More than a dozen destructive packages have been learned on the npm package deal repository given that the start out of August 2023 with capabilities to deploy an open-source information and facts stealer referred to as Luna Token Grabber on systems belonging to Roblox builders.
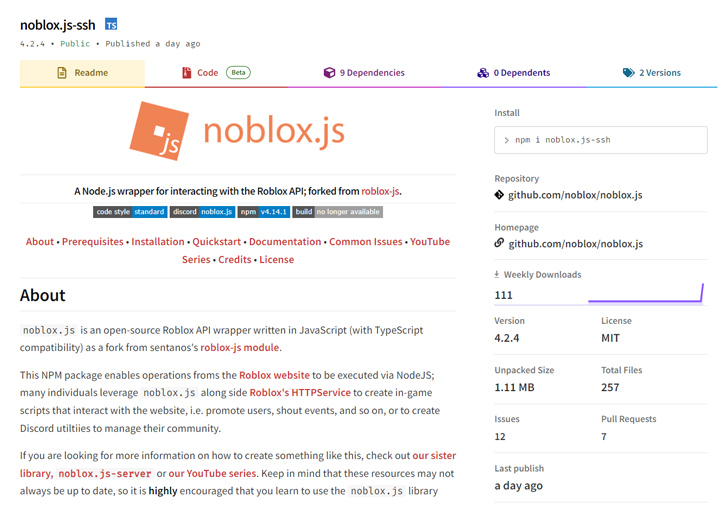
The ongoing campaign, to start with detected on August 1 by ReversingLabs, employs modules that masquerade as the reputable package noblox.js, an API wrapper which is utilized to develop scripts that interact with the Roblox gaming platform.
The program supply chain security enterprise described the activity as a “replay of an attack uncovered two years back” in Oct 2021.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The malicious packages […] reproduce code from the respectable noblox.js deal but increase malicious, information and facts-thieving capabilities,” software menace researcher Lucija Valentić reported in a Tuesday examination.

The offers had been cumulatively downloaded 963 periods before they have been taken down. The names of the rogue offers are as follows –
- noblox.js-vps (versions 4.14. to 4.23.)
- noblox.js-ssh (variations 4.2.3 to 4.2.5)
- noblox.js-secure (variations 4.1., 4.2. to 4.2.3)
Whilst the broad contours of the most up-to-date attack wave keep on being equivalent to the previous a person, it also displays some one of a kind features of its have, notably in the deployment of an executable that delivers Luna Grabber.
The enhancement is one particular of the scarce circumstances of a multi-stage infection sequence uncovered on npm, ReversingLabs reported.
“With destructive campaigns that concentrate on the application supply chain, the difference involving innovative and unsophisticated attacks often comes down to the degree of effort the malicious actors make to disguise their attack and make their destructive deals search authentic,” Valentić pointed out.
The modules, in unique, cleverly conceal their malicious functionality in a independent file named postinstall.js that’s invoked just after set up.
That is for the reason that the real noblox.js package deal also employs a file with the similar title to show a thank you message to its customers together with links to its documentation and GitHub repository.

The bogus variants, on the other hand, make the most of the JavaScript file to confirm to see if the bundle is installed on a Windows equipment, and if so, obtain and execute a 2nd-phase payload hosted on Discord CDN, or alternatively, demonstrate an mistake concept.
ReversingLabs stated that the next-stage continued to evolve with each individual iteration, progressively introducing a lot more performance and obfuscation mechanisms to thwart investigation. The main responsibility of the script is to download Luna Token Grabber, a Python resource that can siphon qualifications from web browsers as perfectly as Discord tokens.
Having said that, it seems that the threat actor guiding the npm marketing campaign appears to have opted only to harvest method information from victims utilizing a configurable builder made readily available by the writer(s) guiding Luna Token Grabber.
This is not the very first time Luna Token Grabber has been spotted in the wild. Earlier this June, Trellix disclosed particulars of a new Go-dependent data stealer identified as Skuld that overlaps with the malware pressure.
“It highlights still yet again the craze of destructive actors working with typosquatting as a approach to fool developers into downloading malicious code under the guise of in the same way named, respectable packages,” Valentić stated.
Located this short article appealing? Observe us on Twitter and LinkedIn to study additional special content material we write-up.
Some areas of this short article are sourced from:
thehackernews.com


 CISOs Tout SaaS Cybersecurity Confidence, But 79% Admit to SaaS Incidents, New Report Finds
CISOs Tout SaaS Cybersecurity Confidence, But 79% Admit to SaaS Incidents, New Report Finds