This article was prepared by Peter Gerdenitsch, Group CISO at Raiffeisen Lender Intercontinental, and is dependent on a presentation given all through Imvision’s Government Training Software, a collection of gatherings centered on how enterprises are using demand of the API security lifecycle.
Launching the “Security in Agile” application
Headquartered in Vienna, Raiffeisen Bank Global (RBI) operates throughout 14 international locations in Central and Jap Europe with about 45,000 staff members. Our target is on furnishing universal banking methods to shoppers, as properly as producing electronic banking solutions for the retail and corporate marketplaces. Appropriately, RBI has a significant R&D division, earning for a really huge community of IT and engineering experts all about Europe.
Back in 2019, we commenced shifting to a merchandise-led agile set up for RBI, introducing numerous security roles contributing and collaborating to accomplish our strategic plans. As element of this journey, we established the security champion job inside the DevSecOps crew for each individual of our items. In addition to our central “Security Style and design and Architecture “purpose, security specialists began working jointly to aid solutions in employing protected solutions.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Far more than anything at all, having ownership in excess of the security facet of their products intended security champions ended up properly-positioned to assure that security-related stories get prioritized for the duration of backlog meetings, in alignment with the item owner’s acceptable amounts of risk.
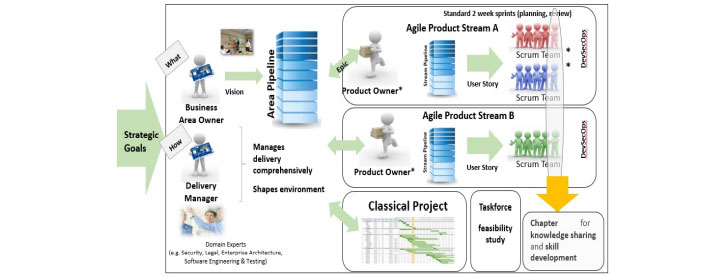
We also established up tribes consisting of a number of merchandise linked with a specific organization-line to foster a shared feeling of neighborhood. Each individual tribe was provided yet another job: the “security chapter lead”.
This part was tasked with supporting the other security champions in their tribe with specifications, risk evaluation, design and style styles and architecture, thanks to their enhanced know-how. These roles were being transparent so that the knowledge provider of security for each individual product and tribe was identified across the overall corporation.
Lastly, we established up a local community of follow, which involves month-to-month conferences where by security champions from all of the various items could satisfy to trade information, educate situation reports, and generally share information about their observe. We even more commenced supporting this local community endeavor with Monday bulletins, updates from the week, and in general encouraged an open trade of data, know-how, and practical experience.
Find out much more on how to acquire charge of the API security lifecycle
Security ‘Martial Arts’ coaching software
The plan was – and however is – to make the security winner a wholly volunteer-driven job, which at first had us apprehensive that we wouldn’t be capable to locate adequate willing volunteers. Fortuitously, the reverse was real, and we have been even capable to recruit two men and women for each and every place to cover holidays and unwell go away. Part of the achievements in all probability comes from the truth that we did not restrict the position in terms of track record, which meant we observed lots of volunteers from numerous IT and business enterprise functions as very well.
To further more guidance this purpose, in early 2020 we set up a schooling plan for our security champions dependent on the martial-arts’ belt procedure. It commenced with a 3-day basic training software in security that we known as Yellow Belt education. It took off and we immediately obtained insights into the plan, which resulted in the start of a slimmer 2-day version of the Yellow Belt that specific anyone intrigued in mastering much more about security.
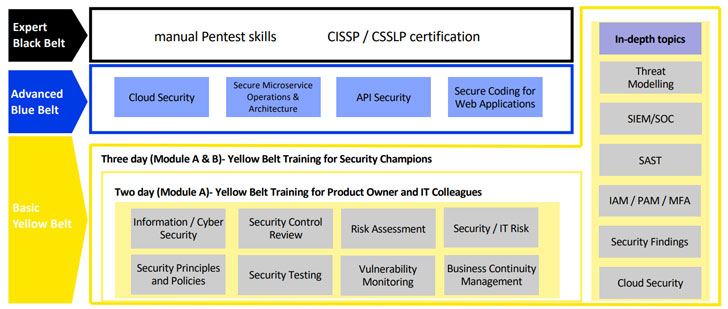
This shorter, generalized program for everyone was intended to foster collaboration and recognition throughout the firm by highlighting the significance of security in the product or service lifecycle and the rationale guiding the security winner software. The security winner program’s excess day was focused on studying additional about the RBI precise tools of the trade, especially the use of supply code scanning and id and obtain administration resources.
Over time we set up more, much more state-of-the-art education classes to support security champions do their careers additional effectively. For example, we have received an API security system and cloud security program to deepen our security-connected expertise in these domains. We also persuade skilled certification by means of exterior classes by furnishing our security champions with the price range and discovering time they require to just take them.
Getting demand of our API security lifecycle
In accordance with the Payment Provider Directive (PSD), around the previous several several years financial institutions have progressively been demanded – and predicted – to open up their APIs to empower consumers to accessibility monetary details easily, including by 3rd-party resources and applications.
This regulation catalyzed a solid pivot to API use that was already in the makingf, and RBI’s API posture and use substantially amplified. Around the earlier numerous yrs, RBI developed a lot of APIs: these days, our API Market has 100+ externally exposed APIs, though internally, we counted ~1,000 distinct APIs. The rise in API implementation and use introduced about security challenges, which prompted us to consider about approaches to handle API security.
As our API footprint was not confined to just people needed by PSD regulations, we quickly learned that we did not necessarily have reliable visibility into all APIs we deployed. Like lots of other enterprises throughout the world, we were being challenged with gaining a central perspective of APIs, looking at the high quantity and range of APIs in use – so we can ensure that the acceptable and adequate level of security is in put.
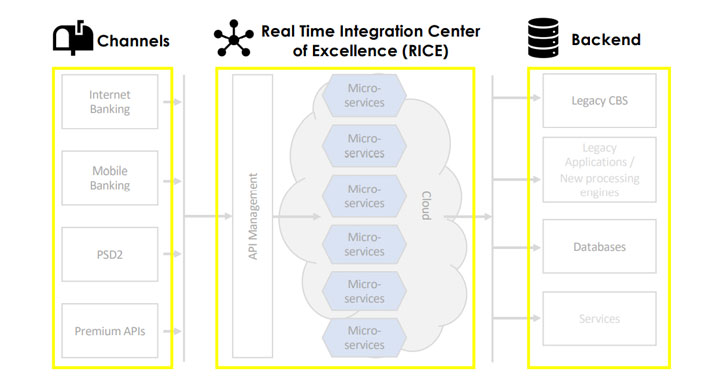
To address some of these difficulties, we resolved to set up the Authentic-Time Integration Center of Excellence (RICE), which serves as a central administration layer for RBI, such as APIs that hook up to the legacy core banking methods of the numerous subsidiaries and acquired companies.
As shown in the diagram below, the central API management layer has all the microservices certain collectively, serving the company performance for the APIs and connecting on the outside the house to the many channels and use scenarios. This layer is a gain-acquire for us, as it enables us to improve buyer experience, efficiency — and security.
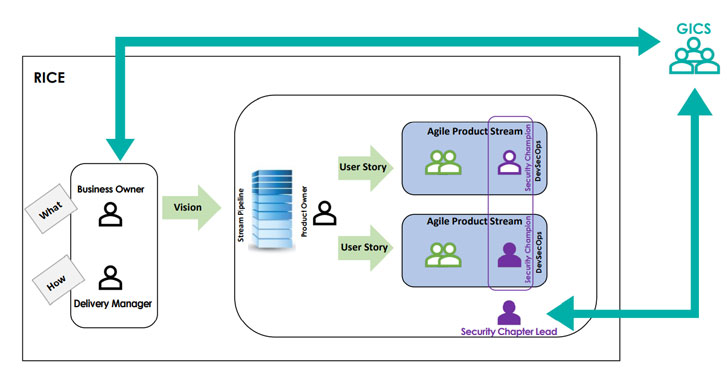
From the security viewpoint, as for every the ‘Security in Agile’ solution, just about every a single of the product teams involved a security winner. They perform with area industry experts and the security chapter lead to coordinate security measures in line with the product or service owner’s designated degrees of risk, getting a consultative technique with the relevant company operator defining the priorities.
API security: Keys to success
Setting up API security on strong collaborative foundations implies that our organization and dev counterparts are equipped to realize far better the worth of security, why we want to do this, and the value of preserving the APIs.
Most importantly, it became obvious that API security was a group endeavor, and that the total staff shared obligation about that region:
From the business finish, considering that APIs are a very important portion of the organization’s IT infrastructure that should be exposed externally, it really is distinct to them that destructive actors would check out to penetrate them by posing as API people. The plan served us recognize that API security is shared in between the solution owner and IT security teams.
From the product or service stop, getting properly-well prepared, learning from experience and applying further layers of defense are key factors in securing APIs.
Additionally, there is a deep shared being familiar with that security ought to be taken into consideration throughout growth, even from the layout stage, and that no product or service really should be introduced without the need of thorough penetration tests.
Master a lot more on how to take demand of the API security lifecycle
Administration buy-in and alignment is possibly just one of the most crucial factors in the correct implementation of API security in an enterprise. Earning absolutely sure that they are aware of the worth of API security is essential in reaching this get-in.
One more essential essential achievements factor is the amount of precision of the detection technology you choose to perform with in your API security journey. The considerably less false positives you get, the improved off you are. In essence, for APIs it implies you can detect actions sequences trying to manipulate the logic and do it in scale.
For security to get the job done, it’s crystal clear that this obligation should not fall on just one particular section, but somewhat be shared by all groups. For the duration of our meetings with the RBI Administration Board, we also focused on the rewards of the Imvision answer and how it enabled us to focus on best vulnerabilities, although understanding in which the practical glitches are to prioritize remediation and help you save assets.
Like with any companion you pick out to perform with, the amount of cooperation is remarkably significant. In standard, the emotion was that the Imvison’s system won’t only offer a effective security mechanism, but also huge knowledge, optimistic travel and responsiveness to our demands.
Located this post fascinating? Observe THN on Facebook, Twitter and LinkedIn to go through a lot more unique material we post.
Some components of this short article are sourced from:
thehackernews.com


 CISA gives civilian agencies two weeks to patch recent security exploits
CISA gives civilian agencies two weeks to patch recent security exploits