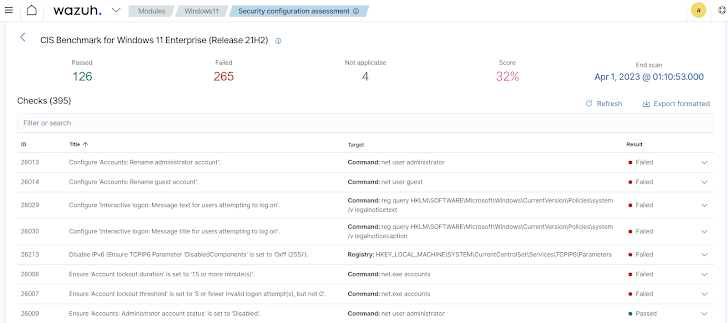 Figure 2: Wazuh dashboard displaying SCA report of a monitored endpoint.
Figure 2: Wazuh dashboard displaying SCA report of a monitored endpoint.
3 — Vulngrability management: This is a proactive and constant approach of determining, prioritizing, and remediating vulnerabilities on endpoints. The vulnerability management approach is crucial to retain IT cleanliness. The Wazuh Vulnerability Detector capability allows you uncover security vulnerabilities in the running method and programs put in on monitored endpoints. Security administrators can acquire needed actions to remediate vulnerabilities and increase IT hygiene.
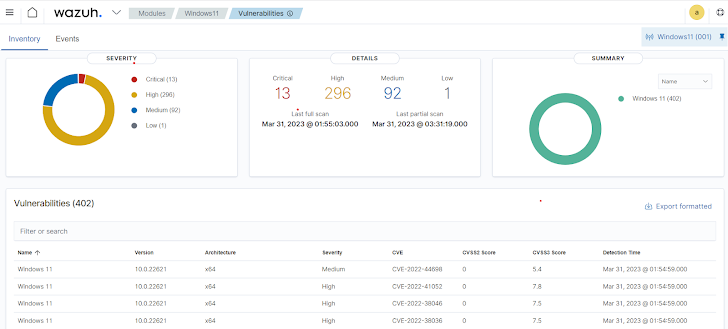 Figure 3: Wazuh dashboard exhibiting vulnerability report of a monitored endpoint.
Figure 3: Wazuh dashboard exhibiting vulnerability report of a monitored endpoint.
4 — Exgended danger detection and automatic reaction: This can help with IT cleanliness by continuously checking and analyzing endpoint activities in an organization’s natural environment. This steady checking assures proactive detection and reaction to threats or malicious routines. With an XDR/SIEM answer, security groups can rapidly determine and isolate contaminated endpoints, thus avoiding the distribute of malware in their organization network. Wazuh can help organizations monitor and secure their IT infrastructure by providing complete threat detection and automatic response abilities for endpoints. It helps to enhance an organization’s IT cleanliness techniques by providing ongoing monitoring, malware detection, incident response, and compliance capabilities.
Summary
In modern ever-shifting menace landscape, producing a superior IT hygiene program is necessary to prevent cyber criminals from triggering security breaches. By leveraging the abilities of Wazuh, corporations can proactively detect and respond to security threats and sustain a robust cyber security posture.
Wazuh is a absolutely free, open up resource SIEM and XDR answer that features comprehensive security for businesses. Wazuh enhances an organization’s IT hygiene making use of numerous capabilities to inform directors of vulnerabilities, suggest remediation methods, and reply to threats.
Wazuh has above 20 million annual downloads and thoroughly supports end users by a consistently increasing open resource group.
Found this report exciting? Stick to us on Twitter and LinkedIn to examine a lot more distinctive content we article.
Some elements of this write-up are sourced from:
thehackernews.com

 HMRC in New Tax Credits Scam Warning
HMRC in New Tax Credits Scam Warning