The National Institute of Specifications and Technology (NIST) on Thursday produced an updated cybersecurity assistance for controlling pitfalls in the source chain, as it ever more emerges as a profitable attack vector.
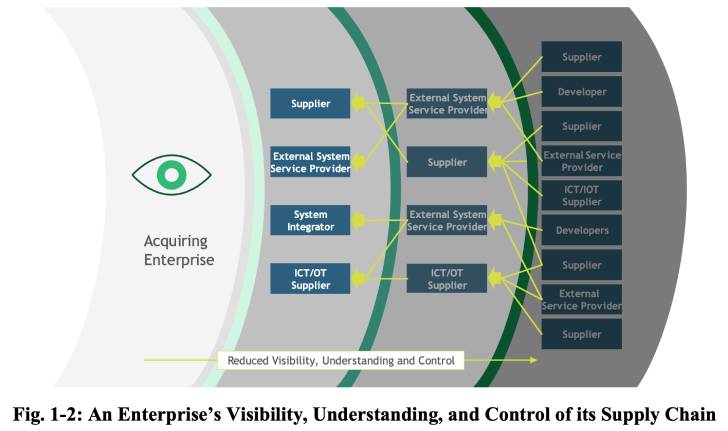
“It encourages companies to take into account the vulnerabilities not only of a finished solution they are thinking of applying, but also of its elements — which could have been created in other places — and the journey people factors took to arrive at their vacation spot,” NIST explained in a statement.
The new directive outlines important security controls and methods that entities must undertake to discover, assess, and respond to pitfalls at different stages of the offer chain, including the possibility of malicious functionality, flaws in third-party application, insertion of counterfeit components, and bad production and enhancement procedures.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The progress follows an Government Buy issued by the U.S. President on “Bettering the Nation’s Cybersecurity (14028)” previous Could, requiring federal government businesses to choose ways to “enhance the security and integrity of the software source chain, with a priority on addressing critical software program.”
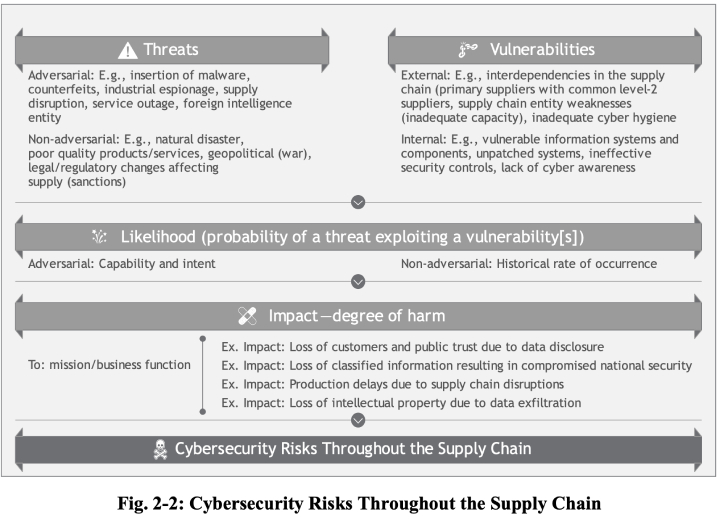
It also will come as cybersecurity threats in the supply chain have appear to the forefront in modern yrs, in part compounded by a wave of attacks focusing on commonly-made use of software program to breach dozens of downstream sellers all at at the time.
In accordance to the European Union Company for Cybersecurity’s (ENISA) Menace Landscape for Provide Chain Attacks, 62% of 24 attacks documented from January 2020 to early 2021 were identified to “exploit the trust of shoppers in their provider.”
“Controlling the cybersecurity of the supply chain is a have to have that is right here to remain,” said NIST’s Jon Boyens and a single of the publication’s authors. “If your company or business hasn’t started off on it, this is a complete software that can get you from crawl to walk to operate, and it can help you do so promptly.”
Observed this article exciting? Comply with THN on Facebook, Twitter and LinkedIn to examine a lot more exceptional content we publish.
Some areas of this write-up are sourced from:
thehackernews.com

 Google to Add Passwordless Authentication Support to Android and Chrome
Google to Add Passwordless Authentication Support to Android and Chrome